FedRAMP levels
FedRAMP LI-SaaS: Who needs it, requirements, and how to prepare

Looking to streamline the work for FedRAMP compliance?
Selling cloud services to the US government often requires significant investments to align with the Federal Risk and Authorization Management Program (FedRAMP). FedRAMP authorization requirements are based on the impact levels from FIPS 199—Low, Moderate, and High—which indicate how much security expectations should scale based on the potential impact of a loss of confidentiality, integrity, or availability.
For some SaaS offerings, the effort and cost of authorization with the three FedRAMP baselines would often outweigh the potential contract value. To address this, FedRAMP introduced the Low-Impact SaaS (LI-SaaS), a tailored authorization option under the FedRMAP Low baseline, designed specifically for eligible systems that access low-risk government data.
In this guide, we’ll break down:
- What qualifies under LI-SaaS
- LI-SaaS compliance requirements
- Steps to earn LI-SaaS authorization without over-engineering security
What is LI-SaaS?
FedRAMP LI-SaaS or FedRAMP Tailored is a tailored variation of the FedRAMP Low impact baseline, intended for SaaS applications that only handle limited, low-risk federal information. This baseline was created to lower the barrier to entry for vendors and make the authorization process more efficient compared to FedRAMP Low.
The LI-SaaS baseline works like a subset of the Low baseline but with a lighter and more streamlined assessment process. FedRAMP Low requires 156 controls to be implemented, which are later tested and validated by a Third-Party Assessment Organization (3PAO). The cloud service provider (CSP) maintains extensive documentation to support each control.
LI-SaaS also asks for 156 controls—but a 3PAO needs to test only 66; the CSP can attest the remaining 90 controls. The attested controls are typically inherited from using other FedRAMP Authorized systems.
The documentation requirements under LI-SaaS are also less intensive, which reduces the overall burden on 3PAOs and expedites the authorization process.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Who needs to comply with LI-SaaS?
LI-SaaS is intended for lightweight SaaS applications that don’t store personal identifiable information (PII) beyond login credentials. The most common use cases include:
- Scheduling tools
- Communication platforms
- Project trackers
- Electric vehicle (EV) charging platforms
These examples are illustrative; eligibility still primarily depends on the system’s authorization boundary and the types of data it handles. If your service processes any low-risk data beyond login credentials, you’ll most likely have to meet the criteria for Low.
If your systems handle controlled unclassified information (CUI) whose breach would have serious adverse effects, you’ll most likely map to Moderate, depending on your FIPS 199 impact assessment.

What are the core LI-SaaS compliance requirements?
FedRAMP, and by extension, LI-SaaS compliance requirements are based on NIST SP 800-53 (Rev. 5) controls, organized into control families which cover different aspects of data security. The table below illustrates key representative families:
Many of these requirements also overlap with other industry-relevant frameworks, such as ISO 27001 and SOC 2. In practice, you can use existing controls as attestation evidence for LI-SaaS implementation, but you’ll still need to plan for FedRAMP-specific tasks like maintaining the System Security Plan (SSP), Plan of Action and Milestones (POA&M), and continuous monitoring (ConMon).
How to prepare for LI-SaaS authorization: 7 steps
Here are the seven steps you should take to achieve and maintain FedRAMP LI-SaaS authorization:
- Scope system categorization (Low-impact)
- Map controls to NIST 800-53 (Rev. 5)
- Start creating the SSP and supporting policies
- Implement baseline security controls
- Engage a 3PAO for third-party review
- Submit the package to the sponsoring Agency for Authority to Operate (ATO) issuance, then submit the approved package to FedRAMP for Marketplace listing
- Maintain ConMon
In ideal conditions, LI-SaaS readiness can take around six months, but for most CSPs, a year is a more realistic timeline. While authorization adds another layer, FedRAMP review cycles have been moving at a relatively steady pace recently.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Step 1: Scope system categorization (Low-impact)
The first step is to confirm your organization qualifies for a Low-impact level categorization under FIPS 199. Conduct an internal assessment to scope all relevant in-boundary assets, including systems, data flows, and cloud hosting environments, to identify what federal data is handled and who accesses it.
Traditionally, this boundary included all components of the system that were in scope for federal data. Under FedRAMP Rev. 5’s Minimum Assessment Scope (MAS) guidance, CSPs can optionally adopt a narrower, risk-based boundary definition process that includes only those information resources likely to handle federal customer data or impact its confidentiality, integrity, or availability.
Next, verify that you process and retain only the least amount of PII. To qualify for the LI-SaaS baseline, you must answer all of the following questions with a Yes when doing your assessment:
- Does the service operate in a cloud environment?
