Share this article

VantaCon 2022: Managing risk and unlocking growth with trust
Accelerating security solutions for small businesses Tagore offers strategic services to small businesses. | A partnership that can scale Tagore prioritized finding a managed compliance partner with an established product, dedicated support team, and rapid release rate. | Standing out from competitors Tagore's partnership with Vanta enhances its strategic focus and deepens client value, creating differentiation in a competitive market. |
VantaCon 2022 brought together the most innovative minds in security and compliance for a half-day user conference jam-packed with keynotes, product announcements, and exciting breakout sessions.
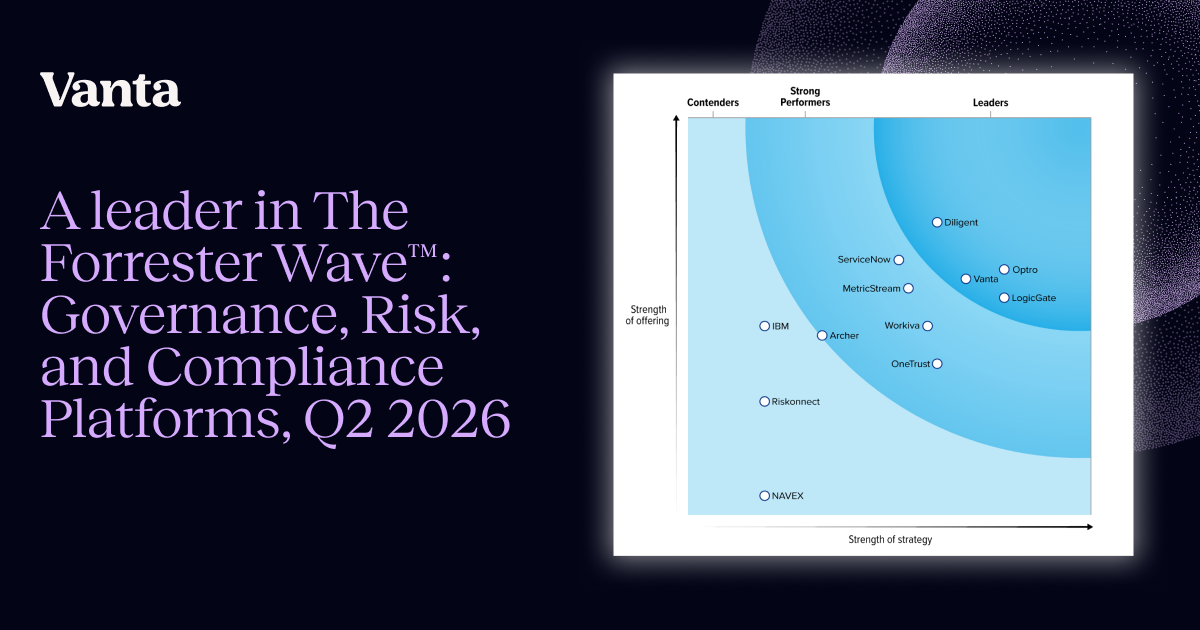
Our CEO, Christina Cacioppo, introduced several solutions to grow revenue and help reduce churn through better risk management. Addressing an audience of Vanta customers and partners, Cacioppo began her keynote by reaffirming Vanta as a platform centered on trust management—for solutions beyond satisfying compliance requirements.
Recent releases

Cacioppo pointed to several recent product releases as evidence of Vanta’s commitment to help organizations scale their security program, including Vanta’s Risk Management solution, which helps teams reduce organizational risk on a continuous basis.
Stevie Case, Vanta CRO, discussed the significant features of Vanta Trust Reports, which allows organizations to proactively demonstrate their trustworthiness to prospects and customers using a real-time trust profile. Since its launch, Vanta’s Trust Reports solution has been shared with thousands of customers and partners, and has accelerated sales cycles by up to 30%.
In addition, Case pre-announced Vanta Verified, the next iteration of how Vanta is rethinking trustworthiness and proof of security from the ground up. Vanta Verified will be a shared interface of trust between software buyers and sellers—one that is proactive, interactive, and continuous.
Elliot Goldwater, VP Partnerships, spoke to Vanta’s growing partner ecosystem, including the partner integration network powered by the Connectors API. Starting today, all Vanta customers can now discover and install partner-built integrations directly in Vanta via a self-serve experience.
Onstage to help celebrate the launch of our partner integration network was Vanta technology partner, Stephen Whitworth, CEO of incident.io. In addition, Tayler Sipperly, Corporate Development at Crowdstrike, spoke to the growing need for more automated, more integrated, and less costly solutions to tackle organizational security.
Upcoming products
Vanta’s latest products focus on de-risking the greatest threat surfaces of every organization: its people, vendors, and assets. The following solutions were announced from the VantaCon mainstage:
Access Reviews

