Agentic Third Party Risk Management
Vanta's TPRM Agent automatically discovers vendors, accelerates assessments, and monitors third-party risk.

The Third Party Risk Management solution for leading businesses





Cut risk assessment time by 50%
Vanta automatically pulls findings from your vendors SOC2 reports, DPAs, and questionnaires so your team focuses on high-stakes decisions, not paperwork.

Your always-on TPRM Agent
The Agent automatically runs the end-to-end assessment lifecycle. Eliminate manual follow-ups, guide vendors, and collect documentation, surfacing real risk exposure directly in your GRC program.
faster vendor evidence collection time
productivity gains after adopting TPRM 1
Continuous risk detection
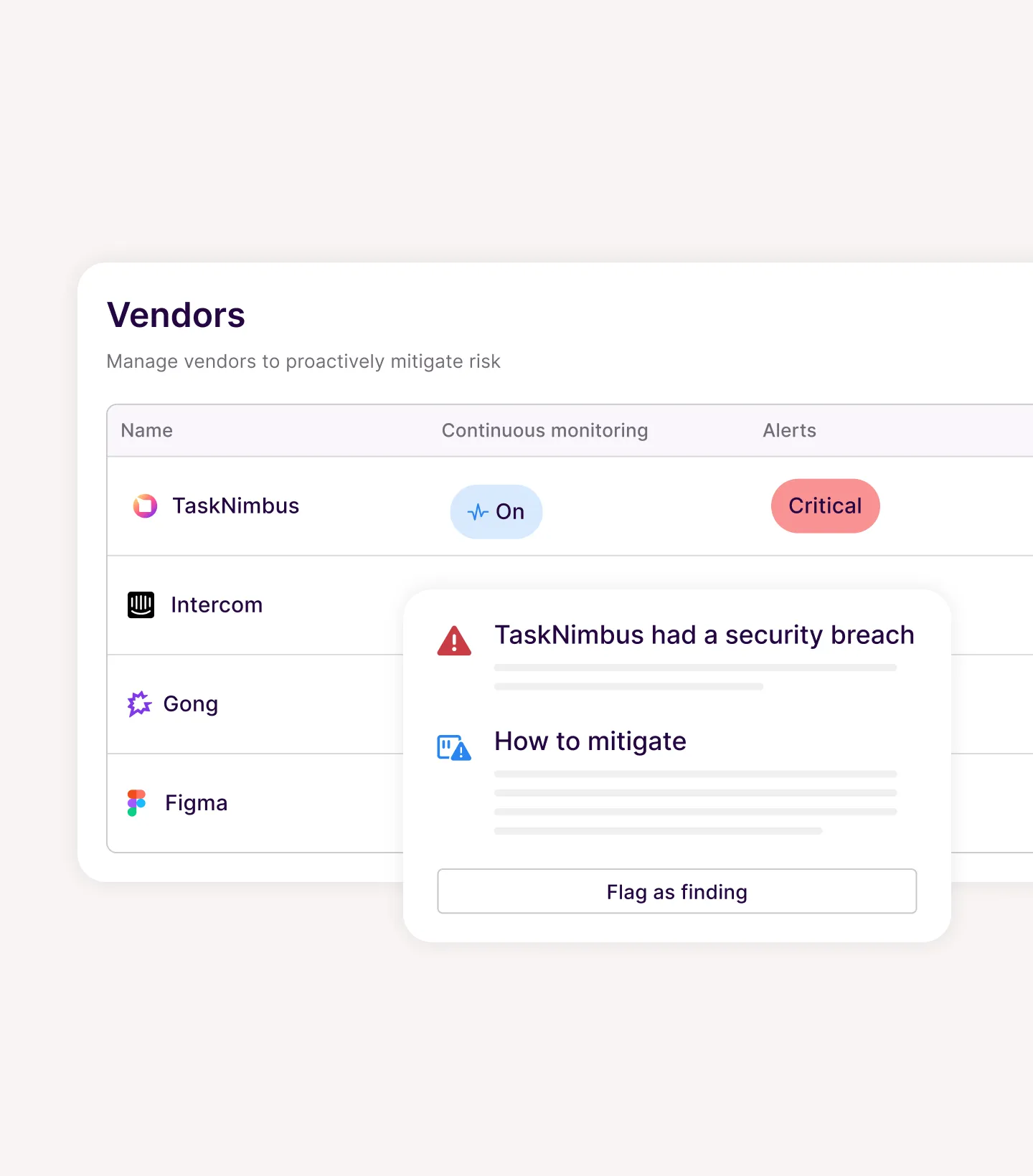
Eliminate blind spots after the risk assessment ends. Vanta’s TPRM Agent continuously monitors your vendor landscape for breaches, emerging threats and material changes. When risks arise, the Agent automatically drafts tailored remediation plans to protect your contractual integrity.
A unified view of all your risks
Vendor findings feed directly into your risk register and compliance posture — giving your team one unified view of risk. No fragmented tools, no context-switching. Detect and remediate issues with speed.

