Introduction to FedRAMP
What is FedRAMP? A 101 guide to the compliance and authorization process

Introduction to FedRAMP
Looking to streamline the work for FedRAMP compliance?
.png)
Cloud services are indispensable in this day and age, even for U.S. federal agencies that work with vast amounts of data. The nature of the data is often sensitive and mission-critical, which means that any cloud provider handling government information must meet stringent security expectations consistently.
The U.S. government introduced the Federal Risk and Authorization Management Program (FedRAMP) as a unified framework to help cloud service providers (CSPs) implement appropriate security measures when working with federal agencies. This guide will help you understand and navigate the key aspects of FedRAMP compliance, including:
- Who governs FedRAMP
- Why compliance matters
- FedRAMP impact tiers
- The authorization process
What is FedRAMP?
FedRAMP is a U.S. government initiative that provides CSPs with a standardized framework for security assessment, authorization, and continuous monitoring. The goal is to provide federal agencies with a repeatable process for validating and adopting secure cloud solutions fit for handling government data.
FedRAMP requirements are based on the security and privacy controls for NIST SP 800-53 (Rev. 5), adapted for cloud environments. The number and rigor of controls a CSP must implement are determined by the system’s overall impact level, which reflects the potential harm to the confidentiality, integrity, and availability of federal data and services.
To work with federal agencies, CSPs must complete the FedRAMP authorization process and obtain an Authority to Operate (ATO), which confirms that they meet the required security criteria. While non-compliance doesn’t result in fines, it certainly blocks a CSP from serving federal clients.
FedRAMP closely aligns with other industry frameworks, such as SOC 2, ISO 27001, and Government Risk and Authorization Management Program (GovRAMP, fka StateRAMP). Still, they’re not interchangeable, as FedRAMP is prescriptive and tied to NIST 800-53 requirements and federally-mandated continuous monitoring obligations.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Who governs and enforces FedRAMP?
FedRAMP isn’t run by a single, central governing body. Instead, its governance and execution are split between several entities. Here’s an overview:
Why FedRAMP compliance matters
FedRAMP compliance holds significance for both federal agencies and cloud service providers.
For federal agencies, FedRAMP makes it easier to identify CSPs with a NIST-aligned and independently validated security posture, which streamlines and shortens the procurement cycle.
FedRAMP authorization signals security maturity and trustworthiness for CSPs. Before FedRAMP existed, cloud providers often had to undergo separate assessments for each federal customer, producing custom documentation and responding to unique control interpretations. FedRAMP standardizes this process, reducing repeated assessments and lowering long-term compliance burden.
Once authorized, a CSP’s security package is published in the FedRAMP Marketplace, giving agencies centralized visibility into its authorization status. This enables reuse, where multiple agencies can review and rely on the same authorization to grant their own ATOs—expanding the CSP’s ability to serve a broad range of federal customers.
What are the FedRAMP baselines?
FedRAMP uses three security impact baselines—Low, Moderate, and High—derived from FIPS 199 impact levels. These baselines determine the set of NIST SP 800-53 Rev. 5 controls a cloud service provider must implement based on the potential impact a loss of confidentiality, integrity, or availability could have on government operations.
Each tier has maps to a set of mandatory NIST 800-53 controls, with higher levels requiring more comprehensive protections.
FedRAMP authorization process: A brief overview
FedRAMP authorization specifics depend on your cloud system and partnering federal agency, but the general process typically involves these steps:
- Prepare your organization for FedRAMP
- Secure an agency sponsor and categorize your system
- Undergo product development
- Spend time on pre-assessment and pre-authorization planning
- Conduct an initial assessment—and prepare for agency authorization
- Undergo agency authorization and PMO review
- Prepare for ongoing annual assessments
Step 1: Define scope and impact level
First, inventory all of your in-scope assets, including systems, applications, physical locations, stakeholders, and hosting environments. You can use data flow diagrams to determine where you store federal data and who has access to it.
With this information, you’ll categorize your organization’s impact level under FIPS 199 by determining the potential impact of loss of confidentiality, integrity, or availability. Your overall impact level is the highest rating among the three, and it defines which FedRAMP baseline you must implement.
After the categorization, conduct internal risk assessments to identify and prioritize risks based on their likelihood and potential impact on operations. Invite IT and security stakeholders early in the process to align on more vague areas like data sensitivity scope and system gaps.
Step 2: Select controls based on categorization
Map the appropriate FedRAMP baseline to your system based on its FIPS 199 categorization. These are tailored overlays of NIST SP 800-53 Rev. 5 security controls.
If you rely on other FedRAMP-authorized IaaS, PaaS, or other shared services, you should evaluate inheritance opportunities. When a service has already implemented controls that meet FedRAMP requirements, you can reuse them and reduce the time, costs, and scope of compliance.