We’re excited to introduce our Access Reviews solution. Reviewing and managing user access to systems is required for compliance, and to reduce the main surface area of risk within an organization: its people. These reviews normally take several days and labor costs can be in the thousands.
Vanta’s Access Reviews solution enables businesses of all sizes to accelerate, automate, and simplify access reviews. They can be done in hours, with cost savings over 90%. Using pre-built integrations, intuitive review workflows, and remediation management, it’s easy to use Vanta to review and report on user access.
Access Reviews is now available in beta to all customers.
Please contact your Customer Success Manager or contact us to gain access to the beta.
Vendor Management

We also announced our upcoming Vendor Management solution to address your second most susceptible surface area: your vendors. Vendors are the services or tools your organization uses to run your business and are a common point of weakness within a data breach.
Vanta’s Vendor Management solution serves as a single source of truth for security and IT leaders to track vendors and conduct risk analysis.
Just as Vanta shifted the compliance industry towards more automation using intelligent integrations, we’re also innovating vendor management by automating the review process and information gathering between customers and vendors.
Vendor Management will be available in beta this year.
Asset Inventory Management
Vanta’s upcoming Asset Inventory Management solution will address another critical area to monitor for risk: your cloud and physical infrastructure.
Our Asset Inventory Management tool will help security, compliance, and engineering leaders centralize their organization's resources into a single view for enhanced tracking, risk review, and management. Asset Inventory Manager will automatically detect new resources as they surface, intelligently annotate assets to remain compliant, and flag resources for risk.
Asset Inventory Manager will serve as your team’s consolidated view into your cloud and physical infrastructure for streamlined compliance and enhanced risk management.
Asset Inventory Manager will be available in early 2023.
Leveraging trust to unlock growth
The VantaCon 2022 keynote concluded with Stevie Case, Vanta CRO, and J.P. Morgan Head of Security Investment Banking, Dhruv Fotadar. The session centered around Vanta’s disruption to the SaaS and compliance industries.
During their live Q&A, Case and Dhruv discussed why time and costs associated with obtaining a certificate of trust pose considerable challenges for young businesses to sell upmarket.
Beyond the keynote, VantaCon’s breakout sessions buzzed with energy as attendees seized the opportunity to meet and learn from their peers innovating in software solutions.
Michael Devyver, Co-founder of EasyLlama, shared ways to leverage outside resources to help fill in gaps for growing compliance teams. Taylor Perkins and Gary Lin, respective Co-founders of Slope Software and Explo, led the audience through multi-standard compliance strategies that 2x’ed the top of their sales funnel and helped reduce sales cycles by 30%.
Vanta has fundamentally shifted the way companies demonstrate their trustworthiness and leveled the playing field for many innovative SaaS businesses by helping them get compliant at a fraction of the cost. Guest speaker Frederick Lee, Chief Security Officer at Gusto, shared how security and compliance are changing the way businesses work with one another. "Compliance is helping guide you through your security journey....compliance is actually leading security. Vanta knows the value of compliance as a driver for your business," Lee said.
Vanta’s upcoming collection of solutions will help organizations mitigate risk across their most important surface areas, automate the daily operations of maintaining compliance and security programs, and help businesses leverage their trustworthiness to unlock growth from previously unattainable markets.
We look forward to making security and compliance scalable for organizations at every stage.
To learn more about our UK edition, visit https://events.vanta.com/vantaconuk.





FEATURED VANTA RESOURCE
The ultimate guide to scaling your compliance program
Learn how to scale, manage, and optimize alongside your business goals.
















.webp)







-p-1600.jpg.webp)

.svg)
.svg)


