FedRAMP levels
FedRAMP levels and baselines: All you need to know

Looking to streamline the work for FedRAMP compliance?

The Federal Risk and Authorization Management Program (FedRAMP) establishes mandatory security standards for cloud service providers (CSPs) working with U.S. federal agencies. Before its introduction, in-scope organizations typically had to prepare separate security documentation as assurance to each agency they served—a tedious and inconsistent process.
FedRAMP acknowledges that not all federal data and contracts are equally sensitive or require the same level of security. This means the depth of controls implemented can vary across CSPs, depending on the sensitivity of the data they handle.
That’s why FedRAMP uses impact levels to help CSPs meet different security expectations by implementing tiered baseline controls. Understanding what applies to your organization is essential for scoping compliance work, including controls and policies.
In this article, we’ll discuss all FedRAMP levels, sample baseline control areas, and the steps to determine the tier applicable to you.
What are FedRAMP impact levels?
Guided by Federal Information Processing Standards (FIPS 199) standards, the FedRAMP impact levels are tiers that categorize cloud service offerings (CSOs) by the sensitivity of the data they handle. The objective is to define the scope and rigor of baseline security controls relevant to the risk and impact of compromise in the cloud.
Each FedRAMP level corresponds to a set of controls drawn from NIST SP 800-53 Rev. 5, with the number of controls and stringency increasing with every higher level.
The framework currently has three main impact levels: Low, Moderate, and High. The idea is for a CSP to implement controls under the relevant tier and get independently validated by a FedRAMP-accredited third-party assessment organization (3PAO). Upon successful validation and review by the program, the CSP achieves FedRAMP Authorization. Individual federal agencies then leverage this existing authorization to review the package and quickly issue their own Authority to Operate (ATO).
FedRAMP has also introduced another sub-tier called LI-SaaS. It’s not an independent impact level but a version of FedRAMP Low impact level for CSOs that handle only the lowest-risk federal data. For this baseline, a 3PAO must independently test a subset of controls, which makes it a faster path to authorization.

{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
FedRAMP impact levels explained [with sample controls]
The table below provides a high-level overview of all FedRAMP impact levels (lower to higher)
*Latest as of December 2025 and aligned with NIST SP 800-53 Rev. 5
FedRAMP Low impact level
The FedRAMP Low designation is given to services that handle either publicly available information or minimal amounts of personally identifiable information (PII), beyond user login credentials. It applies to cloud services where the loss of confidentiality, integrity, or availability would result in a limited adverse effect on agency operations, assets, or individuals.
Examples of solutions that may be considered low-impact include:
- Creative, design, and research tools
- Examples: Vyond, Perplexity
- Public-facing messaging platforms
- Example: CivicPlus
- Scheduling or project management tools
- Examples: Trello, PagerDuty
- Compliance and trust management solutions
- Example: Vanta (20x low)
To meet low-impact tier baseline requirements, you’ll need to implement 156 controls spread across several control areas (“families”) to mitigate common security threats. Here are a few examples:
Even for low-impact cloud services, aligning with the framework requires careful long-term planning. You’ll have to maintain stringent requirements surrounding documentation, such as creating and maintaining a System Security Plan (SSP), to get authorization.
FedRAMP LI-SaaS: Tailored subset of Low
LI-SaaS is a tailored version of the Low impact level. It applies to low-risk SaaS offerings where a loss of confidentiality, integrity, or availability would only have a limited adverse effect, and where the service doesn’t handle federal information beyond the scope of FedRAMP Low.
Example cloud services that could qualify for LI-SaaS include:
- Public survey or engagement
- Social media management
- Learning Management Systems (LMS)
LI-SaaS requires you to implement the same number of controls as FedRAMP Low: 156. The key distinction is that LI-SaaS follows a hybrid attestation approach. 66 controls are independently tested by a 3PAO, while the remaining 90 are satisfied through CSP attestation.
This leaner approach potentially reduces the assessment and cost logistics, allowing organizations greater flexibility in control implementation. Other requirements, such as documentation quality, operational rigor, and SSP maintenance, remain the same.
