Share this article

Building bridges: How Vanta helps EMEA-based companies navigate complex EU regulations
Accelerating security solutions for small businesses Tagore offers strategic services to small businesses. | A partnership that can scale Tagore prioritized finding a managed compliance partner with an established product, dedicated support team, and rapid release rate. | Standing out from competitors Tagore's partnership with Vanta enhances its strategic focus and deepens client value, creating differentiation in a competitive market. |
Companies that want to unlock the door to international revenue have a lot of hurdles to jump. While there are numerous milestones along the way, few blow wind in the sails like security compliance—especially when it’s prioritized as early as possible.
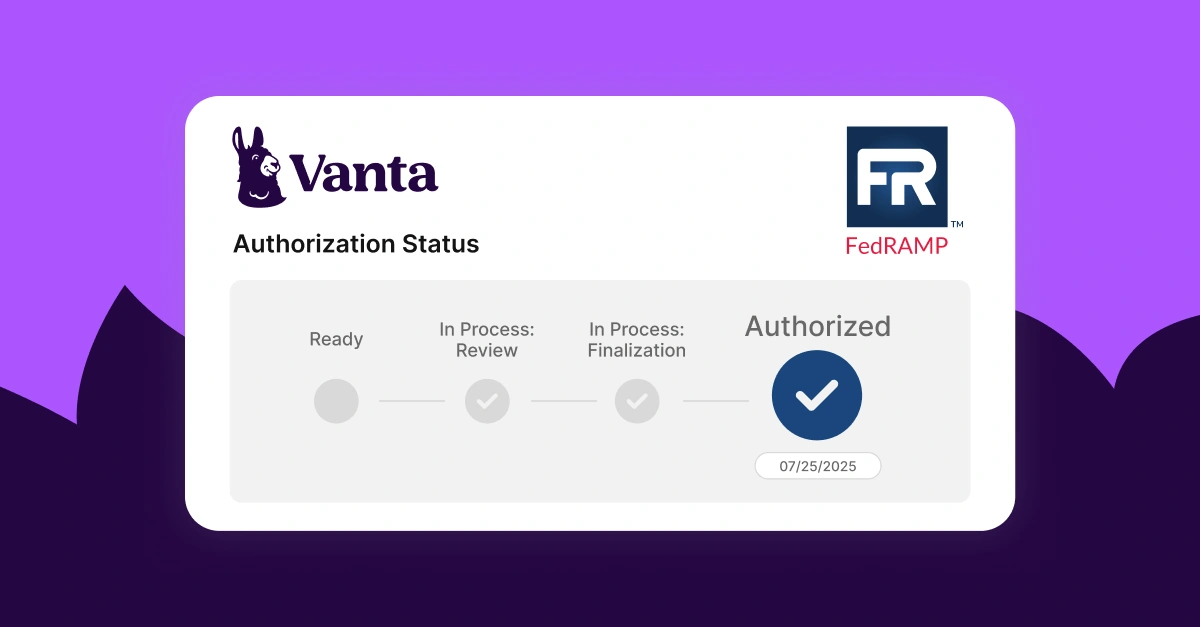
Depending on the market, companies have to possess specific security certifications and privacy standards before they even get a seat at the table. This is why it’s critical to prioritize compliance as soon as possible. Organizations that wish to expand into international markets will encounter compliance checkpoints such as GDPR and ISO 27001. Companies that wish to target the US will also need to solve for standards such as SOC 2 and CCPA.
Before Vanta, the cost of gaining access to new territories via compliance was unrealistic. Vanta eliminates those barriers and levels the playing field by making it easy for companies around the globe to prove security with compliance. Vanta’s customer-centric approach helps companies define their needs so they can scale with confidence. In this article, we’ll take a look at how three Vanta customers prioritized compliance frameworks early, enabling them to enter an exciting new phase of growth.
Causaly ramps up international biotech security with ISO 27001
Founded in 2018, Causaly’s machine-learning platform discovers relationships and patterns within a vast archive of health data and research. Its technology is paving the way for world-renowned health specialists to scientifically consume research in a way like never before. Causaly’s AI can scan all biomedical literature—ever published—in seconds. But housing highly-sensitive health data comes with much responsibility.
Due to the nature of their product and business, Causaly took a proactive approach to compliance early on. The lean, yet expanding company needed a compliance solution that offers reliable, continuous automation. As a new company, Causaly also wanted a trustworthy voice to guide them through the compliance process.
Causaly partnered with Vanta to pursue ISO 27001 certification—one of the most thorough compliance standards available. ISO certification demonstrates Causaly’s dedication to protecting customers and complying with international requirements. It also enables the company to enter new markets with confidence.
With offices in Athens and London, Causaly is preparing to bring its one-of-a-kind product to more corners of the world. In a blog post announcing their certification, Causaly reveals the strategy behind the decision to pursue ISO 27001:
“Implementing ISO’s requirements assure us that our security protocols are ironclad. Certification is the green light that gives us the confidence to scale as fast as possible, with our quality intact.”
In 2021, Causaly raised $17 million in Series A investments from Index Ventures, Marathon, Pentech and EBRD. With a valuable product already used by large pharmaceutical companies, Causaly will leverage investments to grow its team, enter into new markets, and pursue more compliance standards such as SOC 2, GDPR, and possibly CCPA.
incident.io invests in SOC 2 compliance to plant a flag in US
Resilience in the digital era is paramount. When bad things do happen, companies that have a plan fare better than those that don’t. incident.io provides world-class incident management software which is conveniently managed right in Slack. The platform provides automated guidance, tailored processes, and analytics-based insights to prevent a slew of mishaps.