How the TPRM Agent works
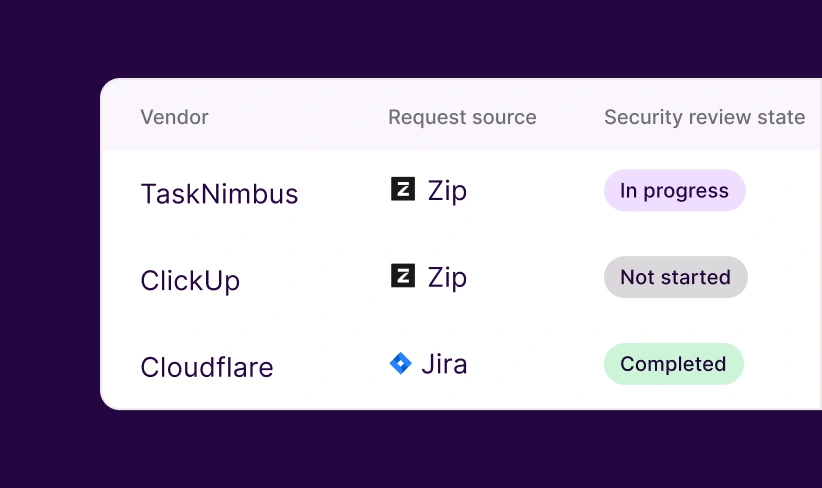
Identifies Shadow IT & AI
Discovers newly adopted vendors and integrates with your existing procurement systems to eliminate shadow IT and AI blind spots.

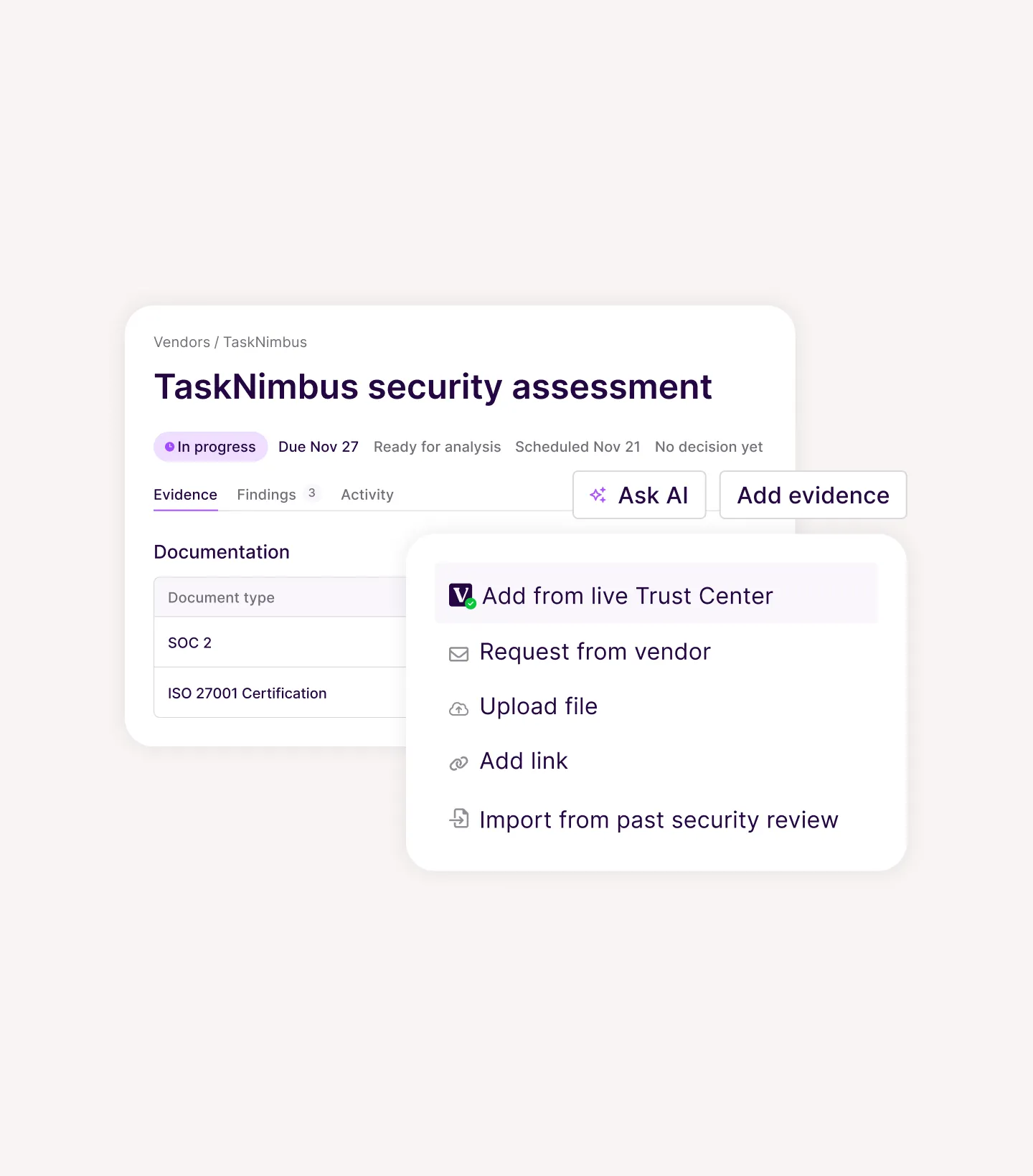
Retrieves evidence
Retrieves verified documentation directly from first- and third-party Trust Centers to build a high-fidelity system of record without manual intervention.

