How to build trust and unlock growth checklist
Your checklist for turning security into a competitive advantage
Is security blocking your business from growing?
Trust is a critical part of any deal. Customers, big and small, need to know how you’ll protect their data before they can do business with you. If you’re not prepared, this can lead to lengthy questionnaires, long security reviews, and awkward sales conversations.
Instead of playing defense, learn how to use your security posture as a competitive advantage by positioning security as one of your strengths. Our five-step checklist helps you establish a security program that unlocks deals by building trust.
Read our checklist to get started:
- Using security to build trust and close more deals, faster.
- Streamlining all your security requests and automating your manual security processes.
- Extending trust beyond the four walls of your business with vendor risk management.

How to build trust and unlock growth checklist
Your checklist for turning security into a competitive advantage
Is security blocking your business from growing?
Trust is a critical part of any deal. Customers, big and small, need to know how you’ll protect their data before they can do business with you. If you’re not prepared, this can lead to lengthy questionnaires, long security reviews, and awkward sales conversations.
Instead of playing defense, learn how to use your security posture as a competitive advantage by positioning security as one of your strengths. Our five-step checklist helps you establish a security program that unlocks deals by building trust.
Read our checklist to get started:
- Using security to build trust and close more deals, faster.
- Streamlining all your security requests and automating your manual security processes.
- Extending trust beyond the four walls of your business with vendor risk management.

The Agentic Trust Platform powering security for over [customer_count] customers






It’s all here
Compliance, risk, and proof. All in the #1 Agentic Trust Platform.
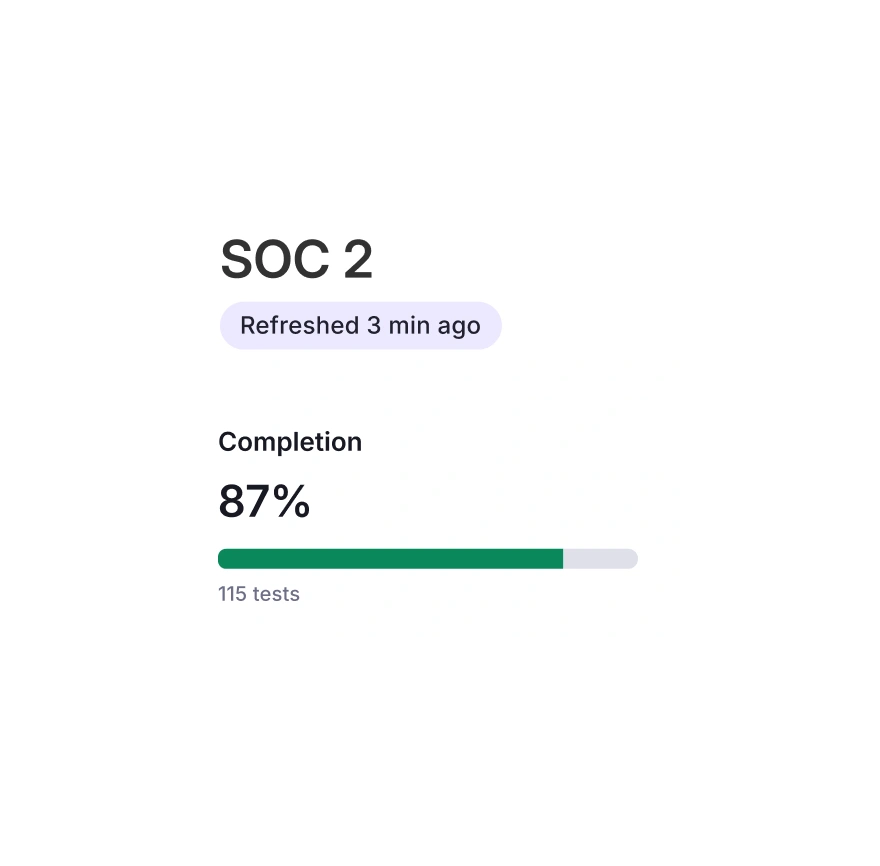
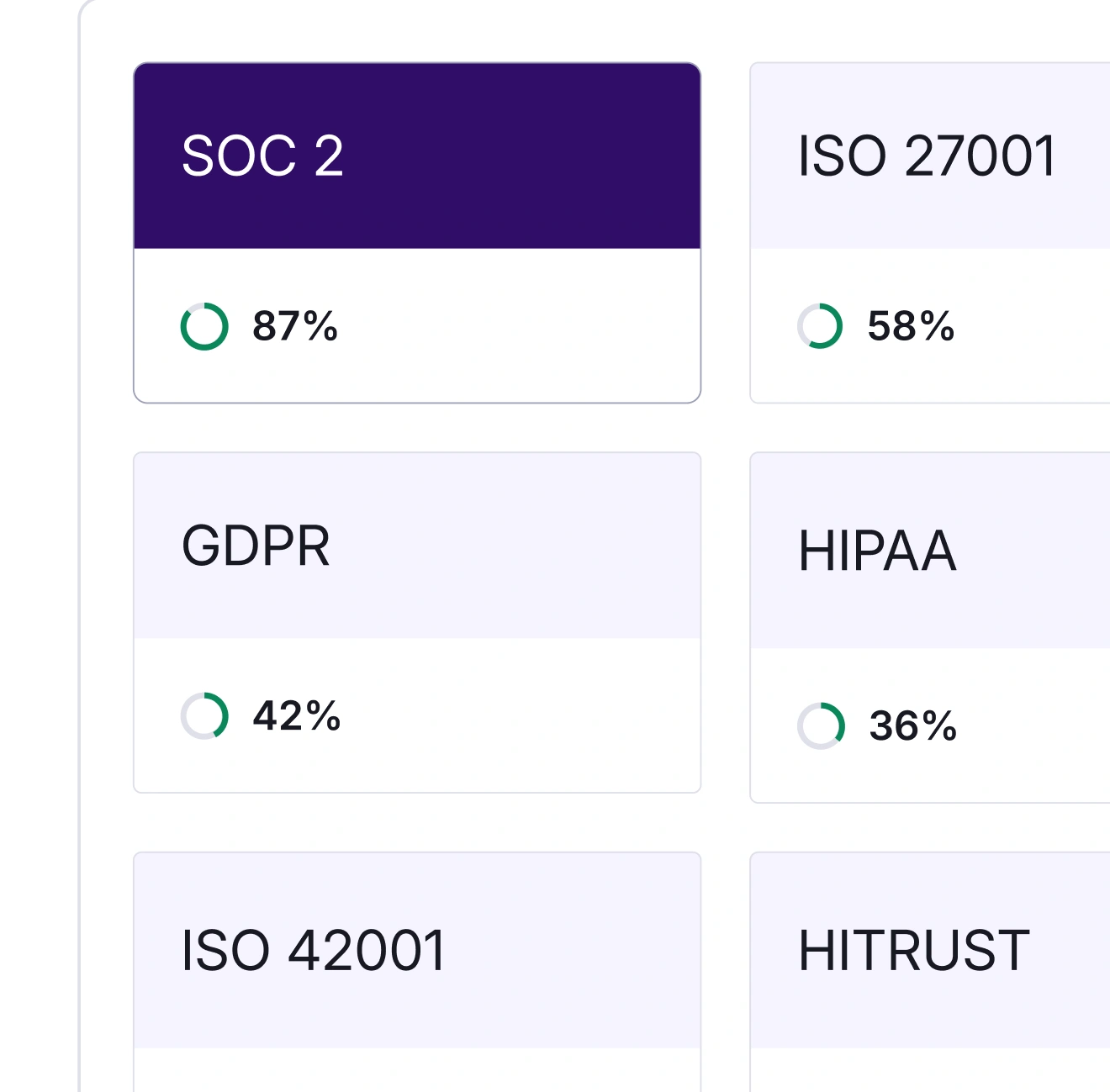
Compliance
Get and stay compliant with automation and continuous monitoring.
