FedRAMP requirements
FedRAMP requirements: A checklist guide for each baseline

Looking to streamline the work for FedRAMP compliance?

The Federal Risk and Authorization Management Program (FedRAMP) establishes standard security requirements for cloud solutions used by US federal agencies. Because cloud systems handle data with varying levels of sensitivity, the required security controls and measures differ based on the applicable impact level.
FedRAMP requirements are defined by whether the underlying cloud system falls under the LI-SaaS (tailored Low), Low, Moderate, or High baseline. These baselines are derived from the Federal Information Processing Standards (FIPS 199) and reflect the risk of loss to the confidentiality, integrity, and availability of federal data and services.
In this guide, we’ll clarify the requirements for each baseline and break down key controls and documentation expectations so you can scope your FedRAMP authorization path confidently.
What are FedRAMP compliance requirements?
FedRAMP compliance requirements are derived from and tailored based on NIST 800-53 (Rev. 5). NIST splits controls into 20 families that cover areas ranging from access control to system and information integrity. Each FedRAMP baseline requires a specific set of controls and procedural expectations drawn from these families.
Here are some key control families with sample controls:
Achieving FedRAMP authorization also requires submitting a formal documentation package with artifacts that demonstrate how you implement and maintain relevant controls. The four documents of the core package are:
- The System Security Plan (SSP): Details the system boundary and compliance elements like control implementation, data flows, and system architecture
- Security Assessment Plan (SAP): Outlines the scope, timeline, and methods a Third-Party Assessment Organization (3PAO) uses to test controls
- Security Assessment Report (SAR): Summarizes the 3PAO’s findings following a formal assessment
- Plan of Action & Milestones (POA&M): Lists identified gaps and details the methods, resources, and timelines required to remediate them
The FedRAMP PMO reviews the package for program consistency, while the sponsoring agency’s Authorizing Official (AO) evaluates residual risk and issues the Authority to Operate (ATO).s. FedRAMP also emphasizes Continuous Monitoring (ConMon) after achieving authorization. Cloud service providers (CSPs) must provide regular updates, typically monthly, to demonstrate that their controls remain effective and that vulnerabilities are regularly addressed.
Pro tip: While FedRAMP requirements are documentation-heavy and time-intensive, modern agentic compliance solutions like Vanta can further streamline the process by automating key aspects of continuous monitoring and evidence collection, helping teams sustain long-term compliance.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
FedRAMP requirements across different baselines
FedRAMP requirements vary across the Low, Moderate, and High baselines. To reflect differences in data sensitivity, organizations implement proportionally stricter controls and undergo broader 3PAO assessments.
The Low-Impact SaaS (LI-SaaS) baseline is also an important part of the conversation. While derived from the FedRAMP Low baseline, LI-SaaS is tailored for SaaS systems that handle the least sensitive federal data and present minimal risk in the event of compromise. It also streamlines certain procedural requirements, which is why we’ve covered it separately in the table below, even though it’s not a standalone baseline.
*The authorization timeline depends on system complexity and existing control maturity.

