FedRAMP requirements
How to write a watertight FedRAMP System Security Plan (SSP)

Looking to streamline the work for FedRAMP compliance?

Federal Risk and Authorization Management Program (FedRAMP) authorization is driven by a robust authorization package that attests to your current security posture: what’s documented, validated, and defensible. Federal agencies and the FedRAMP Program Management Office (PMO) use it to determine whether you qualify for an Authority to Operate (ATO).
The System Security Plan (SSP) is a core artifact within this package. The SSP is a foundational, living document that provides an authoritative description of your system’s security posture and how FedRAMP requirements are implemented within the authorization boundary.
Developing an SSP in alignment with FedRAMP requirements is a critical task during readiness, authorization, and Continuous Monitoring (ConMon). This guide will break down how to write and maintain an SSP, covering its core contents as well as drafting challenges and best practices.
What is a FedRAMP System Security Plan?
The SSP is a formal, authoritative document that describes how a cloud service protects US government data. It maps out the system boundary and in-scope components and data flows, and describes how every control is implemented, monitored, and maintained. An SSP typically includes:
- Implemented and planned security controls under NIST SP 800-53 Rev. 5
- Data flows and mappings
- System architecture within the boundary definition
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Who uses the SSP?
An SSP is very blueprint-like and serves as a single source of truth for all stakeholders, including the cloud service provider (CSP) and federal authorities.
FedRAMP reviewers, including the sponsoring agency’s authorizing official (AO), the independent third-party assessment organization (3PAO), and the FedRAMP PMO, use the SSP, in conjunction with assessment results and ConMon data, to evaluate risk, verify control implementation and monitoring practices, and decide whether the system is secure enough for government use.
Is SSP mandatory for all FedRAMP tiers?
Creating an SSP is mandatory for all FedRAMP baselines, including LI-SaaS (tailored Low) Low, Moderate, and High. But because the higher tiers have more stringent requirements, the resulting SSP is also more comprehensive, even running over 800 pages for complex systems and control mappings.
How long does it take to prepare an SSP?
System complexity is also reflected in SSP preparation timelines. Preparing an initial SSP for FedRAMP Moderate typically takes around eight weeks if done internally. Experienced teams and consultants can usually reduce the time to 4–5 weeks. For Low and High baselines, this can swing to 1–2 weeks over or under, respectively.
FedRAMP 20x significantly changes SSP preparation and timeline logistics. Instead of a long, control-by-control narrative, CSPs organize the SSP into a machine-readable package centered around Key Security Indicators (KSIs) with linked evidence and automated validations where possible. The 3PAO then attests to each KSI validation in the same machine-readable file, similarly to a System Assessment Report (SAR), leading to an efficient authorization cycle.
FedRAMP 20x is still a pilot initiative and concrete, repeatable SSP preparation timelines have not yet been established.
What goes into an SSP?
CSPs are required to use the official FedRAMP template to write their SSP. As of January 2026, it’s available as an Excel workbook with 12 sheets. We’ve grouped its contents into seven categories for easier understanding:
- System identification and overview
- Roles and responsibilities
- External dependencies and control inheritance
- System architecture
- Control implementation summary
- Ongoing monitoring
- SSP appendices
1. System identification and overview
Name and describe your system’s authorization boundary, purpose, deployment model, and the types of federal data it’ll handle to anchor the rest of your SSP. Identify the FedRAMP impact baseline based on the FIPS 199 security categorization. Next, define the system authorization boundary, stating which components, services, and integrations are in and out of scope. A clearly defined boundary ensures that control implementation, inheritance, and 3PAO assessment scope are unambiguous.
The data for this component of your SSP should be derived from internal discovery and validation activities.
2. Roles and responsibilities
Several sections of the SSP ask you to establish governance: who’s responsible for the cloud system’s security and compliance throughout its lifecycle. You first designate a system owner, and then define other roles for other components like system maintenance, procurement decisions, integrations, or modifications.
Assigning ownership across security, engineering, compliance, and operations helps ensure controls are implemented consistently and maintained over time. This exercise ensures better coordination with 3PAOs and less ambiguity during assessments.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
3. External dependencies and control inheritance
This section rounds up external services and system dependencies, including components that have FedRAMP authorization and those that don’t. Describe every tool, platform, and third-party app you use, and outline how you secure data flows between those systems.