CPO and Co-founder Chris Evans developed the core software as a way to remediate manual workflows for his team while working at Monzo. Since starting incident.io, hypergrowth has kept the company in the fast lane.
In July 2022, incident.io raised $28.7 million in a Series A round led by Index Ventures. In total, incident.io accumulated $34.2 million. So what’s an already-successful UK-based company doing with the new funds? Driving international expansion into the US with SOC 2 compliance.
Early in the company’s history, Chris recognized the need for SOC 2, not only to protect sensitive customer data, but also as a way to scale. In order to achieve SOC 2 compliance, incident.io sought an expert partner who could provide an affordable platform with plug-n-play automation.
“A platform like Vanta can easily plug into our system. Being a young company with little infrastructure, it felt like easy mode,” Chris says. “Honestly, the biggest value that I get from Vanta is knowing that when I need to annually renew my SOC 2, I have almost no concern. The evidence is all there and it’s not an ongoing task—it’s just done.”
incident.io is actively pursuing new industries, bigger clients, and more product offerings. Looking ahead, Chris and the incident.io team are looking at ISO 27001 and HIPAA in response to interested prospects. incident.io now has offices in New York with hopes to expand even further.
Hook uses SOC 2 compliance as a revenue engine from the start
Since customer success became a “must-have” in recent years, many CS platforms have hit the market. But not many have infused machine learning into their CS dashboard until now. Meet Hook—an automated customer success platform that analyzes customer data and predicts important information such as health scores, revenue, and retention.
In 2020, Hook’s first year of business, the company prioritized three initiatives—developing a platform, hiring software engineers, and becoming SOC 2 compliant. After six weeks of being a company, Hook partnered with Vanta to tackle SOC 2 compliance.
“We knew that SOC 2 was something a lot of customers would request because of the data transfer our platform requires,” says Head of Business Operations Amelia Wallace Scott. A young UK company wielding a SOC 2 report has far fewer obstacles when it comes to entering the US market. With an additional office now in New York, Hook is able to leverage SOC 2 compliance as a competitive differentiator in The States.
Integrating compliance early into the architecture of the business also presents significant benefits. Internal security organically remains intact as infrastructure expands and new products are created. “Vanta reduces clutter, noise, and uncertainty,” Amelia says. For Hook, a little work upfront enables continuous, low-lift compliance moving forward. “It’s something we’ll stick with as we’re growing.” As the platform continues to generate interest, Hook plans to add ISO 27001 certification to its compliance program.
Play defense and offense by investing in compliance
The obvious benefits of investing in compliance are mitigating risk, avoiding fines, and protecting customers—defending and safeguarding your organization. But there’s another side to compliance that SaaS leaders across the world are discovering.
Compliance is a strong market differentiator—an offensive advantage for companies that need to unlock revenue in new markets. As companies seek new growth opportunities by appealing to mid-market, enterprise, or international prospects, proof of security is invaluable.
Companies that prioritize security and compliance before others will be in a position to accelerate international expansion and tap into new revenue streams. A company may have an exceptional product, a talented workforce, and even international consultants, but overseas expansion may never get off the ground without proof of security.





FEATURED VANTA RESOURCE
The ultimate guide to scaling your compliance program
Learn how to scale, manage, and optimize alongside your business goals.















.svg)






-p-1600.jpg.webp)


.svg)
.svg)


