Growing pains: How to evolve and scale inherited security processes
If you’re working with a patchwork of security tools and workflows, you’re not alone. As your business grows, manual processes and siloed tools can slow you down—and increase risk.
This tactical guide helps solo security practitioners and small teams take control. Learn how to assess what you’ve inherited, prioritize what matters, and build a scalable, resilient security program.
What’s inside:
- Step-by-step guidance on how to audit and improve your processes
- A scoring system to identify high-impact updates
- Tactics to centralize, automate, and streamline workflows
- Tips to align with cross-functional teams and scale with confidence
Growing pains: How to evolve and scale inherited security processes
If you’re working with a patchwork of security tools and workflows, you’re not alone. As your business grows, manual processes and siloed tools can slow you down—and increase risk.
This tactical guide helps solo security practitioners and small teams take control. Learn how to assess what you’ve inherited, prioritize what matters, and build a scalable, resilient security program.
What’s inside:
- Step-by-step guidance on how to audit and improve your processes
- A scoring system to identify high-impact updates
- Tactics to centralize, automate, and streamline workflows
- Tips to align with cross-functional teams and scale with confidence
The Agentic Trust Platform powering security for over [customer_count] customers






It’s all here
Compliance, risk, and proof. All in the #1 Agentic Trust Platform.
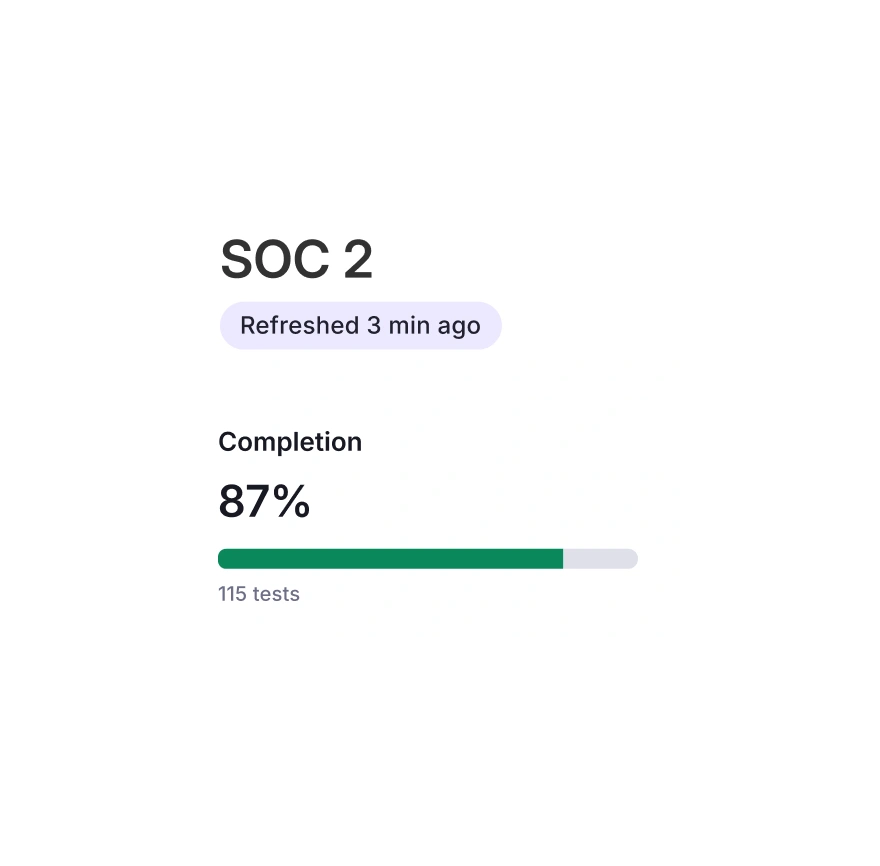
Compliance
Get and stay compliant with automation and continuous monitoring.