Next, document any controls that you’ve inherited from infrastructure providers, such as Infrastructure as a Service (IaaS) and Platform as a Service (PaaS) vendors. A Control Implementation Summary and Customer Responsibility or Shared Responsibility Matrix are required attachments for illustrating ownership to reviewers.
4. System architecture
This section involves visually representing your system's authorization and trust boundaries, networks, and data flows via illustrated diagrams. Conduct an assessment and inventory all relevant assets to ensure your graphs and diagrams accurately reflect your system’s structure and security posture.
When graphing your data flows, list all system components—including servers, storage, and key applications—and specify your hosting environment. For sensitive flows, also specify the encryption status (in transit and at rest) and other security mechanisms.
5. Control implementation summary
Next, you should provide a detailed overview of each required FedRAMP control, which typically makes up the majority of your SSP. As per experts, every control summary should be modeled after six core questions:
When creating this section, you must write clear control descriptions. This means you must:
- Identify the control
- State its objective
- Describe implementation
- List artifacts that prove compliance
- Define monitoring
- Specify inheritance
Tip: The scope of your control implementation summary depends on your impact tier and system complexity. You can make the process smoother with agentic tools like Vanta to auto-populate your SSP.
6. Ongoing monitoring
Ongoing monitoring is a core requirement of FedRAMP authorization—part of appendix N in the SSP, Continuous Monitoring Plan. It’s a critical indicator of your security program’s operational maturity and ability to address evolving risks.
This section should document your ConMon approach, including artifacts such as risk assessment findings, incident reports, internal audits, and system change logs, which collectively provide a comprehensive picture of your control performance. You should also report how findings are tracked, remediated, and validated over time.
7. SSP appendices
SSP appendices are supporting documents that provide detailed information for the record. They contain relevant granular data that would’ve overwhelmed the main body of your document.
There are 17 appendices A–Q, briefly presented below:
It’s best to start gathering appendices documentation early in the drafting process, as information gaps here can cost you the ATO.
Common SSP drafting mistakes to avoid
Watch out for these common mistakes when preparing the SSP:
- Poor scope definition: Your SSP will be incomplete without a clear scope definition, which can result in costly delays, rework, and coverage gaps. Vague framing of any kind reduces the document’s credibility.
- Inadequate documentation: Missing policies, diagrams, inventories, and workbooks early on slows down SSP development.
- Weak stakeholder mapping: Leaving out departments, such as engineering, sales, or security, creates blind spots in your control implementations, leading to often longer and costlier audit cycles.
- Control implementation drift: A common pitfall is documentation that does not align with actual operational, policy, or technical implementation practices. Reviewers routinely flag such discrepancies, which delays authorization and triggers a deeper investigation into controls.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Best practices for developing your FedRAMP SSP
The key to drafting a strong SSP is to think like a 3PAO reviewer and anticipate questions and evidence requests in advance. Follow these practices to make the process smoother:
- Use FedRAMP templates: Rely on official templates, where available, to follow the expected structure and required sections.
- Use specific language when phrasing controls: When writing control descriptions, use clear, consistent language and provide complete narratives. Answer the who, what, when, where, why, how, and reference supporting documents.
- Make documentation consistent: All artifacts should align and cross-reference accurately. For example, the SSP should map to the Control Implementation Summary, while the SAR should map to your POA&M.
- Establish a review cadence: Regularly review and update your SSP, especially after any changes to your systems or risk environment, so it accurately reflects your current posture.
- Use automation: Automation solutions can automatically gather the required evidence, track changes in real-time, and keep your SSP consistent with real-world execution.
