FedRAMP levels
How to prepare for FedRAMP Low and the 20x pilot: Eligibility and requirements

FedRAMP levels
Looking to streamline the work for FedRAMP compliance?

FedRAMP Low, Moderate, and High are the three impact levels under the Federal Risk and Authorization Management Program (FedRAMP). These levels are primarily determined using FIPS 199, which evaluates the potential impact on confidentiality, integrity, and availability (CIA). Other factors like the system’s function and its role in the federal operations also influence the level.
FedRAMP Low applies to cloud systems where the loss of confidentiality, integrity, or availability would have a limited adverse effect. These systems typically support public-facing or low-risk federal workloads that do not process sensitive information such as CUI.
The emerging FedRAMP 20x pilot also builds on this baseline by introducing automation and cloud-native, machine-readable workflows to modernize compliance processes and reduce friction in authorizing low-impact systems.
This guide will help you assess if you should pursue FedRAMP Low, opt for FedRAMP 20x, or level up with Moderate or High impact levels. We’ll discuss:
- Who needs FedRAMP Low
- What’s required for this baseline
- How to prepare for FedRAMP Low authorization
What is FedRAMP Low?
FedRAMP Low is the baseline security standard for cloud service providers (CSPs) that work with government agencies and handle federal data categorized as low impact under FIPS 199 (Federal Information Processing Standard Publication 199). It requires the smallest set of security controls among the Low, Moderate, and High baselines.
This baseline is designed for systems where a breach of confidentiality, integrity, and availability would have a limited adverse effect. For example, a website that hosts general public-facing information about a federal agency would need the FedRAMP Low baseline since a potential data breach would cause minor operational impact, and no sensitive data would be exposed.
The main difference among these baselines is the type and sensitivity of data they protect and the potential impact to its confidentiality, integrity, and availability. Low-impact cloud service offerings (CSOs) only handle public or minimally sensitive data and typically do not access sensitive personally identifiable information (PII) beyond what’s needed for basic logins.
Once a system requires storing or processing higher-risk, sensitive PII, it must switch to a Moderate baseline. Finally, if a CSP has access to highly sensitive data such as law enforcement or mission-critical information, it often warrants a FedRAMP High categorization.
To define the appropriate impact level, you need to go through a formal FIPS 199 impact assessment and consult with your sponsoring federal agency. Avoid relying solely on policy assumptions or internal judgment.
Bonus: You can read about other authorization levels in these Vanta guides:
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Who needs FedRAMP Low authorization?
The FedRAMP Low baseline is required for cloud service providers (CSPs) that aim to sell services handling non-sensitive and publicly releasable federal data. This could refer to data with minimal confidentiality requirements, such as public policies, open datasets, and general census reports on government websites.
This entry-level authorization level is generally pursued by CSPs wanting to enter the FedRAMP Marketplace, including:
- Cloud services that target low-risk federal use cases
- Public-facing services handling little or no sensitive data
- Lightweight SaaS applications like to-do apps, collaboration tools, and calendar apps
In practice, nearly any cloud service a federal agency wants to use must at least meet the Low baseline, with a few expectations for services like social media and search engines.
What is required for the FedRAMP Low baseline?
Each FedRAMP baseline requires CSPs to implement a specific set of controls from NIST Special Publication (SP) 800-53, including both base controls and, if applicable, control enhancements.
The requirement for FedRAMP Low is to integrate 156 security controls across applicable control families. Here are some of the main categories with the highest number of controls:
CSPs must explain how each security control is met in the System Security Plan (SSP), a formal document that describes integrated and inherited controls, data flows, and the system infrastructure. The controls must then be independently validated by a 3PAO (third-party assessment organization) for FedRAMP Low authorization.
What is the FedRAMP LI-SaaS baseline?
The Low-Impact Software as a Service (LI-SaaS) baseline is a tailored subset of the Low baseline for systems with minimal security risk. It was designed for simple SaaS applications that only store basic login details (such as email, username, and password).
