FedRAMP requirements
Essential FedRAMP documentation map: SSP, SAP, SAR, POA&M

Looking to streamline the work for FedRAMP compliance?
The Federal Risk and Authorization Management Program (FedRAMP) isn’t just about meeting technical security requirements. It’s one of the most stringent and documentation-driven compliance processes in the US.
You need to deliver a comprehensive set of records and artifacts that demonstrate how security controls are implemented, assessed, and continuously monitored. Maintaining certain documents could also be necessary to keep your program current and support audit processes.
This guide breaks down FedRAMP documentation for you, covering:
- Which documents are required
- Who’s responsible for preparing them
- Best practices for maintaining FedRAMP documentation
What are the essential FedRAMP documents?
_L1R1.png)
To pursue FedRAMP authorization, you must prepare four key documents:
- System Security Plan (SSP)
- Security Assessment Plan (SAP)
- Security Assessment Report (SAR)
- Plan of Action and Milestones (POA&M)
These artifacts play a distinct role in the authorization lifecycle, regardless of whether you’re pursuing FedRAMP LI-SaaS, Low, Moderate, or High baselines. Some documents are created during preparation, while others will accompany independent assessments or be updated regularly as part of ongoing compliance.
Here’s a quick breakdown of how these critical documents fit into the FedRAMP process:
These four core documents are interconnected as one feeds into the next. For instance, the SSP is your security blueprint that describes how you met your FedRAMP controls, while the SAP uses that blueprint to plan the evaluation of controls.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
1. System Security Plan (SSP)
The SSP is the foundational document for your FedRAMP authorization. It is a blueprint record of your cloud service’s security posture and the primary document 3PAOs and agencies rely on to understand what your system is, how it’s built, and what security controls are implemented.
The SSP should contain:
- A statement identifying the system and its purpose within the authorization context
- System boundaries, including in-scope components and external dependencies
- The system’s hardware and software inventory
- Existing controls with details on how they’re implemented
- References to evidence or descriptions of implementation and validation
The CSP is responsible for developing and maintaining the SSP, as it serves as proof of the cloud service’s security posture during authorization and ongoing monitoring. Ideally, the CSP should review and update the SSP periodically, such as every quarter, or as significant changes occur within systems and controls. The effort toward maintenance depends on system complexity and update frequency. As Vanta’s GRC expert notes:
Since this is a high-stakes document with in-depth explanations and demonstrations, FedRAMP offers a template to help CSPs align their SSP with the expected criteria.
2. Security Assessment Plan (SAP)
The 3PAO prepares the SAP document before reviewing your controls. It serves as a guide for all security testing actions.
While the 3PAO is responsible for preparing SAP, the specific testing methodology typically requires review and approval from your internal team, particularly senior security leadership roles, such as the Head of Information Security and/or the Chief Information Security Officer (CISO). The goal is to guide assessments within the system boundary, facilitate consistent and structured review measures, and factor in operational realities.
FedRAMP also provides a SAP template that outlines what the plan should include. You can refer to it to proactively define the following for your 3PAO:
- The scope of security testing
- Testing methodologies
- Roles that will be tested
- Assumptions and constraints
- Test plan and schedule
SAP holds the most value before and during the assessment process. Errors and misalignments can lead to delays, retesting, and disputes over findings, which can heavily influence the next document, the SAR.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
3. Security Assessment Report (SAR)
The SAR is where the 3PAO documents the results of an independent FedRAMP assessment. It tells how your controls perform under testing and what your security posture is at a specific point in time. The SAR should include:
- A description of the system and assessment scope
- Detailed control testing results
- Identified vulnerabilities, deficiencies, and non-compliant findings
- Risk ratings and severity levels associated with each finding
The SAR is a critical input for sponsoring federal agencies, which review it as part of the risk-based decision to issue an Authority to Operate (ATO). The FedRAMP PMO also reviews the SAR to ensure the authorization package meets program requirements and quality standards.
Since the SAR is created by the 3PAO, the CSPs also use it as a basis for objective remediation planning. It can inform the POA&M and clarify the most pressing areas of risk remediation or mitigation. Findings documented in the SAR are used to populate and update the Plan of Action and Milestones (POA&M). This helps security and GRC teams identify the most urgent risks and track mitigation activities through authorization and ConMon.
4. Plan of Actions and Milestones (POA&M)
FedRAMP recognizes POA&M as a tool for systematically tracking and addressing known security gaps and challenges. This document helps you identify and prioritize key issues that you must remediate if you want to achieve authorization, including:
- Key issues
- Remediation actions
- Required resources
- Milestones that will lead you to compliance
While the POA&M supports initial authorization compliance, its primary role is ongoing risk management and continuous monitoring. There’s also an element of accountability and timely action, as FedRAMP sets specific timelines for addressing different tiers of POA&M items
You must use the standardized FedRAMP template to draft your initial POA&M and update it as you progress with remediation plans. Using an automation tool like Vanta can also help you with governance by centralizing findings, tracking remediation status, and maintaining evidence across reporting cycles.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Once you have your authorization package ready, including the SSP, SAR, and POA&M, you need to submit it to your sponsoring agency for review. The agency will evaluate the risk and determine whether to issue an ATO or require additional remediation before approval.