1. FedRAMP Low and LI-SaaS requirements
The low-impact designation is used for cloud services that handle low-risk federal data, where a compromise would have only a limited adverse effect on an agency’s operations, assets, or individuals.
In-scope systems include collaboration tools, survey applications, and public-facing websites that typically don’t handle sensitive information. The type of platform doesn’t alone qualify it for the Low baseline. Many tools, applications, and dashboards often qualify as Moderate due to handling Controlled Unclassified Information (CUI), authentication credentials, or mission-related information. The key is performing a FIPS 199 assessment early to correctly determine your true impact level and avoid under-scoping your FedRAMP path.
To achieve Low Impact authorization, you must implement the baseline 156 controls derived from NIST 800-53 (Rev. 5). These focus on safeguarding the confidentiality, integrity, and availability of information, without requiring the same rigor of documentation and testing as the higher tiers.
LI-SaaS is a tailored subset of the low-impact tier, intended for SaaS platforms that process only public-facing information and no PII beyond login credentials. It retains the full 156 Low controls, but reduces assessment burden by limiting independent testing to 66 controls and allowing the remaining 90 controls to be addressed through CSP attestation.
LI-SaaS and Low can be used as a stepping stone when pursuing FedRAMP, allowing you to gradually mature control implementations.
FedRAMP Low compliance checklist
Note: Our sample checklists assess baseline readiness and alignment and are for reference only. They do not replace a formal assessment or authorization decision.
2. FedRAMP Moderate requirements
A moderate impact is the most commonly assigned baseline, designating systems where data security incidents could result in serious financial and operational consequences. These typically include:
- HR/payroll platforms
- Case management
- SaaS and PaaS offerings
FedRAMP Moderate includes data such as CUI, employee PII, and key mission data. Proportional to the increased sensitivity of this information, the baseline controls are broader—covering 323 controls tailored from NIST 800-53 (Rev. 5).
Because of the broader scope, organizations can expect greater effort to achieve and maintain authorization. This includes more extensive assessment and authorization timelines, monthly vulnerability scanning, and POA&M management compared to FedRAMP Low.
In practice, FedRAMP Moderate often involves closer collaboration with a 3PAO. Organizations may choose to undergo a readiness assessment before the formal review. The 3PAO conducts this assessment and documents the findings in a Readiness Assessment Report (RAR). RARs can be prepared for all baselines, but they’re more commonly used for Moderate and High authorizations.
FedRAMP Moderate compliance checklist
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
3. FedRAMP High requirements
High impact is assigned to systems where a data breach could have severe or catastrophic consequences on operations, assets, or individuals. It’s typically used for working with agencies that deal with law enforcement, emergency services, healthcare, and financial data.
Typically, cloud systems operating within such high-risk agencies are also expected to align with sector-specific regulations, such as CJIS for law enforcement or HIPAA for healthcare.
FedRAMP High compliance requirements are at the highest rigor, as you need to implement 410 controls tailored from NIST 800-53 (Rev. 5). That’s significantly more than Moderate controls, and many impose tighter parameters on how they’re implemented and tested.
Depending on your control maturity, compliance with FedRAMP High can take up to a year or more, with longer audit timelines, higher remediation costs, and closer scrutiny from 3PAOs.
FedRAMP High compliance checklist
FedRAMP requirements: Challenges and how to mitigate them
Meeting FedRAMP requirements isn’t about completing a checklist but about maintaining operational discipline and high technical accuracy. Some of the most notable authorization roadblocks include:
- Defining your system boundary: One of the biggest missteps in FedRAMP preparation is poorly identifying which components, services, and data flows fall within the authorization scope, since they’re often distributed across multiple environments and dependencies. The goal is to create a well-defined boundary to focus control implementation, streamline documentation, and prevent unnecessary expansion of assessment scope.
- Complex compliance requirements: FedRAMP’s breadth of control implementation and documentation can be overwhelming for smaller or less experienced teams. Break requirements into phases and assign clear ownership to maintain oversight and momentum.
- Substantial implementation costs: Implementing and maintaining FedRAMP controls, policies, and procedures requires significant tooling and resource investments. Perform a readiness assessment early to organize priorities within your budget.
- Ongoing monitoring and frequent audits: ConMon and recurring assessments are required to maintain authorization, and can be time-intensive. Define an ongoing monitoring strategy with a set cadence for review and reporting to stay on track.
Addressing these challenges calls for continuous visibility into ownership and evidence readiness across your security program, which is easier with Vanta’s purpose-built FedRAMP product.
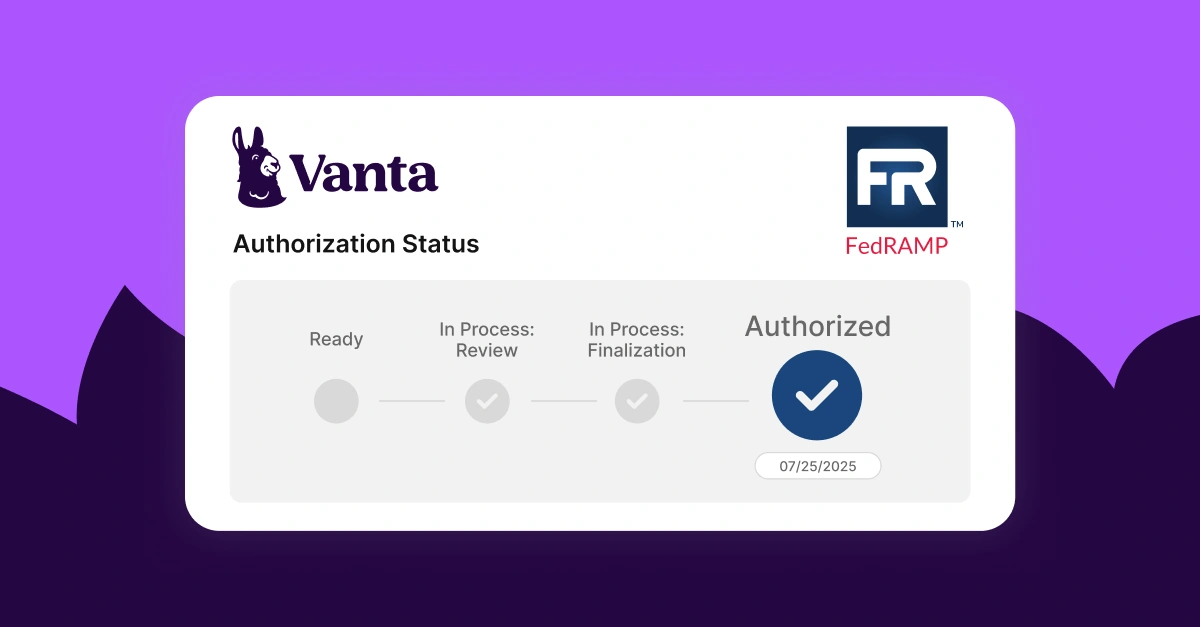
Achieve FedRAMP authorization efficiently with Vanta
Vanta is a leading agentic trust platform that helps organizations streamline and scale FedRAMP authorization and maintenance. Vanta provides step-wise guidance that breaks down the framework’s complex compliance requirements into actionable steps tailored to your impact tier.
Vanta’s FedRAMP product comes with:
- Vendor risk management tools to secure your supply chain
- Automated evidence collection powered by 400+ integrations
- AI-powered policy creation and customization
- A centralized dashboard to monitor your compliance status
- Pre-built, auditor-approved policies that map to FedRAMP baselines
- Ongoing monitoring with on-demand security report generation
If you’re still looking for a 3PAO to partner with, you can use Vanta’s partner network to find the right expert to guide you through the authorization process.
Schedule a demo for a tailored walkthrough on how Vanta’s FedRAMP suite can support your team.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.