Extracts risks
Identifies high-stakes SLAs, DPAs, and custom security terms in SOC 2 reports to surface real exposure in seconds.

Enforces custom standards
Applies your specific risk tiers and scoring logic across every assessment to ensure vendor compliance reflects your unique standards.

Drives vendor responses
Manages document requests and follow-ups with persistent reminders to keep your program moving forward on autopilot.
Monitors 24/7
Scans your vendor landscape for material changes and breaches to draft tailored remediation plans that protect your contractual integrity.
Your risk program. Your rules. And the Vanta AI Agent does the busy work for you.
Available as a standalone product or as an add on to your existing Vanta plan, Third Party Risk Management helps you unlock even greater value from Vanta.






Learn more about Third Party Risk Management
.png)
Live Demo: Navigating Third-Party Risk Through Vanta’s Vendor Risk Management
Watch on-demand for a live demo that showcases Vanta’s Vendor Risk Management solution. Well share how we can help automate and streamline security reviews so that you can spend less time on repetitive work and more time strengthening your security posture.
The best TPRM software for 2026
Discover the best third-party risk management software solutions for 2026.

How to minimize third-party risk with vendor management
Get insights and best practices from security & compliance experts on how to manage third-party vendor risk in this free guide.
FAQ
Vanta replaces spreadsheets with a centralized vendor inventory, automated vendor discovery via integrations, customizable intake forms for procurement requests, AI-powered security reviews that auto-collect and analyze evidence, automated follow-ups and reminders to vendors, and real-time dashboards—cutting review time by up to 50%.
IDC research shows Vanta delivers a 526% three-year ROI with a 3-month payback. TPRM teams saw 54% productivity gains. Organizations managing 50 vendors can save approximately $81K annually through automated discovery, AI-powered reviews, and continuous monitoring—reducing vendor review time by up to 80%.
Yes. Vanta offers fully customizable risk rubrics—you can add, remove, or adjust metrics and their weightings. Pre-configured categories include data types, business criticality, integration access, and communication scope. Vendors are automatically scored based on your criteria, and you can tailor thresholds to match your organization's risk appetite.
Third party risk management (TPRM) software helps organizations evaluate, monitor, and manage security risks introduced by vendors. It works by centralizing vendor inventories, automating risk assessments through questionnaires and AI, assigning risk scores, and continuously monitoring for threats—ensuring vendors meet your security and compliance standards throughout the relationship.
Vanta streamlines vendor onboarding with customizable intake forms, automated risk scoring at request, and procurement workflows that guide approvals. AI auto-collects evidence and accelerates security reviews. For offboarding, Vanta tracks vendor status changes and maintains audit-ready documentation of all decisions made throughout the vendor lifecycle.
TPRM software identifies cybersecurity risks (vulnerabilities, breaches), data privacy risks (data handling, residency), business continuity risks (vendor outage impact), compliance risks (regulatory alignment), fourth-party/supply chain risks (sub-processor exposure), and integration access risks (read/write permissions). Vanta monitors all these continuously with real-time alerts.
- IDC White Paper, The Business Value of Vanta (doc #US52656824), January 2025. Sponsored by Vanta.










%20headshot.png)