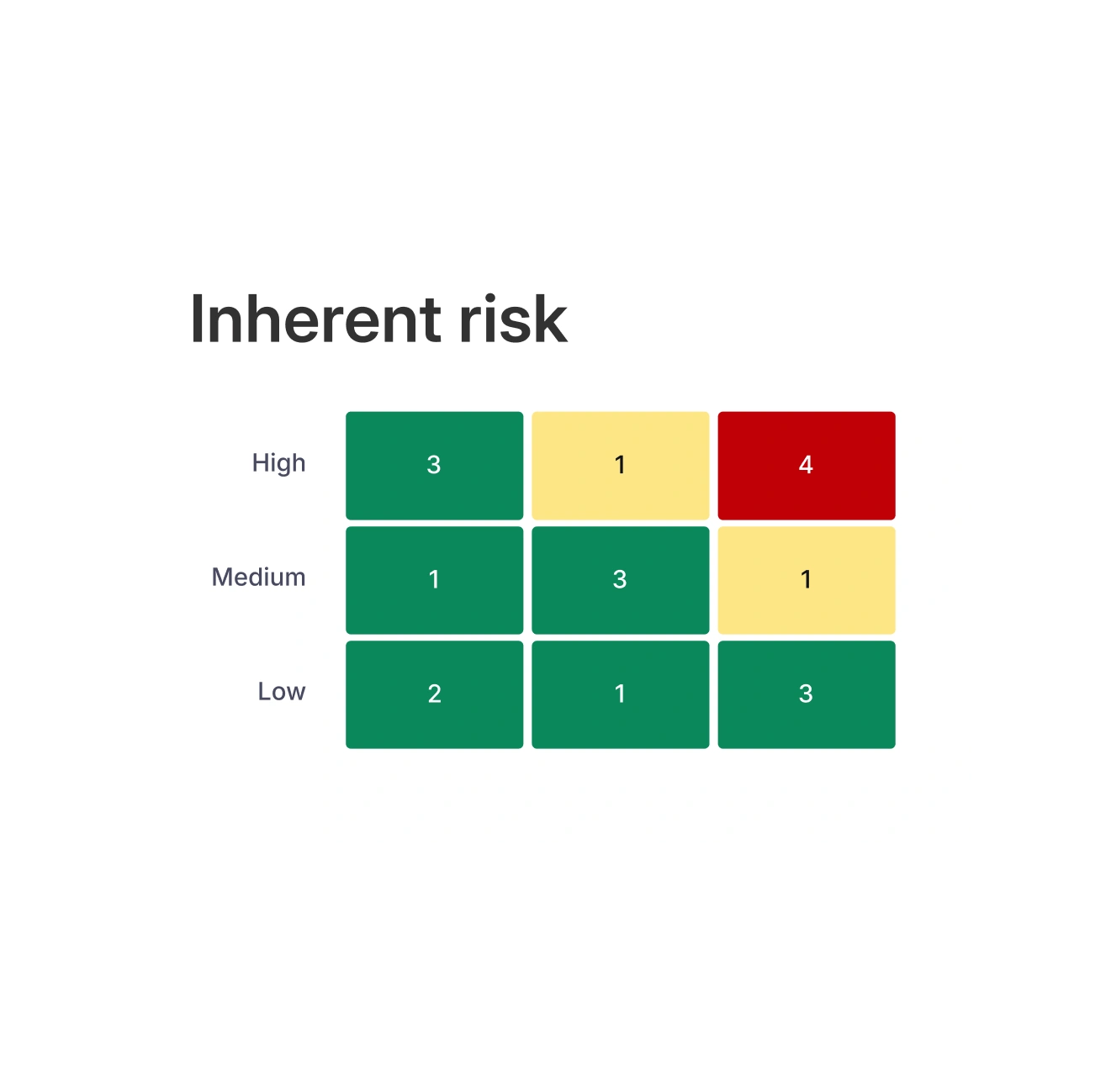
Risk
See and manage risk in one place.
