FedRAMP requirements
Guide to navigating the FedRAMP authorization process

Looking to streamline the work for FedRAMP compliance?
Any cloud service provider (CSP) offering in-scope cloud services that wants to sell to US federal agencies must obtain a Federal Risk and Authorization Management Program (FedRAMP) authorization. Although the program is based on NIST 800-53 (Rev. 5), the authorization process itself is distinct, with rigorous security controls and documentation vetted across multi-layered assessments.
Recent changes have also reshaped how CSPs approach the compliance landscape. The retirement of the Joint Authorization Board (JAB) Provisional ATO (P-ATO) path means that CSPs must primarily rely on agency sponsorships for authorization. The alternative FedRAMP 20x path also exists, but it’s still in its pilot stages and has yet to be rolled out at scale.
This guide will break down:
- Critical FedRAMP authorization phases
- Typical timelines for authorization
What is FedRAMP authorization?
FedRAMP authorization is a standardized security review for cloud service offerings (CSOs) handling federal data. It validates if the CSP’s controls meet the FedRAMP criteria and whether their documentation satisfactorily attests to those controls. If successful, the cloud service gets an Authority to Operate (ATO) and is listed on the FedRAMP marketplace under the appropriate baseline designation (FedRAMP LI-SaaS, Low, Moderate, or High).
Getting listed on the marketplace means that the CSO is now centrally visible to other federal agencies that may be looking for similar services.
Due to its reputation as one of the strictest security programs, FedRAMP authorization is also viewed as a signal of a mature security posture across various industries, including private and highly regulated markets.
Currently, the primary method to obtain an ATO is to find an agency sponsor. The sponsoring agency reviews your authorization package, validated through a third-party assessment organization (3PAO), and determines whether the CSO meets FedRAMP requirements and acceptable risk thresholds.
FedRAMP authorization via FedRAMP 20x pilot
FedRAMP authorities are also working toward a modernization initiative called FedRAMP 20x. While still in the pilot phases, it aims to reduce authorization timelines by as much as 20x through automation, cleaner collaboration, and machine-readable submission packages.
Under the 20x model, CSPs are no longer required to secure an agency sponsor to pursue authorization, removing one of the most persistent barriers in the traditional process.
20x also moves away from annual, point-in-time control assessments that demand huge resource commitment. Instead, CSPs are expected to establish processes and tooling that provide continuous, real-time visibility into their security posture, which is shared with agency partners on an ongoing basis.
Because FedRAMP 20x is being tested on a limited scale now, the agency-sponsored path is still the default authorization path for most CSPs.
3 phases of FedRAMP authorization

The agency-sponsored authorization process itself can be split into three phases:
- Pre-authorization
- Assessment
- Maintaining compliance
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
1. Pre-authorization
The pre-authorization stage heavily revolves around implementing the required controls and preparing the necessary documentation (authorization package). Many organizations start with determining their FIPS 199 impact tier—Low, Moderate, or High—based on the potential impact a breach of data confidentiality, integrity, or availability would have on the agency.
For CSPs offering low-risk cloud services, FedRAMP also defines a variation of the Low impact tier called LI-SaaS, for CSOs that don’t store personally identifiable information (PII) outside of login capabilities. This is a tailored subset of the Low baseline designed to offer a lightweight authorization path for services handling low-risk data. Under LI-SaaS, 3PAO can independently assess a subset of Low controls, while CSP attest the remaining controls. Although this tailoring can reduce assessment effort, CSPs remain accountable for all Low baseline requirements.
Some of the best practices for the pre-authorization phase include:
Secure stakeholder buy-in: Executive support is critical to ensure that your teams have the necessary time, budget, and tools to successfully implement FedRAMP controls.
- Understand the investment scope: Before committing, evaluate the resources you’ll need to meet FedRAMP criteria. Organizations should run a complete ROI analysis to understand if the substantial investment required will pay dividends in the future.