However, you must document which controls are inherited and include evidence. Additionally, you’ll also document how each in-scope asset is covered by one or more assigned controls for faster authorization audits.
Step 3: Implement and document the controls
Implement the relevant controls across in-scope assets. You’ll want to assign a team or task owner to review each control and confirm it’s properly applied, configured, and operates as intended.
Document all implementation details in your System Security Plan (SSP) and supporting artifacts, including:
- Policies
- Procedures
- Architecture diagrams
- Control Implementation Summary (CIS)
- Customer Responsibility Matrix (CRM)
- Evidence of automated monitoring
It’s a good practice to keep your records organized and easily accessible here. Incomplete or missing documentation can lead to delays in the assessment, require extensive remediation work, and increase the overall effort and costs of obtaining your FedRAMP ATO.
Step 4: Engage a 3PAO to conduct a readiness assessment
Next, engage an accredited Third-Party Assessment Organization (3PAO) for an assessment. Before the formal audit, most CSPs undergo a Readiness Assessment to evaluate control implementation maturity and identify gaps. The results are captured in a Readiness Assessment Report (RAR).
Although not mandatory, the RAR is strongly recommended because it helps CSPs proactively address weaknesses before the full assessment and initiate remediation.
Once remediation is complete, the 3PAO will conduct a formal assessment, after which they’ll write a Security Assessment Report (SAR). This document details the results of the assessment and serves as the main reference supporting your ATO.
The RAR (if applicable), the SAR, and the SSP also form the core of the documentation package you’ll submit in the next step.
Step 5: Submit documentation for review
After passing the 3PAO assessment, you need to submit your documentation package to a sponsoring federal agency. The agency’s authorization officer (AO) then conducts a review of your system’s documentation, including the SAR, RAR, SSP, and other supporting artifacts to determine whether you meet FedRAMP requirements.
If the AO determines your controls are sufficient, you’ll be issued an ATO. You’ll then upload your FedRAMP Initial Authorization Package Checklist and the package to FedRAMP’s secure repository.
Sponsoring agencies use ATO issuance to effectively enforce FedRAMP compliance. CSPs that haven’t obtained an ATO can’t provide services to federal agencies.
Important updates (2025):
- As of late 2025, the previous authorization paths, Joint Authorization Board (JAB) and its Provisional ATO (P-ATO) authorization path, have been discontinued and replaced by a single ‘FedRAMP Authorized’ model governed by the FedRAMP Board.
- The agency-sponsored authorization process is now the primary path for achieving FedRAMP Authorization.
- The FedRAMP 20x pilot is testing a more automated and streamlined authorization approach in which upfront agency sponsorship is not required, though agency involvement remains a necessary part of the overall authorization process.
Step 6: Continuously monitor
Even after obtaining an ATO, you’ll still need to invest in Continuous Monitoring (ConMon) to oversee the effectiveness of your controls. This will require several key activities, including:
- Establishing a continuous monitoring team
- Conducting regular vulnerability scans
- Developing and updating a Plan of Action and Milestones (POA&M) under FedRAMP
- Creating an incident response plan
Plan a workflow to submit potential remediation actions, POA&M updates, and vulnerability test results to your sponsoring organization’s AO at a set cadence, typically every month. Significant changes to your system environment may trigger additional testing or require reauthorization.
Common FedRAMP compliance challenges
Meeting FedRAMP’s stringent security requirements can be challenging because of process hiccups and roadblocks, such as:
- High resource and staffing costs: Even at lower-impact levels, pursuing FedRAMP compliance requires significant investments in resources, staffing, and internal expertise. This can be a bigger conflict for startups and resource-constrained organizations.
- Comprehensive control implementation and documentation: FedRAMP requires more than just ticking off a list of controls. It can be tricky to document all process aspects, including control implementation, status of inherited controls, and vulnerabilities addressed ongoingly to support ConMon.
- Regular reviews and updates: Organizations must regularly review their FedRAMP documentation and controls, submit evidence at a set cadence, as well as undergo annual assessments, or risk losing their authorization.
- Ongoing continuous monitoring with reporting requirements: FedRAMP places a strong emphasis on continuous monitoring and monthly/quarterly reporting. This can put significant pressure on compliance teams and pull them away from day-to-day operations.
FedRAMP has complex expectations that can challenge even experienced teams. That’s why you need an automated system that helps identify compliance gaps and provide context on risk mitigation and prioritization. For instance, an agentic trust platform like Vanta can streamline evidence collection, gain real-time visibility into your control status, and enable inheritance mapping across systems.
Streamline FedRAMP compliance with Vanta
Vanta offers a unified system to help organizations meet their governance and compliance goals using agentic workflows, continuous monitoring, and centralized visibility.