FedRAMP supporting documentation
Besides the core authorization package, you must maintain several supporting documents as part of your FedRAMP authorization program. Examples:
- Incident response plan
- Continuous monitoring strategy
- Configuration management plan
- Rules of Behavior (RoB)
- Control implementation summary
Ownership of these documents spans between a CSP’s security, engineering, and compliance teams, and in some cases, includes shared responsibility with the sponsoring agency.
Depending on your authorization path, the following may also be relevant to you:
- Readiness Assessment Report (RAR): A 3PAO may choose to conduct an optional readiness assessment before the formal one to evaluate preparedness, the results of which are documented in the RAR.
- Machine-readable documents under FedRAMP 20x: As part of FedRAMP’s modernization initiative, the FedRAMP 20x pilot requires CSPs to submit machine-readable documentation to address requirements and recommendations. This is an in-progress pilot program and is not available to all, as of January 2026.
Bonus: Read about Vanta’s lessons learned from the 20x pilot here.
Best practices for maintaining FedRAMP documentation
One of the FedRAMP requirements is to monitor and maintain the core documents even after authorization. We’ve singled out five best practices that can help you:
- Treat documents as living artifacts: Cloud systems are constantly evolving, and your documentation needs to evolve accordingly to avoid audit friction. Treat your documents as living artifacts. Establish a regular review and update schedule.
- Build version controls: Use formal version control procedures for all artifacts to maintain an audit trail. Log every update with the date, author, and a summary of the modification so that your team can keep up with the changes.
- Centralize documentation: Maintain one secure repository for your documentation. By centralizing documentation, you can minimize duplication, simplify evidence collection, and allow all authorized stakeholders to work from the current version of the document.
- Assign role-specific document ownership and accountability: Define the roles and responsibilities when it comes to documentation management. Clear ownership reduces gaps, improves response times during audits, and ensures ambiguities don’t delay updates.
- Use automation: Use a credible compliance automation solution like Vanta to reduce administrative overhead, minimize human error, and save time during readiness workflows. Such a tool can streamline documentation, synchronize data, and automatically populate updates into FedRAMP templates.
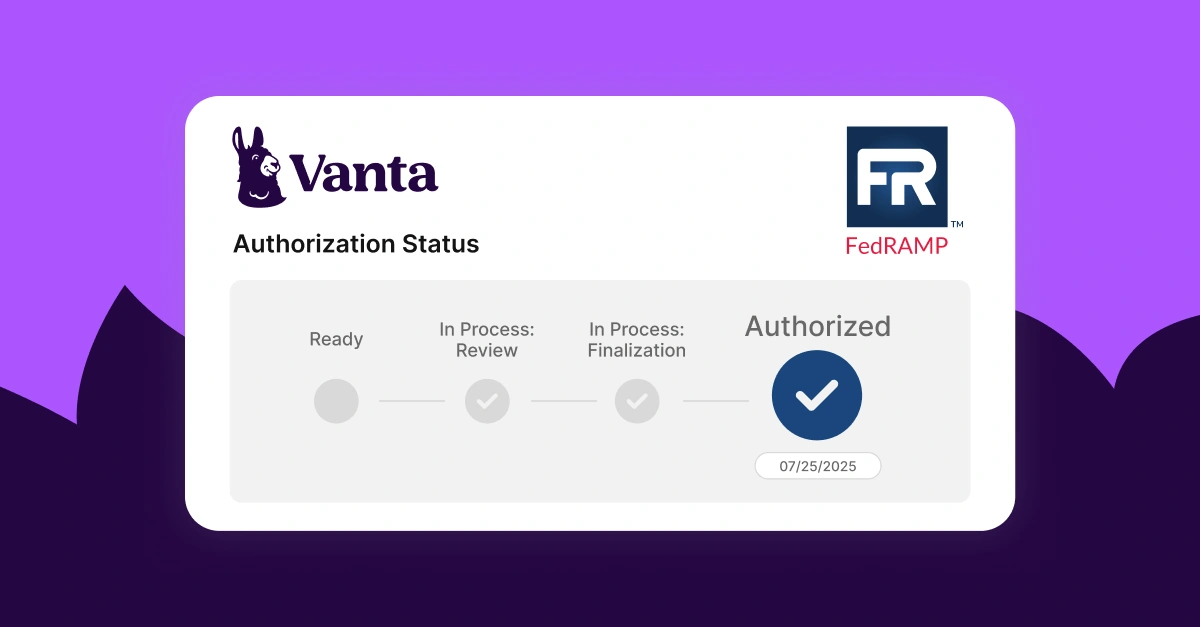
Why Vanta is your go-to for FedRAMP documentation
Vanta is an agentic trust management platform that simplifies FedRAMP authorization documentation and workflows. It takes the guesswork out of the process with its integrated implementation guidance that ensures you complete FedRAMP documentation without any confusion.
With Vanta, you can generate FedRAMP-aligned policies, populate your SSP, and manage POA&Ms with templates and automation that cut manual work. This operationalized support, combined with AI-powered prep, can help you streamline documentation tasks and resolve potential issues faster.
Vanta’s FedRAMP product has features such as:
- Centralized dashboard to track actions, evidence, and milestones
- Pre-built, auditor-approved document templates
- Automated evidence collection
- AI-powered policy management
- Vendor risk management support
- Continuous monitoring through 400+ integrations
- Audit-ready evidence packages for 3PAO review
You can use Vanta to find a vetted 3PAO through its partner network and receive tailored guidance throughout documentation and readiness workflows.
Schedule a custom demo to see how Vanta helps you upgrade and maintain your compliance posture.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