Some of the controls you must implement for the LI-SaaS baseline include:
FedRAMP Moderate impact level
FedRAMP Moderate covers systems where data compromise could have seriously adverse effects on an organization, including damage to assets or financial harm. Example systems under this designation include:
- Financial systems
- Human resource tools
- Case management platforms
FedRAMP Moderate is the sweet spot for most CSPs, as it attests to strong security and also supports systems that handle Controlled Unclassified Information (CUI) data under the Cybersecurity Maturity Model Certification (CMMC).
To meet the baseline criteria for moderate impact, you must implement 323 controls guided by NIST SP 800-53 Rev 5. The table below illustrates some notable controls for FedRAMP Moderate:
Good to know: Supply chain risk management controls have been newly elevated in FedRAMP Rev. 5. This reflects a growing focus on supply chain integrity, requiring organizations to formalize policies and manage cybersecurity risks throughout the vendor lifecycle.
FedRAMP High impact level
FedRAMP High is intended for systems where data compromise could have severe or catastrophic effects on operations, assets, or individuals. It’s necessary for cloud services that handle highly sensitive data, such as:
- Law enforcement information
- Emergency services
- Public health information (PHI)
Due to the sensitivity of this information, aligning the high baseline requires a noticeable increase in control depth, rigor, and operational maturity. In-scope organizations need to implement 410 mandatory controls. For systems moving from Low or Moderate to High, this could mean material upgrades in areas such as access control, encryption, logging, and incident response.
A common misconception is that FedRAMP High is a more secure version of Moderate, when it's just a separate control set with its own monitoring and documentation requirements. Some of the controls you must implement include:
How to determine your FedRAMP impact level
Determining your FedRAMP impact level is a formal FIPS 199 process that checks risk across the CIA Triad—Confidentiality, Integrity, and Availability. The assessment evaluates both the types of information you handle and the criticality of the system that processes it.
Here’s how to get started:
- Determine the type of information in scope.
- Evaluate the information system.
- Apply the highest impact level.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Step 1: Determine the type of information in scope
First, identify all types of data your system will handle using NIST SP 800-60 (e.g., Privacy Data, Financial Records, System Metadata). Assign a Low, Moderate, or High rating to each type based on the potential impact of a data breach.
For example, a federal website that stores public information about grant announcements may consider their data Low impact. However, if the same website is also used to share real-time funding data exclusively with agency stakeholders, Moderate or High may be more appropriate.
Here’s how different types of data can map to FedRAMP impact levels:
Step 2: Evaluate the information system
Next, assess the system’s operational criticality independent of the data it stores. Ask: “If this system becomes unavailable, produces incorrect outputs, or behaves unpredictably, how would that affect the agency’s mission?”
This step focuses on the role the system plays in agency operations, including whether it supports time-sensitive decisions, public safety functions, or mission-critical workflows. Even systems that handle low-sensitivity data can require higher impact levels if failures would cause operational disruption or harm. This involves several activities, including:
- Identifying and mapping all FedRAMP-relevant assets (you can consult a FedRAMP or cybersecurity assessor for accurate mapping)
- Analyzing potential internal and external threats to each system
- Assigning low, moderate, and high impact rankings to each system based on the potential effects of a data compromise
Step 3: Apply the highest impact level
Your system’s overall impact level and required baseline controls is determined by the highest ranking you assign to an individual asset. It’s also called the High Water Mark. For example, if even one of your assets maps to FedRAMP High, the entire cloud service should align with High baseline controls.
Tip: While the impact level is determined by the FIPS 199 process, it’s essential to first understand your scope of work with government agencies and streamline your authorization goals more accurately. For example, if your contract only requires you to manage low-impact data with federal agencies, you don’t need to align with Moderate or High.
That said, businesses typically plan FedRAMP authorization from a scaling perspective. They may start with Low or LI-SaaS and gradually upgrade to Moderate and High to expand government contracting opportunities.
Ideally, plan at least 18 months in advance if you intend to pursue a higher impact tier. This gives you a larger window to prepare for high-friction control families, such as Access Control, Audit & Accountability, Configuration Management, and System & Communications Protection, which require deeper automation and documentation maturity.