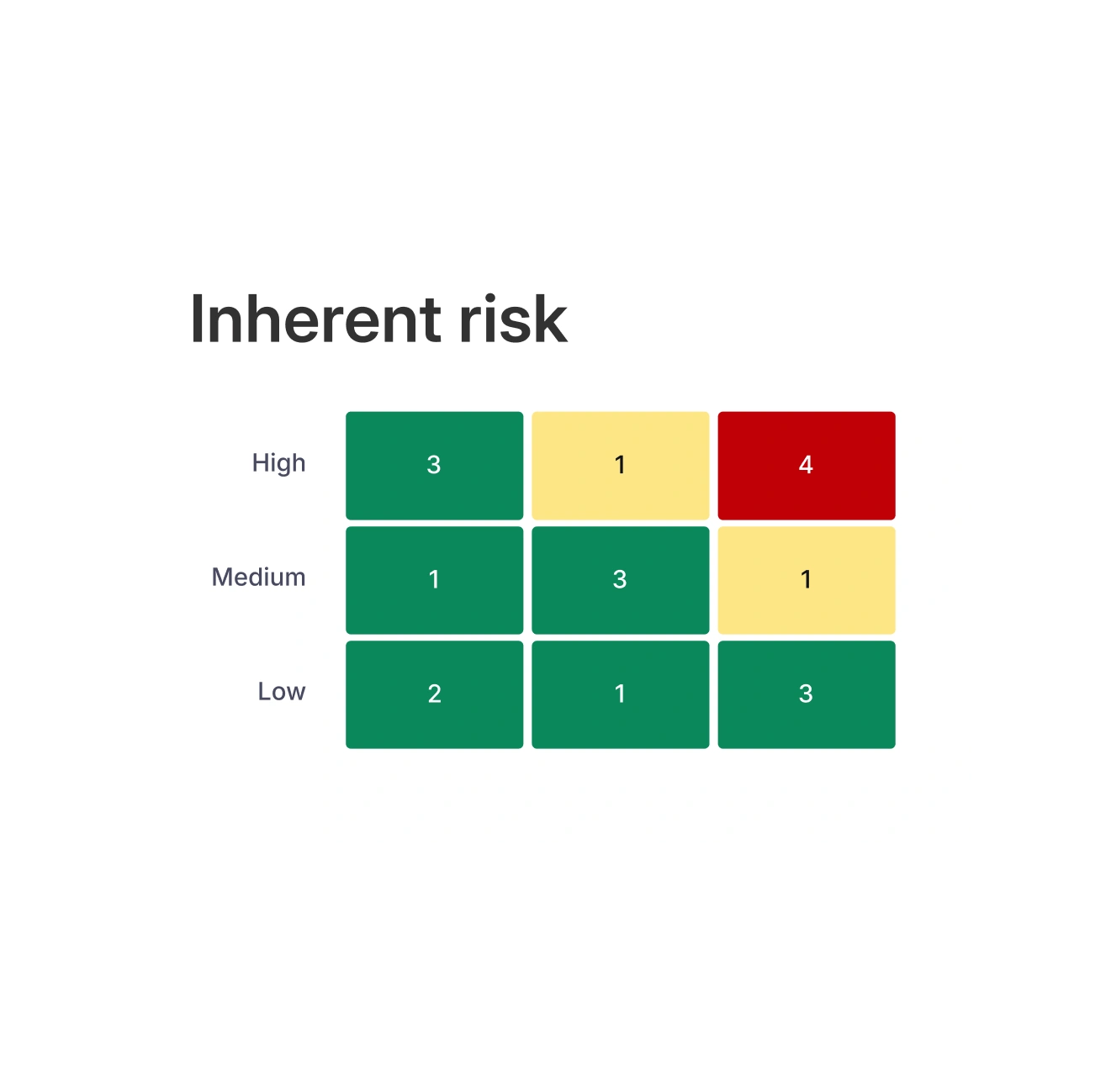
Risk
See and manage risk in one place.
