Additional resources
FedRAMP vs. SOC 2: Key differences for cloud service providers

Looking to streamline the work for FedRAMP compliance?
FedRAMP and SOC 2 are two widely adopted security frameworks for cloud service providers (CSPs) that safeguard sensitive data in cloud environments. Both share the same goal of validating the provider’s data security practices and building customer trust. But they serve different market priorities, data types, and regulatory expectations, which can influence how you decide on what to pursue.
This comparison guide will help you evaluate both by breaking down their differences and similarities. We’ll also discuss how to choose between the two.
What is FedRAMP?
FedRAMP, or Federal Risk and Authorization Management Program, is a federal authorization program that standardizes how federal agencies assess and authorize cloud services. It defines the baseline requirements for protecting federal data that in-scope CSPs must meet, which is tailored based on the NIST 800-53 (Rev. 5) control catalogue. Here are a few examples:
Federal data varies in sensitivity, so under FIPS 199, federal systems are classified as Low, Moderate, or High impact based on the potential harm from a compromise of confidentiality, integrity, or availability. The classification means you can pursue:
- FedRAMP Low (or LI-SaaS): Applies when a loss of confidentiality, integrity, or availability would have a limited adverse effect
- FedRAMP Moderate: Covers the majority of federal cloud systems, where a loss of confidentiality, integrity, or availability would cause a serious adverse effect
- FedRAMP High: Applies to the most sensitive unclassified data, where a breach would cause severe or catastrophic harm
FedRAMP applies specifically to cloud service providers that process, store, or transmit federal data on behalf of U.S. government agenciesWhile non-compliance won’t lead to fines, it’ll prevent you from entering the FedRAMP Marketplace and competing for government contracts.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
What is SOC 2?
SOC 2 is a voluntary framework that helps service organizations, including SaaS, PaaS, and IaaS providers, strengthen and validate their internal data security. In contrast to FedRAMP, which focuses on federal data, SOC 2 is industry-agnostic and applies to customer data across all sectors.
This framework is based on the five Trust Services Criteria (TSCs) that define how organizations should safeguard data. Here’s an overview of the requirements:
You can undergo an independent audit to receive a SOC 2 attestation—you can pursue two types of attestation reports:
- Type 1: A point-in-time review of your control design
- Type 2: A comprehensive review of how your controls operate over 3–12 months
SOC 2 compliance is not mandatory, but it is a common expectation in service contracts across various sectors.
{{cta_withimage1="/cta-modules"}} | SOC 2 compliance checklist
FedRAMP and SOC 2 similarities: Control overlap and mapping
While they serve different markets, FedRAMP and SOC 2 share foundational similarities. Both emphasize data security and require organizations to implement stringent controls to protect the information they handle.
Another shared requirement is continuous monitoring (ConMon) that reinforces the idea that compliance isn’t a one-time event. Implemented controls must remain effective over time. To evaluate continuous compliance and remediate gaps, both frameworks entail annual internal assessments.
FedRAMP and SOC 2 also rely on many of the same security practices and share a number of common controls, including:
- Access control
- Penetration testing
- Contingency planning
- Incident response
- Risk assessments
We mapped some common overlaps in control focus areas in the table below:
For many CSPs, SOC 2 artifacts can serve as a baseline for FedRAMP. However, FedRAMP is largely more prescriptive and rigorous than SOC 2. It requires detailed control implementation narratives, technical evidence, formal testing procedures, and ConMon aligned with NIST SP 800-53 (Rev. 5). Control coverage must also account for FIPS 199 impact levels because higher levels require a larger control set and stricter configurations.
Differences between FedRAMP and SOC 2
Despite many overlaps, FedRAMP and SOC 2 differ in a lot ways. Reference the table below for a general comparison, after which we’ll expand on five of the key differences for a more nuanced understanding.
Let’s now explore five key FedRAMP and SOC 2 differences in detail:
1. Main purpose
FedRAMP exists to standardize how CSPs secure US federal data and is mandatory for federal cloud use, while SOC is designed to broadly demonstrate internal security to customers and stakeholders.
FedRAMP enables government-wide reuse of authorization, meaning you can pursue multiple cloud service contracts in the FedRAMP Marketplace with the same authorization package.