Navigating FedRAMP levels and baselines: Challenges and tips
One of the most common challenges is CSPs underestimating their impact level, which can lead to reworks and delays in the authorization process. Another is adapting to the evolution of FedRAMP. For example, with the shift to Rev. 5, in-scope organizations must align with the new control renumbering, update privacy and security documentation, and track transition timelines—which can be overwhelming without the right tech stack.
Additionally, once you’ve achieved authorization at any level, you have to implement continuous monitoring (ConMon), internal assessments, documentation updates, and monthly reporting to align with FedRAMP. This also helps identify if you need to adjust your impact level and/or revisit controls over time.
How Vanta helps streamline FedRAMP compliance
Vanta is a leading agentic trust platform that helps organizations manage their compliance goals through automated workflows, continuous monitoring, and unified visibility.
Vanta supports you throughout the FedRAMP authorization process by providing expert guidance and breaking down complex requirements into actionable steps, tailored to your organization’s impact level.
Besides compliance, the platform also helps you with ongoing risk management to address compliance gaps and tools to demonstrate compliance. Vanta’s FedRAMP compliance product comes with features like:
- A centralized dashboard for everything FedRAMP
- Pre-built, approved FedRAMP policies
- AI-powered policy management
- Continuous monitoring through 400+ integrations
If you’re still preparing for an assessment or looking for a 3PAO, you can use Vanta’s partner network to find vetted professionals.
Book a demo today for a customized walkthrough of the FedRAMP compliance suite.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
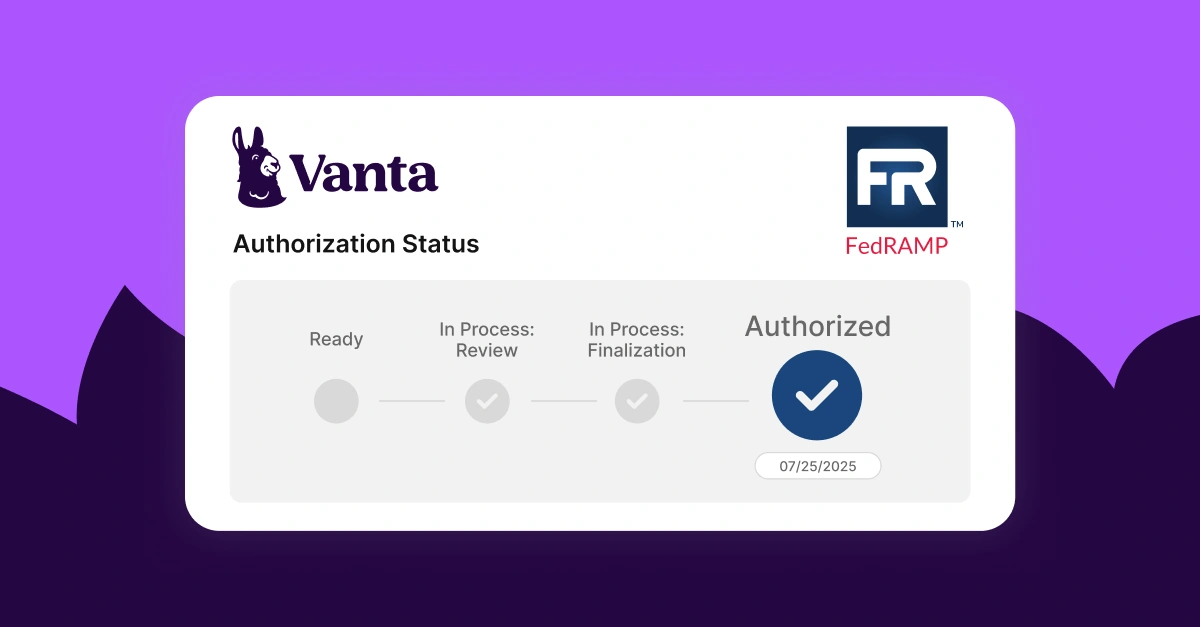
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