- Is the cloud service fully operational?
- Is the cloud service a Software as a Service (SaaS), as defined by NIST SP 800-145, The NIST Definition of Cloud Computing?
- Does the cloud service contain no personally identifiable information (PII), except as needed to provide a login capability (e.g., username, password, and email address)?
- Is the cloud service low-security-impact, as defined by FIPS PUB 199, Standards for Security Categorization of Federal Information and Information Systems?
- Is the service hosted on a FedRAMP-authorized PaaS/IaaS (recommended for control inheritance) or does the CSP provide/operate the underlying cloud infrastructure meeting the applicable controls?
If any of the scoped assets introduce a higher impact level, the entire system must be categorized at a higher tier, and FedRAMP LI-SaaS no longer applies.
Step 2: Map controls to NIST 800-53 (Rev. 5)
Map your existing security controls to the LI-SaaS tailored baseline designed considering the NIST 800-53 (Rev. 5). This requires an internal assessment to:
- Determine how your existing technical and administrative controls compare to LI-SaaS requirements
- Map controls that can be inherited from FedRAMP Authorized CSP’s or other shared services
- Identify control gaps based on your existing system architecture and inheritance strategy
Accuracy during this step is crucial as it directly impacts the timelines, investments, and expectations for the rest of the readiness process.
Step 3: Start creating the SSP and supporting policies
Once you’ve established a control roadmap, start drafting your System Security Plan (SSP) to document the intended control implementations within the LI-SaaS boundary. The SSP serves as the main reference point for how each control is applied, configured, and maintained, and is supported by artifacts such as:
- Policies and procedures
- Architecture and data flow diagrams
- Control Implementation Summary (CIS)
- Customer Responsibility Matrix
- Evidence of automated monitoring
The policies and procedures you draft must support each control family, such as configuration management, contingency planning, and incident response.
When preparing an SSP for LI-SaaS, you must rely on FedRAMP’s prebuilt template for more precise guidance. The SSP will be finalized in the next step when you implement the controls.
Step 4: Implement baseline security controls
Set up the documented controls across the authorization boundary. This can involve processes such as updating outdated policies, strengthening existing controls, upgrading infrastructure, and conducting additional stakeholder training.
Update your SSP as you implement controls, which keeps your documentation current and third-party audits smoother. If your service inherits controls from a FedRAMP-authorized PaaS or IaaS, you must clearly document the source of inheritance and your remaining responsibilities in the SSP.
Common mistakes at this stage include treating the implementation like a checkbox exercise and over-engineering controls. You could miss required evidence, due to a lack of internal understanding of how LI-SaaS scales down FedRAMP requirements.
An effective way to approach these issues is to monitor readiness with compliance and trust automation platforms like Vanta. You can improve governance with Vanta by automating evidence collection, mapping existing controls to LI-SaaS, as well as giving your teams the clarity and structure to move towards authorization faster and with confidence.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Step 5: Engage a 3PAO for third-party review
You must undergo an evaluation by a FedRAMP-accredited 3PAO as part of the formal authorization process. The 3PAO will provide you with a Security Assessment Plan (SAP) that outlines:
- The scope of the assessment
- Testing methodologies
- Roles that will be tested
- Assumptions
- Testing plan and schedule
Before the formal authorization audit, the 3PAO may conduct an optional readiness assessment to evaluate the maturity of control implementation and identify any gaps. The findings are documented in the Readiness Assessment Report (RAR), which CSPs can use to prioritize remediation before entering the formal authorization phase.
The 3PAO’s final findings are then documented in a Security Assessment Report (SAR), which will then be transposed into a POA&M to track remediation activities.
Step 6: Submit the package to the sponsoring agency
You then submit your authorization package to your sponsoring federal agency, including the System Security Plan (SSP), Security Assessment Report (SAR), Plan of Action and Milestones (POA&M), and any supporting artifacts. If a readiness assessment was performed earlier, the Readiness Assessment Report (RAR) may also be included for context.
The FedRAMP PMO will also review your material for program consistency and alignment with FedRAMP LI-SaaS, but doesn’t grant the ATO. The final decision is made by the Authorizing Official (AO) of your sponsoring agency, who also reviews your submission to verify it meets the agency criteria.
Note: A SaaS that meets LI-SaaS criteria can optionally pursue the automation-driven 20x pilot for Low baseline, if under scope. The LI-SaaS authorization pathway is agency-sponsored, but the 20x authorizations can be issued directly by the PMO for 12 months without an agency sponsor. This program uses machine-readable packages and automated validation of Key Security Indicators (KSIs) to streamline the process, making authorization faster, more predictable, and less dependent on manual agency reviews.