FedRAMP LI-SaaS baseline requires the same number of security controls (156), but reduces the 3PAO validation burden to accelerate the authorization process. Under FedRAMP Rev. 5, only 66 controls require independent 3PAO testing, and 90 can be met through CSP attestation. This means the SSP documentation requirements are also simplified compared to a standard FedRAMP Low authorization.
Eligibility requirements for LI-SaaS
Cloud providers can qualify for LI-SaaS if they meet the following requirements:
- Be fully operational (and not in the development phase)
- Contain no PII other than what is required for login (username, email, password)
- Fall under a SaaS application according to NIST SP 800-145
- Run entirely in a cloud environment
- Are rated as Low impact under FIPS 199
- Operate on a FedRAMP-approved PaaS or IaaS or provide their own underlying infrastructure within the authorization boundary
Does FedRAMP Low 20x automate low-impact authorization?
The U.S. General Services Administration (GSA) introduced the FedRAMP 20x Phase One pilot program in early 2025 to test automation for low-impact authorizations and gradually move to higher tiers. As of November 2025, Phase Two of the pilot is in progress, but participation is limited and not open to the public. FedRAMP is targeting approximately 10 Moderate pilot authorizations during Phase Two. Interested providers should review FedRAMP’s Phase Two Pilot Eligibility and Participation Criteria.
The FedRAMP 20x transforms authorization logistics by expressing requirements as a set of Key Security Indicators (KSIs) mapped to the underlying NIST SP 800-53 Rev. 5 controls and designed to automate validation.
The 20x program modernizes the Low baseline through initiatives such as:
- Machine-readable security packages using standardized schemas
- Automated validation of KSIs to streamline review
- Programmatic submission of evidence to the FedRAMP PMO
- A more predictable and outcome-focused authorization process
Traditionally, LI‑SaaS and other low-impact systems require a federal agency sponsor to review their security package and issue an Authority to Operate (ATO), which can be time-consuming. To reduce this dependency, the FedRAMP 20x Phase One pilot allows vendors to obtain a 12-month Low authorization directly from the FedRAMP Program Management Office (PMO) without a sponsor.
After that, agencies may choose to issue an ATO. CSPs can also eventually transition to a Moderate or High level. Note that a scaled 20x model for High impact systems has not yet been announced as of writing.
Here’s a comparison between FedRAMP Low and FedRAMP 20x key differences:
How to prepare for FedRAMP Low authorization
Approaching the authorization process methodically can make the process smoother. Here are the steps to follow under the standard Rev. 5 process used for FedRAMP Low authorizations:
- Determine if you qualify for FedRAMP Low or LI-SaaS: Use a FIPS 199 assessment to confirm that you should pursue the Low baseline. Determine your authorization boundary, detailing what parts of the system are in scope.
- Conduct a gap analysis vs. NIST 800-53: Compare your current security posture against required NIST 800-53 controls to identify missing practices, policies, and safeguards.
- Address the gaps: Remediate the control gaps uncovered. Draft or update the missing policies and procedures to create the foundation for your SSP.
- Engage a 3PAO for formal assessment: Hire a 3PAO to conduct a formal independent security assessment. They’ll attest if you’ve properly implemented the controls and then issue the Security Assessment Report (SAR).
- Submit the authorization package: Compile your SSP, SAR, and other relevant documentation and submit it to your sponsoring agency for review. The agency verifies the package and decides whether to issue the FedRAMP Low ATO.
- Automate evidence collection and monitoring: Once authorized, use automation tools to streamline evidence collection, continuous monitoring, and reporting to maintain compliance.
Note: The steps above reflect the traditional, agency-sponsored FedRAMP Low process under NIST 800-53 Rev. 5. FedRAMP 20x follows a distinct authorization model with different patterns, automation workflows, and validation approach. For Low authorization under 20x, see our dedicated FedRAMP 20x guide.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
FedRAMP Low authorization cost and timelines
The FedRAMP Low may cost less than Moderate or High authorization, but it’s still a notable investment of a team’s time and resources.