- Prepare FedRAMP documentation early: Begin developing FedRAMP-aligned documentation early, including your System Security Plan (SSP), Plan of Action and Milestones (POA&M), architecture diagrams, and boundary definitions. See that your documentation accurately reflects how controls are implemented in practice and remains internally consistent across artifacts, as this is a common gap uncovered during authorization audits.
- Conduct a readiness assessment: Many CSPs perform an internal or third-party readiness assessment to identify gaps before the formal assessment. A 3PAO can also conduct a FedRAMP-aligned readiness review and produce a Readiness Assessment Report (RAR), which highlights deficiencies and remediation priorities.
- Note: Once accepted by the FedRAMP PMO, the RAR can also be used to apply for FedRAMP Ready status in the Marketplace, signaling preparedness to pursue full authorization. You can use the RAR to apply for the FedRAMP Ready status in the Marketplace.
- Resolve high-risk findings promptly: Prioritize any critical issues flagged during your initial reviews to support a smooth final 3PAO assessment and authorization process.
Tip: A good approach to run this phase efficiently is through compliance and trust management platforms like Vanta. You get a FedRAMP-native setup to automate evidence collection, monitor artifacts, and manage readiness tasks with reduced manual effort and risk of errors.
2. Assessment
Once you’re fully prepared, undergo the formal authorization assessment by an accredited 3PAO. This involves detailed testing to ensure that your control implementations continuously meet the criteria for your baseline, as well as a thorough review of your SSP and other artifacts.
Before the assessment, your 3PAO may ask your key security roles to contribute to the Security Assessment Plan (SAP) they prepare, particularly for developing the testing methodology.
Some of the best practices for this phase include:
- Designate a point of contact: Assign a team member to coordinate with your 3PAO, respond to questions, and serve as a primary point of contact to reduce confusion and ambiguity.
- Centralize documentation: Keep all policies, procedures, and other compliance evidence in a centralized dashboard so your 3PAO can access and review them easily.
- Maintain transparency: Inform 3PAO and your sponsoring agency of your findings, remediation progress, and any gray areas proactively to strengthen trust and prevent surprises later in the assessment cycle.
- Sustain continuous monitoring and vulnerability management discipline: Don’t slow down your security practices during the formal assessment. Track vulnerabilities and document your remediation efforts to demonstrate you’re meeting FedRAMP remediation timelines and expectations.
After the assessment, the 3PAO will provide you with a Security Assessment Report (SAR). This report is a part of your documentation package, which details the auditor’s findings on security controls, risk assessments, and vulnerabilities.
Next, submit the package to the sponsoring agency for final review and approval. They’ll evaluate the SAR and other core artifacts to decide if you’re clear to get an ATO.
3. Maintaining compliance
After receiving an ATO, CSPs must contain compliance through FedRAMP’s continuous monitoring (ConMon) requirements. Key ConMon activities include monthly vulnerability scanning, POA&M updates, annual independent assessments, and annual penetration testing, along with timely incident and change reporting.
Some of the best practices for this phase include:
- Assigning clear roles: Designate owners for ongoing maintenance tasks so there’s defined accountability for vulnerability reporting, evidence reviews, and communication with your sponsor.
- Build a repeatable ConMon calendar: Treat ConMon as an ongoing operational process rather than a one-off project by creating a monthly, quarterly, and annual calendar. The goal is to minimize the chance of missing any task that could lead to ATO suspension or revocation.
- Tighten vulnerability management cycles: Establish strict timelines for addressing High and Critical findings. Regularly check in with your agency clients to reassure them you are consistently meeting FedRAMP standards and mitigating relevant risks.
- Regularly train teams on FedRAMP responsibilities: Conduct frequent training sessions so your teams understand their responsibilities under FedRAMP and stay aligned with time-sensitive tasks.
- Time documentation updates with patch management: Align documentation updates and agency reporting points with patch cycles so remediated vulnerabilities are accurately reflected in monthly scans and POA&M submissions.