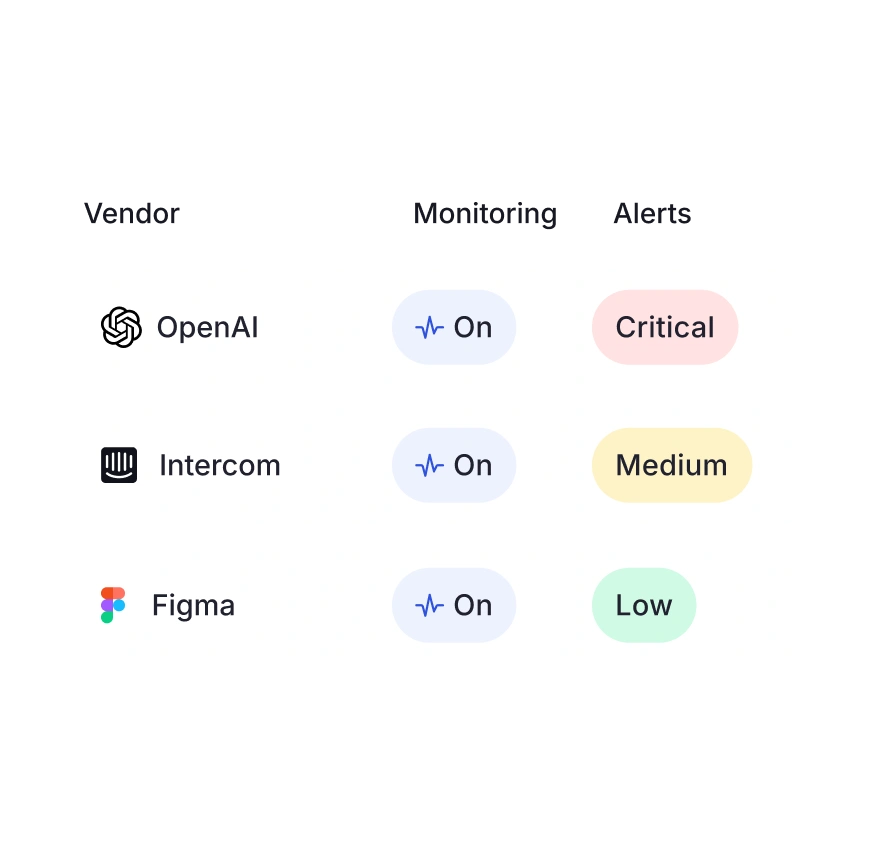
Third Party Risk
Stay on top of vendor risk with Vanta's Agent for TPRM.
Audit
Audit prep with ease, no spreadsheets required.
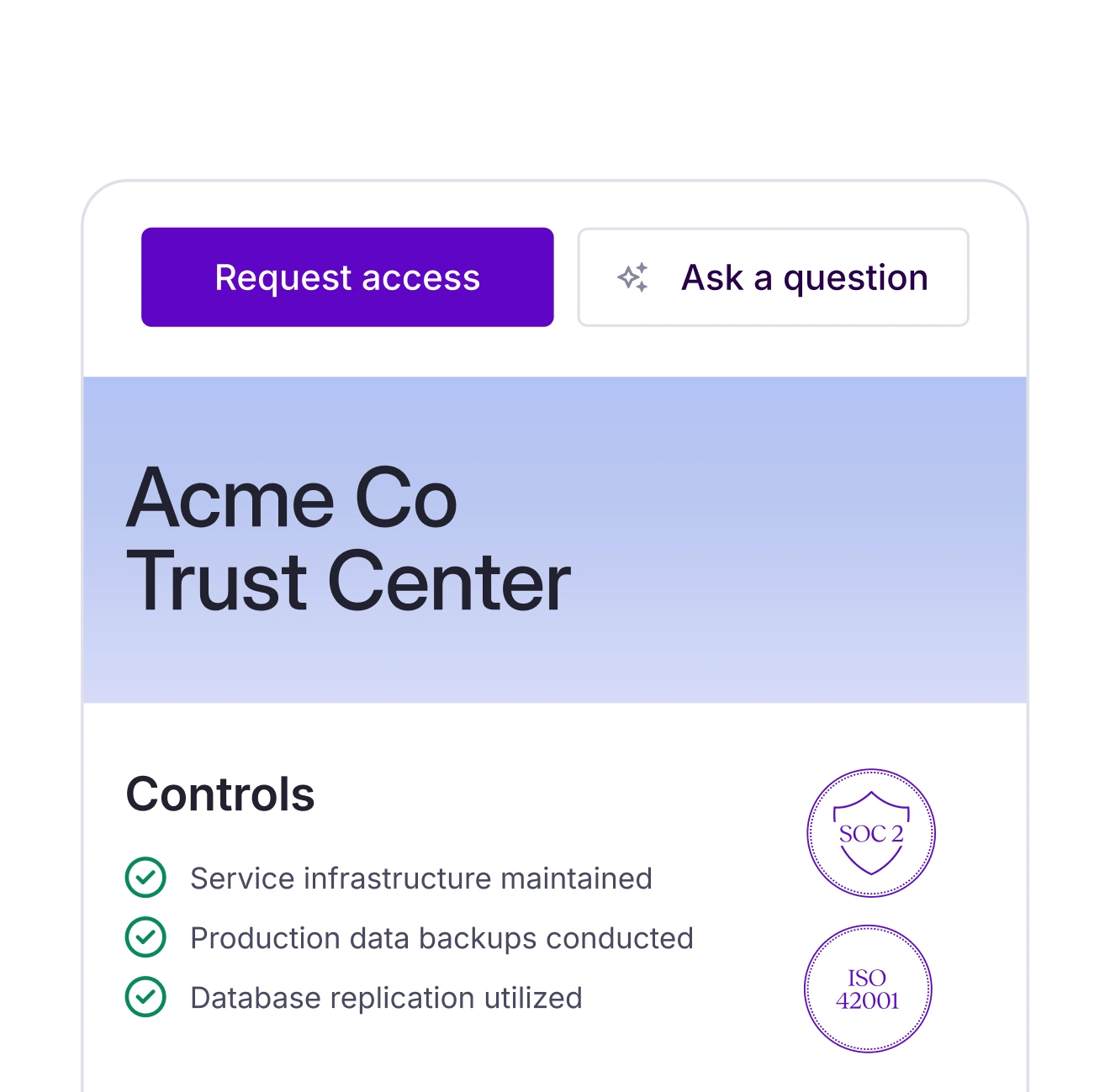
Trust Center
Showcase your security posture in real time.
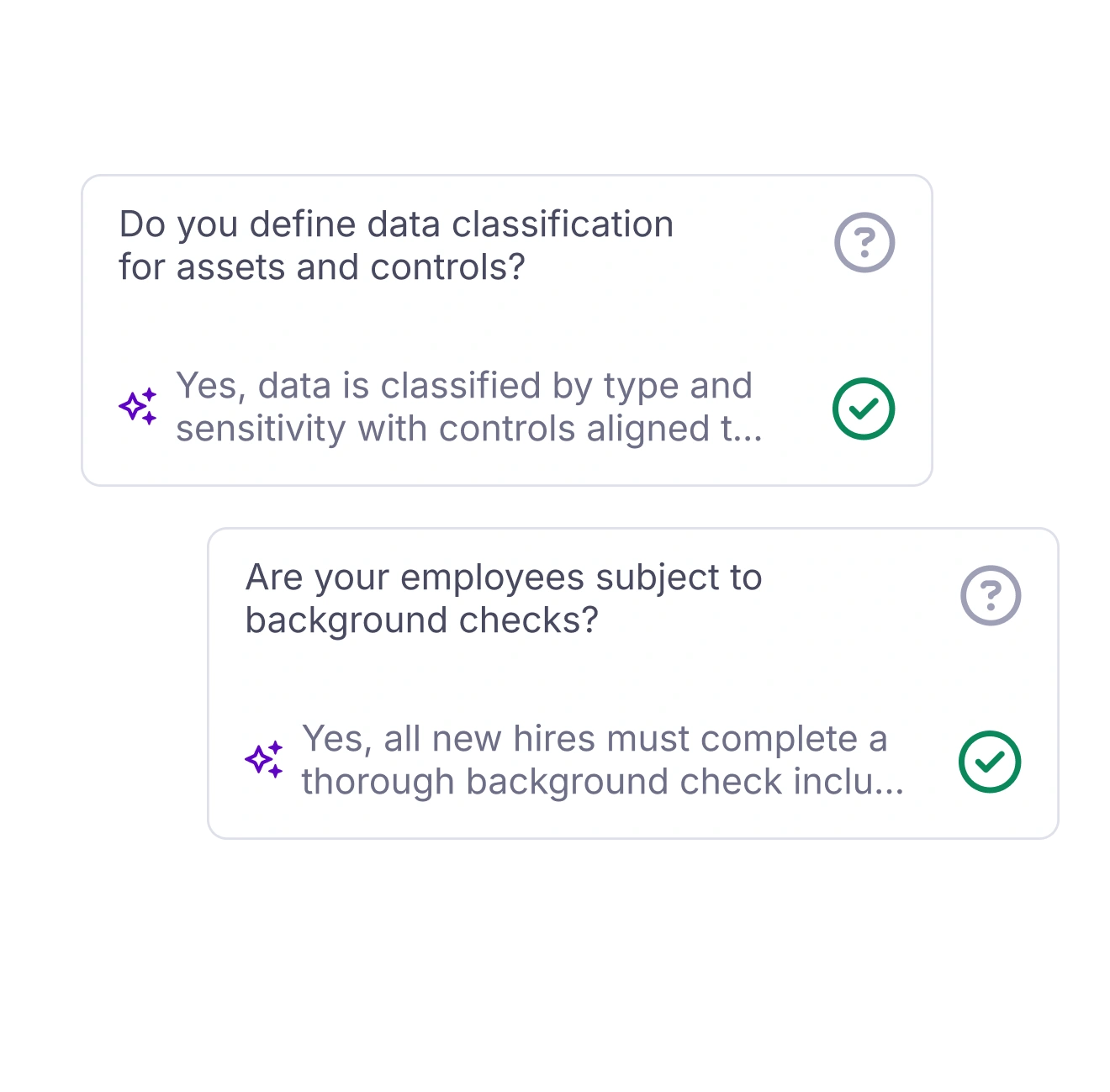
Questionnaire Automation
Let the Vanta Agent draft your questionnaire responses.
The Vanta Agent: your 24/7
GRC engineering team
The Vanta agent is everywhere you need it to be—drafting policies, completing your questionnaires, calling out issues, and generally making you wonder what you did before it existed.
Built for you
Whether you're managing a complex program or just getting started.

Startups
Are you a startup founder in need of a SOC 2 yesterday, but lacking time and resources? We'll automate the process and get you big-deal-ready.




Mid-market
Security leaders, keep scaling fast—no need for more headcount. Vanta automates and continuously monitors your program, so you can do more with the team you have.




Enterprise
Vanta combines compliance, risk, and proof, right where CISOs and security leaders need them—clearly visible and all on one platform.



How to build trust and unlock growth checklist
How to build trust and unlock growth checklist
Your checklist for turning security into a competitive advantage
Is security blocking your business from growing?
Trust is a critical part of any deal. Customers, big and small, need to know how you’ll protect their data before they can do business with you. If you’re not prepared, this can lead to lengthy questionnaires, long security reviews, and awkward sales conversations.
Instead of playing defense, learn how to use your security posture as a competitive advantage by positioning security as one of your strengths. Our five-step checklist helps you establish a security program that unlocks deals by building trust.
Read our checklist to get started:
- Using security to build trust and close more deals, faster.
- Streamlining all your security requests and automating your manual security processes.
- Extending trust beyond the four walls of your business with vendor risk management.









%201%20(1).svg)


%201.svg)