The platform gives you a dedicated suite for FedRAMP compliance, helping you obtain an authorization through knowledge resources, documentation, and clear guidance. Vanta breaks down the framework’s complex requirements into clear, actionable steps for your impact tier, freeing up significant time and resources for your team.
You can scale a faster path to getting an ATO with features like:
- Automated evidence collection through 400+ integrations
- Vendor risk management tools to secure your supply chain
- Pre-built, auditor-approved policies mapped to FedRAMP baselines
- Ongoing monitoring with security reports
- AI-powered FedRAMP policy creation and customization
- A centralized dashboard to monitor your compliance status
You can use Vanta’s partner network to find trustworthy 3PAOs that meet your organizational needs and can guide you every step of the way.
Book a personalized Vanta demo to experience the FedRAMP compliance features in action.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
FAQs
Is FedRAMP a framework?
FedRAMP is a federal authorization program built on a NIST security framework. It establishes a standardized approach to assessing, authorizing, and continuously monitoring data security practices for cloud service providers that work with U.S. federal agencies.
What is an Authority to Operate (ATO)?
An ATO is a formal risk-based decision issued by a federal agency's AO that states that a cloud service meets FedRAMP security criteria and is authorized to handle federal data.
What internal roles and headcount are needed to run a FedRAMP program?
Successfully running a FedRAMP program requires a cross-functional team. This includes a compliance lead, security and control owners, documentation specialists, IT/cloud engineers, and a project coordinator. The exact headcount of your team should scale based on your organization’s impact level.
What is the relationship between FedRAMP and NIST?
FedRAMP tailors the security standards developed by NIST, particularly NIST SP 800-53 Rev. 5 and FIPS 199 impact tiers. It adapts the requirements listed in NIST 800-53 to the cloud environment, detailing how CSPs should implement, evaluate, and monitor data safeguards.
What is the relationship between FedRAMP and the Federal Information Security Modernization Act (FISMA)?
FISMA requires federal agencies to protect federal information systems using NIST-based risk management practices. For cloud systems, the FedRAMP Authorization Act designates FedRAMP as the standardized approach agencies must use to meet their FISMA obligations.
In short: FISMA sets the security law; FedRAMP provides the cloud-specific implementation.
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
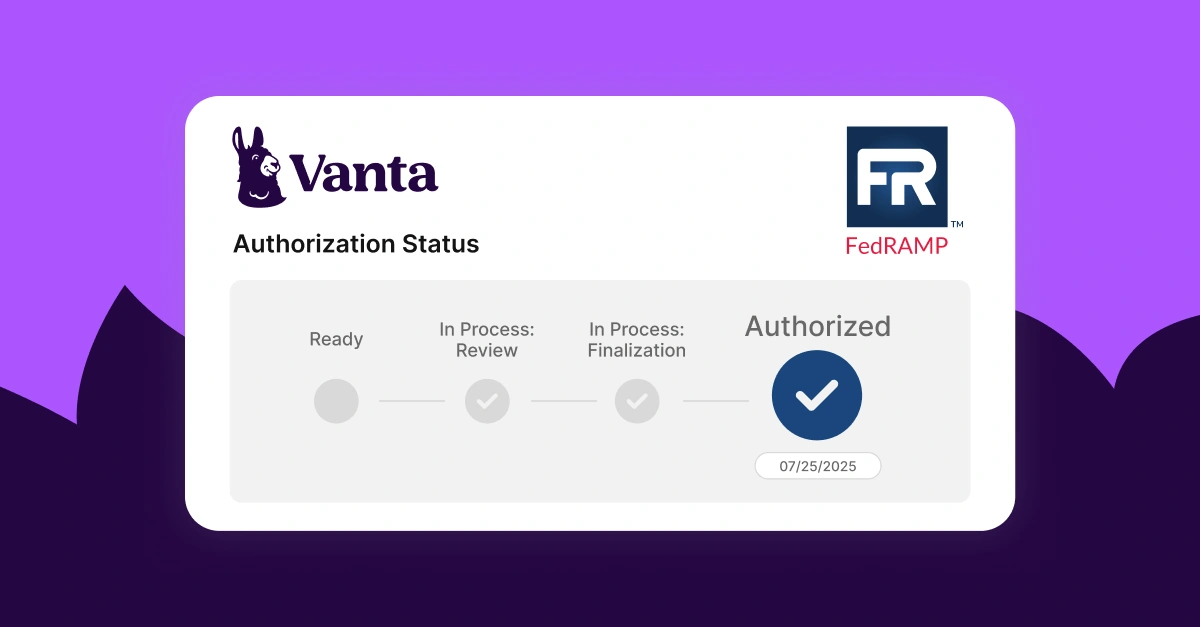
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