- Leverage automation: Strong automation software can help you minimize manual effort by centralizing tasks, documentation, and evidence collection, making ongoing maintenance smoother.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
How long does FedRAMP authorization take?
The FedRAMP authorization timeline can vary widely based on factors such as your impact tier, system maturity, and alignment with your sponsoring agency.
Here’s an overview of typical timelines for the authorization process:
Get FedRAMP-authorized faster with Vanta
Vanta is a leading agentic trust platform that streamlines the process of obtaining and maintaining a FedRAMP authorization. It achieves this through workflow automation, tailored risk management, and step-by-step guidance that operationalizes complex requirements into clear, actionable tasks tailored to Low, Moderate, or High levels.
Vanta then helps map them to the evidence you need, ensuring your compliance progress is visible and trackable. The platform can also help you automate monthly vulnerability scans and track your POA&M updates through a unified dashboard, so you avoid delays and stay on track for annual reassessments.
You can access the following with Vanta’s FedRAMP product:
- Automated evidence collection powered by 400+ integrations
- Continuous monitoring through a centralized dashboard
- AI-assisted policy drafting and customization
- Auditor-approved pre-built policies that map to FedRAMP baselines
- Vendor risk management tools
If you’re looking for a 3PAO or a FedRAMP consultant, you can use Vanta’s partner network to find support for your compliance program.
Schedule a custom demo to see how Vanta can support your team for FedRAMP compliance.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
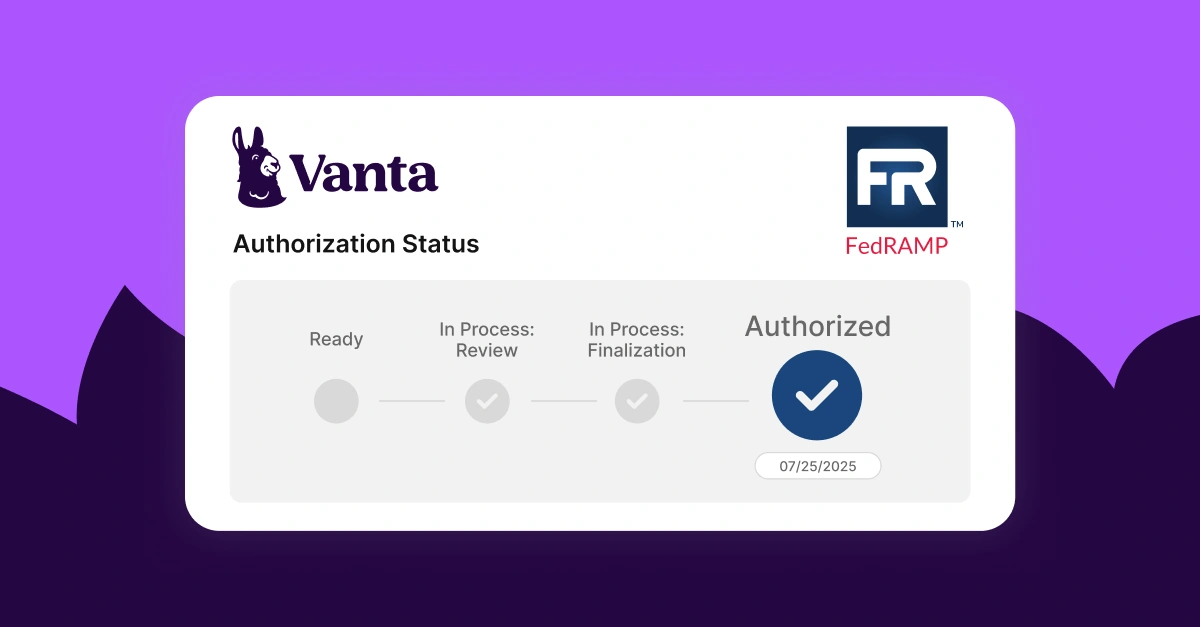
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