Streamline FedRAMP documentation with Vanta
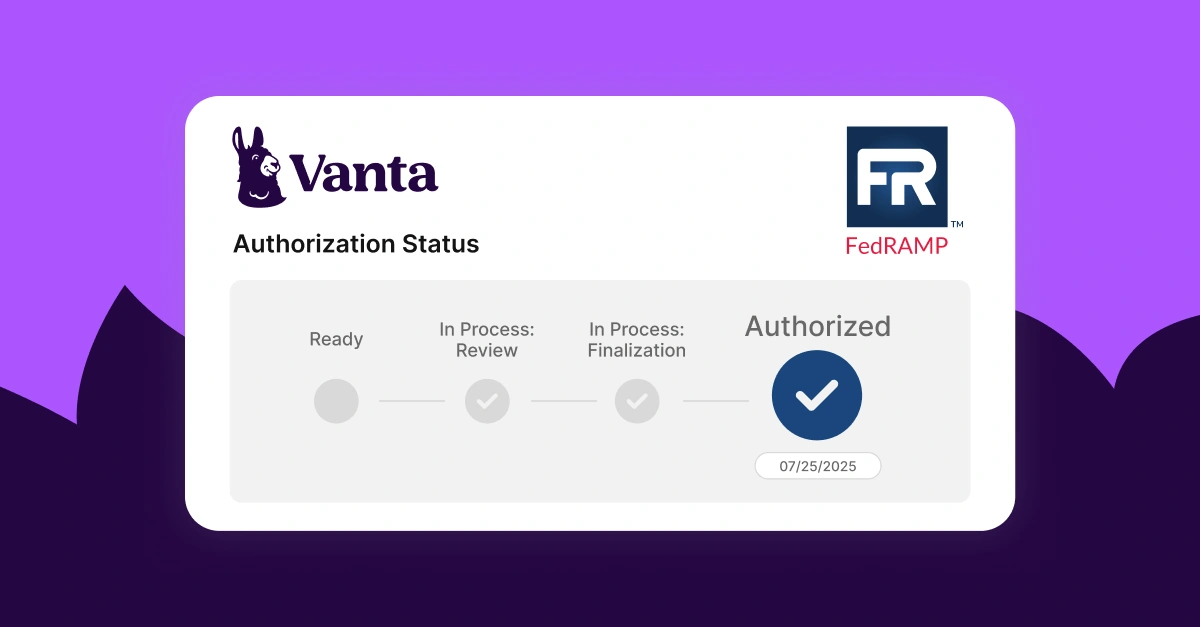
Vanta is an agentic trust platform that helps organizations achieve and maintain FedRAMP authorization efficiently.
With Vanta, you can accelerate documentation preparation by generating FedRAMP-aligned policies, populating your SSP, and managing your POA&M through templates and automation that significantly reduce manual overhead. Ongoing compliance also becomes easier when monthly vulnerability scans and POA&M updates are automated and centrally tracked, keeping you on track for annual reassessments.
Vanta operationalizes many FedRAMP requirements, turning them into actionable tasks tailored to your impact tier (LI-SaaS, Low, Moderate, or High). Key features of the FedRAMP suite include:
- Automated evidence collection through 400+ integrations
- Continuous monitoring with a centralized dashboard
- Auditor-approved pre-built policies that map to FedRAMP baselines
- AI-assisted policy creation and customization
- Vendor risk management tools to secure your supply chain
You can also use Vanta’s partner network to find knowledgeable 3PAOs who guide you through the authorization process, help resolve issues, and keep your ATO timeline moving.
Schedule a custom demo for a visual walkthrough.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
FAQs
Do I need a separate SSP for each environment?
You need one SSP per authorized system boundary (cloud service offering). If you have multiple environments (e.g., development/testing/production) within the same boundary and governed by the same controls and processes, you can cover them in a single SSP.
If the environments have different control boundaries or materially different controls, you’ll need separate SSPs or authorizations or to re-scope accordingly.
Who approves the SSP: The 3PAO or FedRAMP PMO?
Neither the 3PAO nor the FedRAMP PMO “approves” the SSP formally; it’s rather about assessing and accepting.
The SSP is assessed by an accredited 3PAO who reports on it through a SAP and SAR. It’s also reviewed by the FedRAMP PMO for program compliance and quality, but the AO at the sponsoring agency makes the ultimate authorization decision, accepting the package and providing the ATO.
How often should I update the SSP?
The SSP should be treated as a living document. At a minimum, it should be updated: prior to annual assessments following an incident, or after any significant changes to your systems or compliance environment.
How can automation tools export the FedRAMP SSP in the required format?
Automation tools help streamline FedRAMP SSP management, including populating and exporting it in the required format. Some solutions also support the export of the SSP and other artifacts in machine-readable documentation formats such as the Open Security Controls Assessment Language (OSCAL), which is acceptable by FedRAMP.
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




