FedRAMP levels
Who needs FedRAMP Moderate, key requirements, and how to prepare

Looking to streamline the work for FedRAMP compliance?

Cloud service providers (CSPs) that want to sell their services to federal agencies must meet the Federal Risk and Authorization Management Program (FedRAMP) security requirements. FedRAMP lets CSPs pursue three security baselines: Low, High, and Moderate, each mapped to the sensitivity of federal data. FedRAMP Moderate by far is the most widely used, making up nearly 80% of the authorized cloud services listings in the FedRAMP Marketplace.
This guide will help you understand FedRAMP Moderate and plan readiness. We’ll cover:
- Who needs FedRAMP Moderate
- Its requirements
- How to prepare for authorization
- Typical costs and timelines
What is FedRAMP Moderate?
FedRAMP Moderate is the mid-level security baseline under FedRAMP. It applies to cloud systems where impact on confidentiality, integrity, or availability of data could cause a serious adverse effect on the federal agency’s assets, people, or operations. FedRAMP draws this model from Federal Information Processing Standard (FIPS) 199 and its three impact levels.
The FedRAMP Moderate baseline is designed for cloud services that handle Controlled Unclassified Information (CUI)—federal data that’s sensitive information but not classified under national security laws. In practice, this typically refers to:
- Departmental budgets
- Law enforcement records
- Contracts
- Personally identifiable information (PII)
Exposure of these records could cause harm to individuals, such as financial fraud or privacy violations, or disrupt government operations, but the harm could be remediated. For example, unauthorized access to a federal employee’s PII could lead to identity theft, and such an impact aligns with the Moderate threshold. By contrast, the High tier covers scenarios where the breach won't just harm individuals but has a severe or catastrophic adverse effect overwhelming to remediate.
Today, FedRAMP Moderate is the most widely pursued authorization, as the majority of federal agencies handle CUI in one form or another.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Who needs FedRAMP Moderate authorization?
Any CSP that plans to collect, store, process, or transmit CUI on behalf of federal agencies must pursue a FedRAMP Moderate authorization. This can apply to both startups and mature organizations, as any CSP that sells in-scope cloud services to a federal agency is expected to be authorized at the applicable impact level.
Here are some cloud systems that typically must comply with FedRAMP Moderate:
- Human resource or payroll platforms
- Case and program management systems
- Financial and accounting tools
- Document management and shared collaboration platforms
- General healthcare and admin solutions
What are the FedRAMP Moderate baseline requirements?
Achieving FedRAMP Moderate requires CSPs to implement and document 323 privacy and security controls across the applicable control families from NIST Special Publication (SP) 800-53 Rev. 5.
These controls must target the in-scope cloud service offering (CSO) that handles federal data. They include both baseline controls and additional enhancements that will be independently evaluated by a third-party assessment organization (3PAO).
A good approach here is to start with areas that have a bigger volume of requirements. Here are some of the main control families with the highest number of controls:
Continuous Monitoring (ConMon) is one of the core obligations under FedRAMP. While it isn’t a standalone NIST control family, it’s an ongoing requirement derived from multiple NIST SP 800-53 controls that a CSP must maintain after receiving its Authority to Operate (ATO).
CSPs must also develop a System Security Plan (SSP) aligned with FedRAMP Moderate, detailing how each control is implemented, maintained, and verified. This document is the main evidence you’ll submit to demonstrate the system’s posture and readiness.
FedRAMP Moderate vs FedRAMP High and Low
The primary difference between the three FedRAMP impact levels lies in the potential impact to federal operations, assets, or individuals if the data or system were compromised. FedRAMP applies the impact definitions from FIPS 199—Low, Moderate, and High—which reflect the severity of harm resulting from a loss of confidentiality, integrity, or availability (CIA).
Moderate level covers systems that handle CUI or other sensitive data, where a CIA compromise would have a serious impact. Here’s how the others compare in terms of data sensitivity:
- Low impact level: Needed for systems that only handle federal data that is publicly available and not sensitive. For example, a website that publishes general announcements
- High impact level: Applicable to systems that store or process highly sensitive data, such as defense systems that contain mission-critical information
As the sensitivity of data increases, so does the number of controls, marking the next major distinction. All FedRAMP impact levels mandate a different number of security controls to meet the expected level of security rigor for the tier. Here’s a snapshot:
These controls are eventually validated by your 3PAO, so that progressively increases the review complexity across tiers. CSPs in scope for Low can also explore the option of pursuing the Low-Impact SaaS (LI-SaaS) baseline. This is a subset of FedRAMP Low with a reduced number of security controls that require 3PAO validation, which can expedite the process.