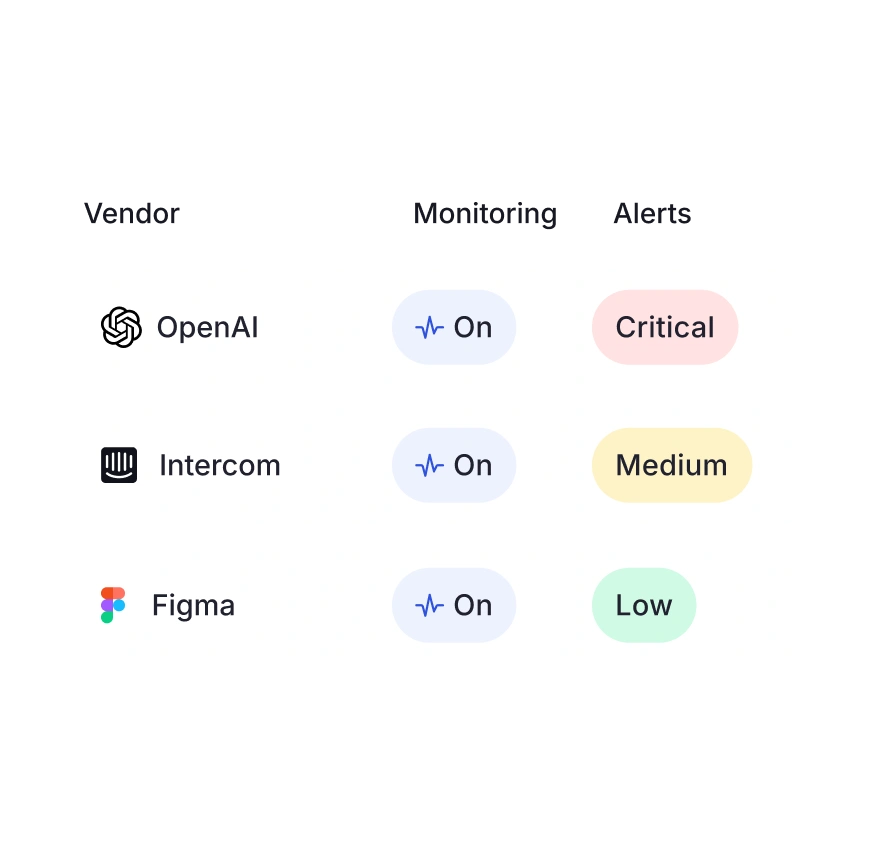
Third Party Risk
Stay on top of vendor risk with Vanta's Agent for TPRM.
Audit
Audit prep with ease, no spreadsheets required.
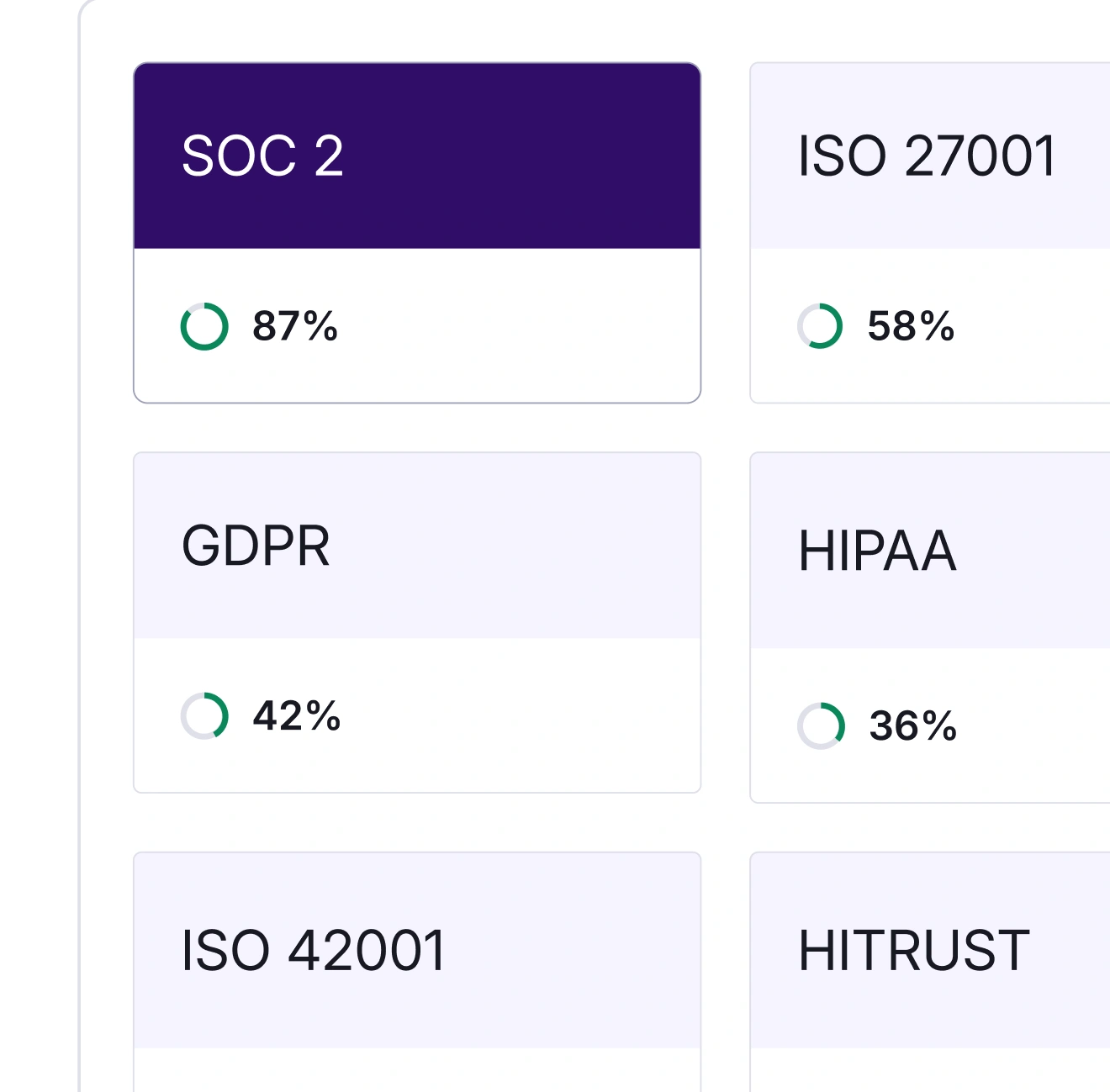
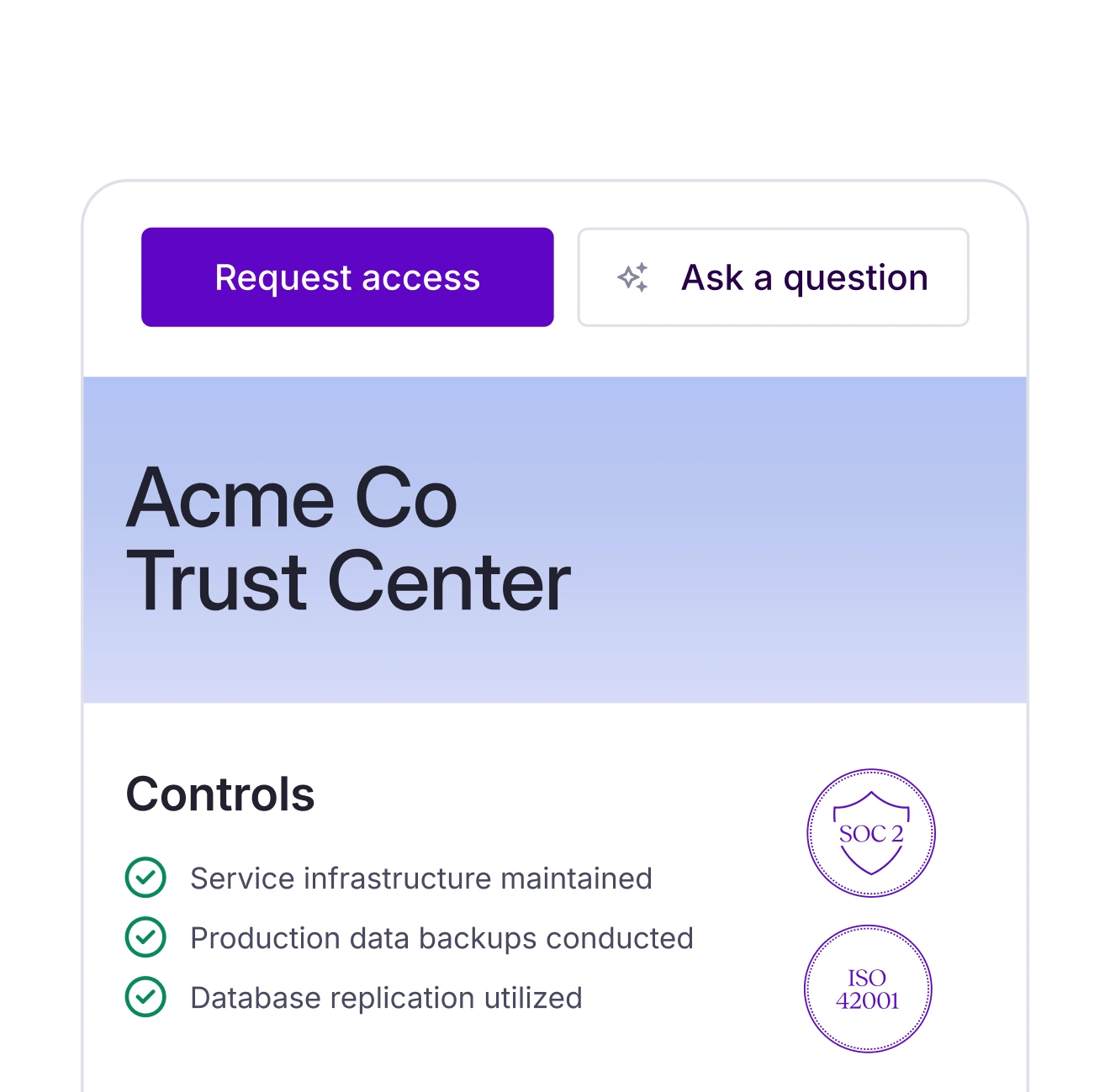
Trust Center
Showcase your security posture in real time.
Questionnaire Automation
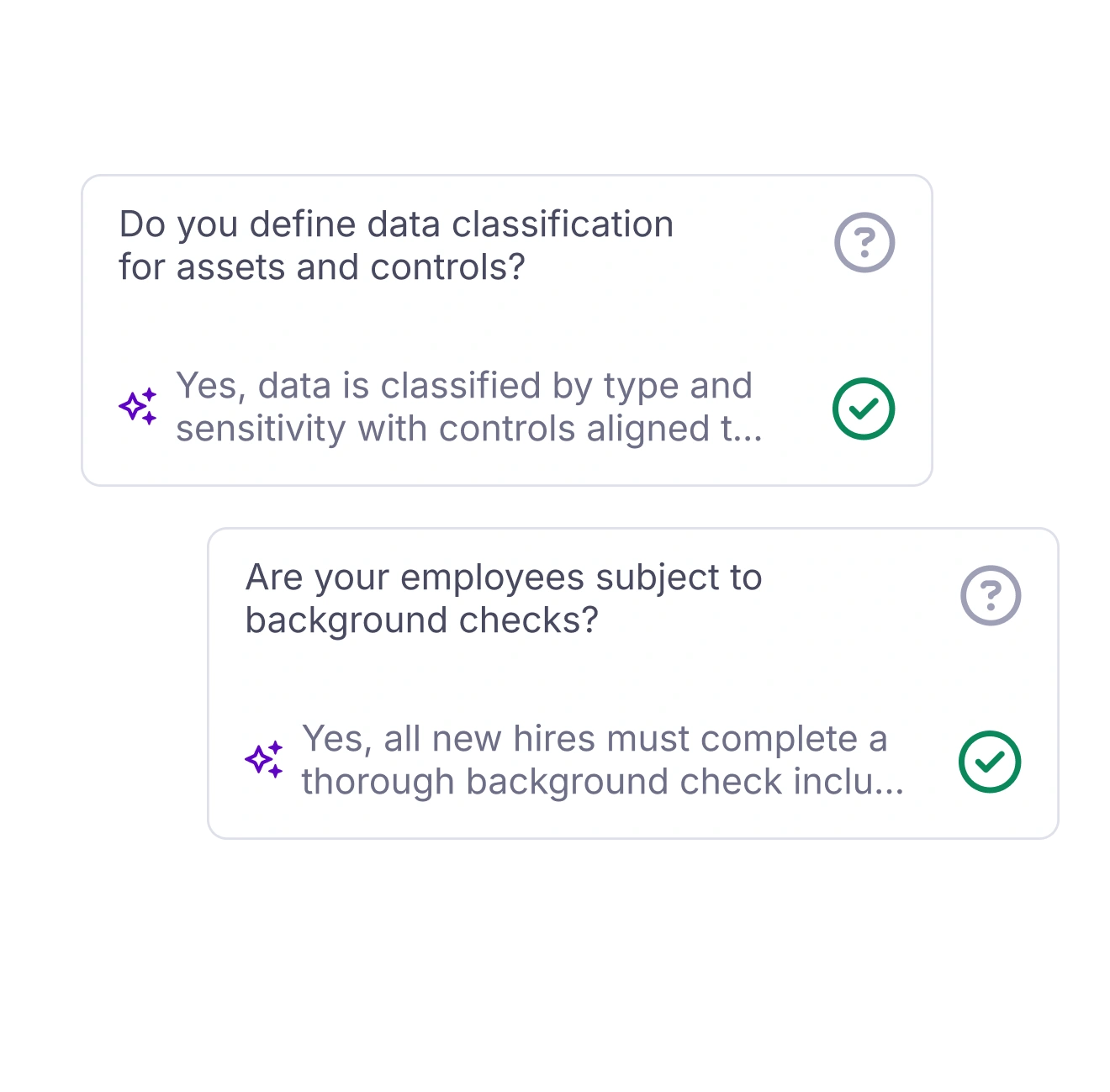
Let the Vanta Agent draft your questionnaire responses.