The overall cost can be broken down into two segments:
- Initial costs (pre-certification, gap remediation, and authorization): $500,000 to $1,000,000
- Annual costs (maintenance and monitoring): $150,000 to $250,000
The Low authorization process can take up to 12–18 months. It depends on your readiness and agency sponsorship, such as how fast you’ll secure one, their capacity, and engagement terms.
For cloud-native solutions that don’t store PII, LI-SaaS could be a more economical solution. It is usually less expensive. The lighter validation requirements may enable you to complete it in a few months, which is distinctly faster compared to a year or more required for the Low baseline.
Regardless of which authorization you pursue, using a compliance solution such as Vanta can help you proceed with more structure and confidence.
Achieve guided FedRAMP Low readiness with Vanta
Vanta is a robust agentic trust platform that supports complex compliance and assurance programs with automated workflows, built-in resources, and continuous monitoring. The platform maps many FedRAMP requirements into easy-to-manage, actionable tasks, reducing the guesswork for still-maturing teams.
Vanta automates evidence collection through integrations with 400+ solutions. You can also track the progress of actions, evidence, and milestones in a unified dashboard and remediate gaps proactively for faster readiness.
Here are some of the key features of Vanta’s dedicated FedRAMP product:
- Pre-built templates mapped to FedRAMP
- Accessing and monitoring third-party vendors
- AI-powered policy management
- Access to the Vanta partner network to find a 3PAO and consultants
- Continuous monitoring to support post-authorization obligations
- FedRAMP 20x pilot support
Book a custom demo to watch Vanta FedRAMP in action and discuss tailored solutions.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
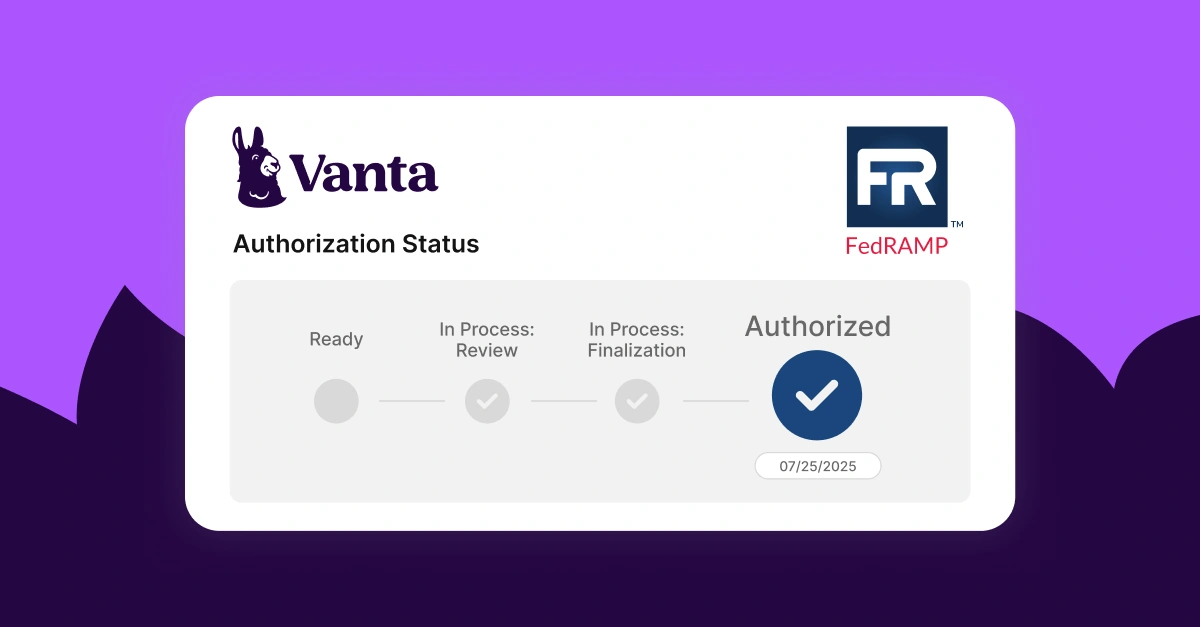
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