SOC 2 is more about customer-by-customer trust signaling and applies to services beyond the cloud. Customers may evaluate a SOC 2 attestation independently, often combining with their own due diligence and risk reviews and making the final vendor selection based on what they value.
The contrast is also visible in the scale of approved/attested services. FedRAMP authorizations are limited and highly selective, while thousands of organizations across sectors are SOC 2 attested.
2. Enforcement
FedRAMP has a formal governance structure with several bodies performing distinct obligations:
- FedRAMP Board: Provides general guidance and sets policy direction
- FedRAMP PMO (GSA): Manages day-to-day operations, program guidance, and compliance process
- Contracting agencies: Sponsor CSPs and oversee their authorization
- NIST: Develops the underlying security standards and guidelines
- Office of Management and Budget (OMB): Oversees the program’s modernization and policies
SOC 2, as a voluntary attestation, doesn’t have an enforcing body. Under SOC 2, organizations are audited by external auditors from a CPA-licensed firm.
3. Controls
SOC 2 has a more flexible control framework than FedRAMP. It lets you determine which controls you need to implement to stay aligned with the TSC, as long as you meet the mandatory security criterion. The other TSCs are optional and can be implemented based on customer expectations or to elevate trust.
FedRAMP is highly rigorous and prescriptive. It requires organizations to implement a strict baseline set of controls based on the impact tier, in addition to any extra controls the agency may deem relevant to the SLA. The fixed baseline control requirements per impact level are:
- Low impact: 156
- LI-SaaS (tailored Low): 66 controls tested + 90 attested (156)
- Moderate impact: 323
- High impact: 410
4. Authorization/Attestation process
The compliance timeline for SOC 2 is notably shorter, taking 1–3 months for a Type 1 report and 3–6 months for a Type 2 report.
FedRAMP timelines are considerably longer and tied to the impact level.
Another difference in the final authorization process is how the audit is approached. For SOC 2, the third-party audit is the final step to attestation.
For FedRAMP, the Third Party Assessment Organization (3PAO) audit helps you finalize a documentation package that you deliver to the sponsoring agency to receive the Authority to Operate (ATO). The FedRAMP PMO also reviews your package for compliance.
5. Cost investment
*Table rubrics: Medium indicates average investment relative to the size and complexity of the organization, while high and very high indicate progressively greater investments.
FedRAMP is substantially costlier than SOC 2 due to its federal-grade requirements, the depth and number of mandated controls, and ongoing maintenance and agency oversight.
When it comes to SOC 2, the costs can range from $5,000 to $50,000+, depending on:
- Your decision to pursue a Type I or a Type II report
- Whether the audit covers a single or multiple TSCs
- Security readiness
Cost modeling for FedRAMP involves a much larger upfront investment than SOC 2, driven by the premium cost of FedRAMP Authorized services and the engineering uplift required to meet stricter technical and documentation standards. Most organizations also budget for specialized consultants and an independent 3PAO assessment, which adds significant additional expense before authorization.
For the sake of estimates, FedRAMP audit, authorization, and continuous monitoring costs can sit anywhere between $150,000 and $1M+, influenced by the impact level, system complexity, and readiness.
Another possibility is to pursue both if that aligns with your business goals; however, in practice, most organizations obtain a SOC 2 attestation before pursuing FedRAMP.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
FedRAMP or SOC 2: Which one should you pursue?
Whether you should pursue FedRAMP or SOC 2 depends mainly on your industry and operational goals as a CSP. If your objective is to secure federal contracts, you must pursue FedRAMP. Otherwise, you could benefit from SOC 2 since it is more flexible and applicable to any industry.
Another possibility is to pursue both if that aligns with your business goals; however, in practice, most organizations obtain a SOC 2 attestation before pursuing FedRAMP
How automation bridges FedRAMP and SOC 2
Automation allows CSPs to scale compliance across either or both frameworks with greater efficiency. By automating control implementation and evidence collection, organizations can:
- Maintain a single source of truth for controls and artifacts
- Avoid duplicated work when evidence is reusable across frameworks
- Reduce manual effort during initial assessments and ongoing compliance
Automation can be particularly useful for maintaining SOC 2 and FedRAMP requirements. With the right tool, you can automate data collection, control testing, compliance alerts, and report generation, as well as offer your auditors a centralized platform for accessing evidence, control status, and task owners.