If you’re handling limited, low-risk CUI and feel conflicted between Moderate and Low baselines, it’s best to check where your agency stands.
How to prepare for FedRAMP Moderate authorization
Here are the main stages to cover when preparing for the FedRAMP Moderate authorization:
- Assess if your organization requires FedRAMP Moderate
- Hire a 3PAO to conduct a readiness assessment
- Implement Moderate-level controls and undergo the formal assessment
- Submit the package to the sponsor agency
- Submit the authorization package to FedRAMP
Note: FedRAMP previously offered two authorization paths: one through individual agencies and another through the Joint Authorization Board (JAB) via the P-ATO process. The JAB route has been phased out between 2024–2025, leaving the streamlined agency-sponsorship model that makes authorization simpler for most Low and Moderate systems.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Step 1: Assess if your organization requires FedRAMP Moderate
First, determine the type of federal data you’ll handle. If your cloud service stores or processes CUI, the Moderate impact level applies to your organization.
The general rule while classifying your data appropriately is to conduct the FIPS 199 impact assessment. Besides that, you can consult your sponsoring agency to ensure you’re in the right category and are working with defined authorization goals.
Step 2: Hire a 3PAO to conduct a readiness assessment
Start this step with a gap assessment to evaluate the current state of your security systems and then document the areas that need updates/remediation. While you can do this with your internal teams, it’s highly recommended to engage a 3PAO to perform a readiness assessment against Moderate baseline controls.
3PAOs offer a collaborative service by helping you identify gaps in your policies, procedures, and controls and remediate them before the formal assessment. This step can be crucial if you’re new to FedRAMP and want to reduce remediation-related delays down the line.
Step 3: Implement Moderate-level controls and undergo the formal assessment
Once you know the scope of remediation, start implementing the relevant controls while maintaining extensive, audit-ready documentation on how each is met.
Particularly, maintaining the SSP is critical as auditors assess both technical deployment and evidence of compliance. Other key activities typically include:
- Establishing policies and procedures aligned with controls
- Configuring systems with the expected security settings
- Organizing evidence for easy access during the formal assessment
Once remediation is complete, your 3PAO will perform the full security assessment and generate the Security Assessment Report (SAR). The SAR and SSP become the core artifacts of your submission package.
Step 4: Submit the package to the sponsor agency
The last step is to submit the authorization package to your sponsoring federal agency. The sponsor agency will then review the system, verify the artifacts to see if controls are properly implemented, and decide whether to issue an ATO.
Once you receive the authorization, plan your continuous monitoring and reporting scope to ensure you sustain the FedRAMP Moderate ATO.
Step 5: Submit the authorization package to FedRAMP
After the sponsoring agency issues an ATO, the CSP must submit the complete authorization package—SSP, SAR, POA&M, attachments, and required forms—to FedRAMP for review and inclusion in the FedRAMP Marketplace.
FedRAMP verifies that the package meets formatting and completeness requirements and establishes the CSP’s continuous monitoring obligations.
Only after this submission is the service officially listed as FedRAMP Authorized and made available for reuse by other agencies.
How much does FedRAMP Moderate cost?
There’s no official government-provided pricing table for FedRAMP Moderate. The cost can vary depending on factors such as:
- Scope complexity
- Tech stack
- The 3PAO you choose
- The size of your system
- Current readiness level
- Requirements of the sponsoring federal agency
Here are the typical cost ranges and what they refer to:
If you’re moving from the Low to Moderate baseline, set aside an initial budget for the transition and then prepare for higher ongoing investment. Both baselines require ongoing cost drivers, including monthly vulnerability scanning, annual reassessment, and detailed POA&M (Plan of Action & Milestones) management, but Moderate would expand the scope and depth of these activities.
How long does it take to get FedRAMP Moderate authorization?