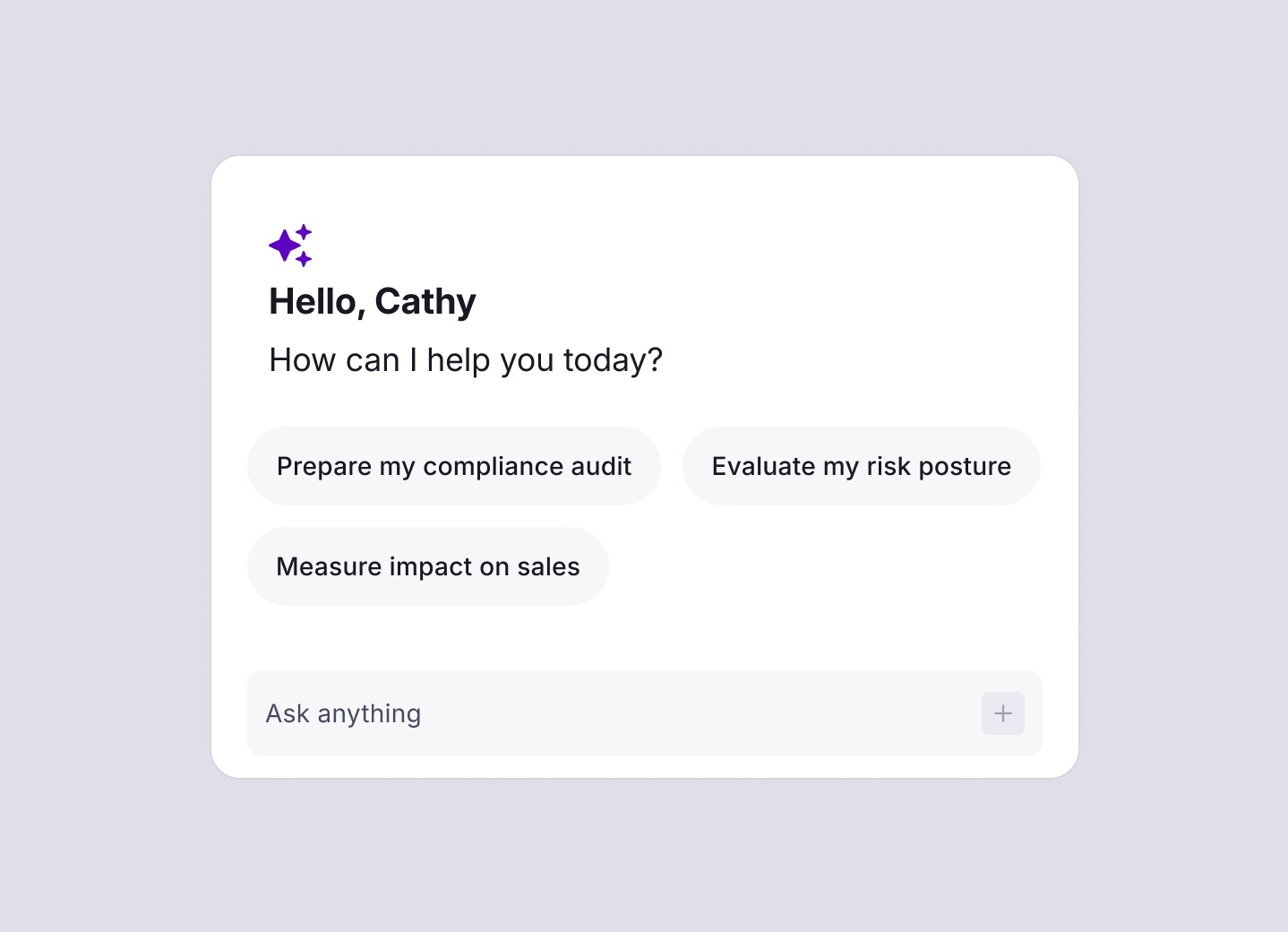
The Vanta Agent: your 24/7
GRC engineering team
The Vanta agent is everywhere you need it to be—drafting policies, completing your questionnaires, calling out issues, and generally making you wonder what you did before it existed.
Built for you
Whether you're managing a complex program or just getting started.

Startups
Are you a startup founder in need of a SOC 2 yesterday, but lacking time and resources? We'll automate the process and get you big-deal-ready.




Mid-market
Security leaders, keep scaling fast—no need for more headcount. Vanta automates and continuously monitors your program, so you can do more with the team you have.




Enterprise
Vanta combines compliance, risk, and proof, right where CISOs and security leaders need them—clearly visible and all on one platform.



Growing pains: How to evolve and scale inherited security processes
If you’re working with a patchwork of security tools and workflows, you’re not alone. As your business grows, manual processes and siloed tools can slow you down—and increase risk.
This tactical guide helps solo security practitioners and small teams take control. Learn how to assess what you’ve inherited, prioritize what matters, and build a scalable, resilient security program.
What’s inside:
- Step-by-step guidance on how to audit and improve your processes
- A scoring system to identify high-impact updates
- Tactics to centralize, automate, and streamline workflows
- Tips to align with cross-functional teams and scale with confidence









%201%20(1).svg)


%201.svg)