Step 7: Maintain ConMon
After obtaining an ATO, CSPs must implement ConMon and submit deliverables at a set cadence—typically monthly—to maintain their authorization status. The deliverables are submitted to the sponsoring agency’s AO and include potential remediation actions, POA&M updates, and vulnerability test results.
As additional federal agencies begin consuming the same authorized service, CSPs may transition to a Collaborative Continuous Monitoring (CCM) approach. CCM allows CSPs to coordinate ongoing monitoring and reporting across multiple agencies, reducing duplicative submissions while maintaining consistent visibility into system risk and changes.
The documentation reviews, vulnerability testing, and remediation tracking under FedRAMP can be time-consuming and divert your teams from more strategic tasks. Use solutions like Vanta to streamline your ConMon and ongoing documentation efforts.
Fast-track FedRAMP LI-SaaS authorization with Vanta
Vanta is a leading agentic trust platform that helps organizations approach compliance and governance frameworks, as well as risk management practices, systematically through a unified dashboard.
With Vanta, you can achieve FedRAMP compliance efficiently with step-by-step guidance that breaks down complex requirements into actionable steps. You access agentic workflows to address control gaps and run continuous monitoring.
Vanta’s dedicated FedRAMP product has numerous features to streamline compliance, such as:
- Automated evidence collection powered by 400+ integrations
- Vendor risk management tools
- AI-powered policy drafting and customization
- Pre-built, auditor-approved policies that map to FedRAMP baselines
- Continuous monitoring through a single dashboard
If you’ve already achieved compliance or are pursuing other industry-relevant frameworks, such as SOC 2 or ISO 27001, Vanta’s cross-mapping feature can help you reuse the evidence where relevant. The platform also offers a public Trust Center to demonstrate all your compliance and security efforts in one place.
Schedule a custom demo to see how Vanta can streamline FedRAMP compliance for your team.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
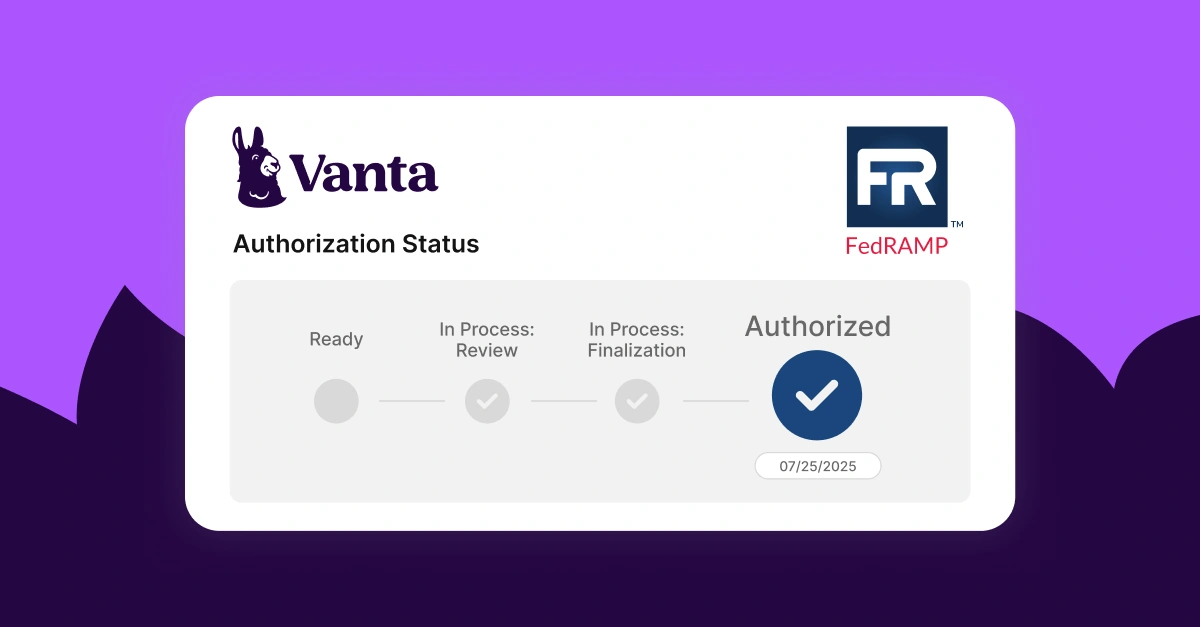
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