The timeline for FedRAMP Moderate authorization depends on:
- How many of the required controls are already implemented
- How mature your security processes are
On average, the agency authorization takes between 12 and 18 months. The exact duration depends on the sponsoring agency, the scope of your system, and the FedRAMP PMO or agency review queues.
Delays and extended timelines often happen because of incomplete documentation or gaps in security controls. Leveraging compliance automation solutions can speed up the process and reduce human errors—and it also aligns with FedRAMP’s recent push for automation-driven continuous compliance.
Using an automation-first trust platform such as Vanta can streamline time-consuming tasks like collecting evidence and tracking progress. This can make a huge difference in your preparation workflows and resource planning, making it easier to hit FedRAMP Moderate readiness in 6–12 months.
Pursue FedRAMP Moderate authorization efficiently with Vanta
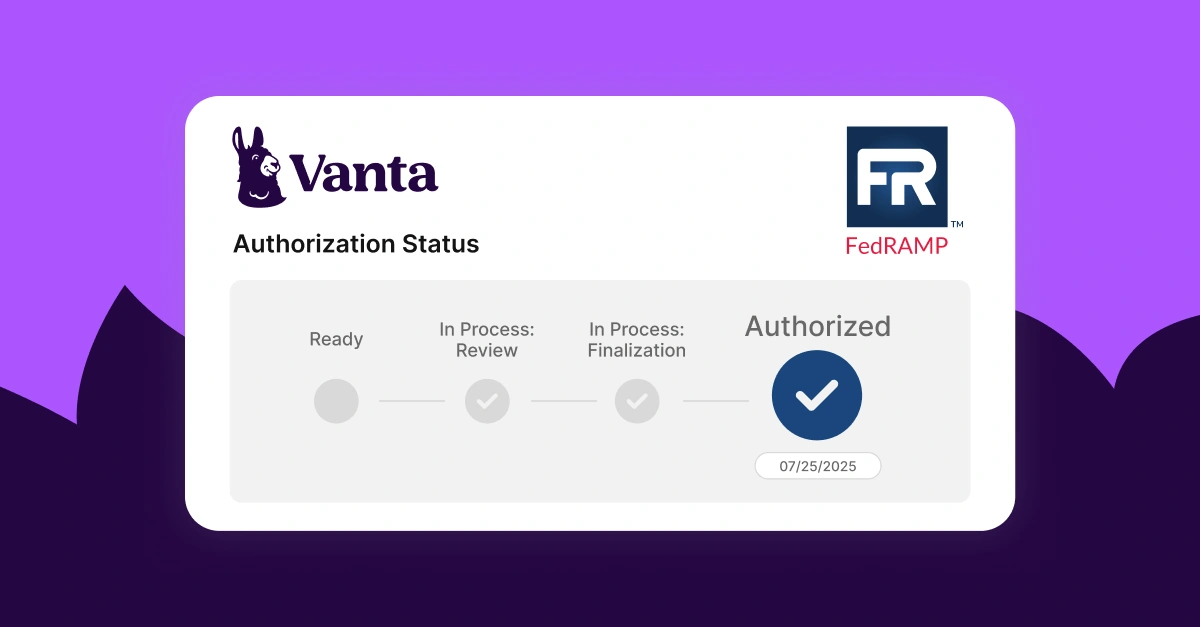
Vanta is a leading agentic trust platform that helps organizations build efficient governance, risk, and compliance programs with automated workflows, evidence collection, built-in resources, and continuous monitoring.
Vanta simplifies FedRAMP authorization across impact levels, taking the stress and guesswork out of it with expert-backed guidance on next steps. Many FedRAMP requirements are already mapped into Vanta, so you can track controls and policies and monitor gaps at every stage. To speed up the evidence collection, Vanta integrates with over 400 apps and platforms to pull in data for centralized visibility.
Here are some core functionalities of Vanta’s FedRAMP product:
- Centralized dashboard to track actions, evidence, and milestones
- Pre-built, auditor-approved document templates
- AI-powered policy management
- Vendor risk management support
- Vanta partner network to find a 3PAO to guide you through the authorization process
- Continuous monitoring to support post-authorization obligations
Schedule a custom demo today to have an expert show you how the FedRAMP product can streamline your workflows.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