{{cta_simple1="/cta-blocks"}} | SOC 2 product page
Achieve your compliance goals faster with Vanta
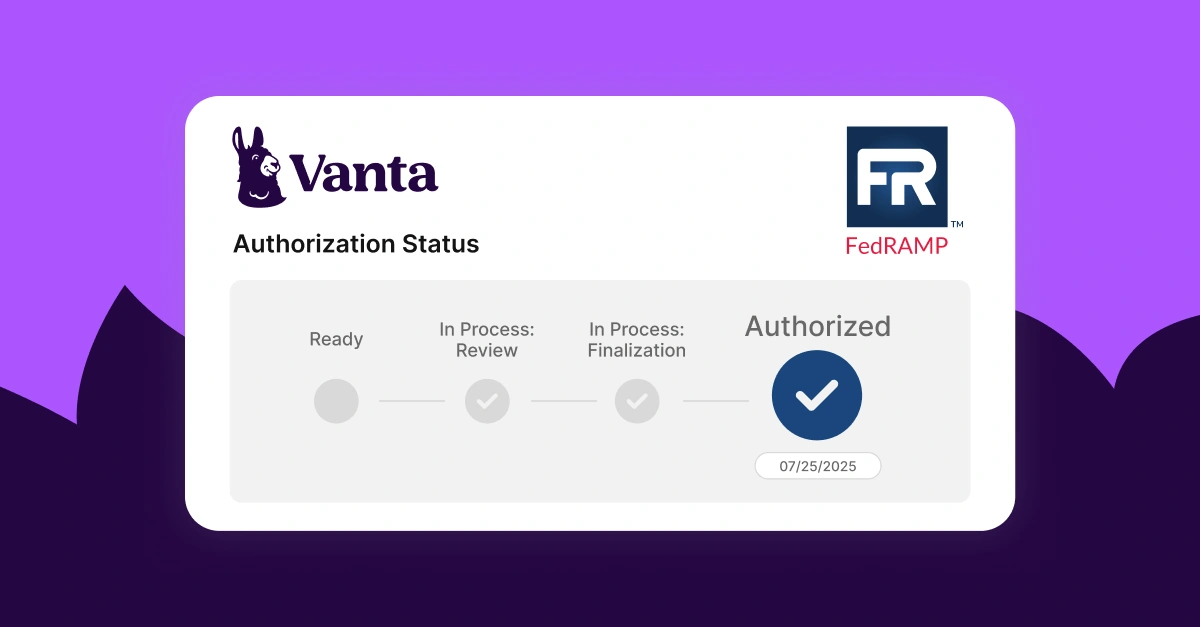
Vanta is a robust agentic trust platform that streamlines the entire compliance lifecycle across 35+ frameworks like SOC 2, FedRAMP, CMMC, and ISO 27001. Its agentic workflows, unified visibility, and continuous risk monitoring capabilities can manage framework requirements in an organized and cost-efficient manner.
Vanta’s FedRAMP product turns complex requirements into easy-to-follow, trackable tasks. You can get audit-ready faster with features like:
- Automated evidence collection with 400+ integrations
- AI-powered policy drafting
- Unified dashboard for continuous monitoring
- Automated monthly vulnerability scans
- Support with updating your POA&M
- Auditor-approved pre-built policies
- Vanta partner network to find a 3PAO
If you’re pursuing only SOC 2, Vanta’s SOC 2 product has built-in workflows and guides to help you get attested. For organizations pursuing multiple frameworks, Vanta’s cross-mapping feature can help you reuse evidence.
Book a custom demo for FedRAMP (or SOC 2) for a tailored walkthrough for your team.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
FAQs
Can one audit cover both FedRAMP and SOC 2?
No, the processes and scope are too different to be covered by a single audit. That said, many organizations reuse policies, procedures, and technical evidence across both programs and often coordinate their FedRAMP and SOC 2 assessments to reduce duplication of effort.
Who issues FedRAMP authorization and SOC 2 reports?
FedRAMP authorization is issued by a sponsoring federal agency’s Authorizing Official (AO), while SOC 2 reports are issued by accredited third-party auditors.
How often must you renew FedRAMP and SOC 2?
Both FedRAMP and SOC 2 frameworks should be renewed annually.
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




