FedRAMP requirements
Continuous monitoring expectations after FedRAMP authorization: All you need to know

FedRAMP requirements
Looking to streamline the work for FedRAMP compliance?
The Federal Risk and Authorization Management Program (FedRAMP) is a pivotal data security program that authorizes cloud systems that are mature enough to serve government agencies. Due to the sensitive nature of federal data, FedRAMP also mandates ongoing monitoring after authorization is granted.
Continuous monitoring under the FedRAMP aims to limit control drift and address emerging vulnerabilities. It’s an elaborate process, and without a structured approach, Cloud Service Providers (CSPs) can struggle to meet maintenance and reporting requirements, which puts their authorization at risk.
This guide breaks down what’s expected for continuous monitoring and how to approach it effectively through six practical steps.
What does FedRAMP continuous monitoring entail?
Continuous monitoring (ConMon) is a core FedRAMP authorization requirement across all baselines (Low, LI-SaaS, Moderate, and High). It requires CSPs to provide ongoing visibility into the security posture of in-scope systems, address control gaps and any new risks, track and document remediation processes, and maintain reporting timelines.
After authorization, CSPs submit Continuous Monitoring (ConMon) artifacts to their sponsoring agency’s Authorizing Official (AO) at the required cadence. As additional federal agencies adopt the same authorized service, CSPs can transition to a Collaborative Continuous Monitoring (CCM) approach under FedRAMP Rev. 5, coordinating ongoing reporting across agencies to reduce duplication while maintaining consistent visibility into system risk.
To implement continuous monitoring, follow these practices recommended under FedRAMP:
- Define a continuous monitoring strategy: Based on your risk tolerance and FedRAMP impact level priorities, develop a ConMon strategy that provides clear visibility into your assets, identifies vulnerabilities, and incorporates current threat information.
- Establish metrics: Set metrics, assessment methods, and reporting frequencies that help detect shifts from your baseline security posture. The goal is to track changes in systems and operational environments as well as maintain operations at an acceptable risk level.
- Implement a continuous monitoring program: Operationalize your ConMon program by setting up task owners and workflows for data collection and reporting. You can use automation where possible, more commonly with tasks like streamlining evidence collection and reporting metrics.
- Analyze data and report findings: Analyze monitoring data to identify vulnerabilities, control deficiencies, and deviations from the authorized baseline. Document findings clearly, including severity, scope, and impact, and collect additional evidence where needed to validate results or clarify risk.
- Respond to vulnerabilities and findings: Take timely action on identified vulnerabilities and findings by determining whether to remediate, mitigate, or formally accept risk in accordance with FedRAMP requirements. Track remediation activities and timelines in the POA&M, report security incidents within FedRAMP- or agency-defined timelines, and update core artifacts—such as the SSP and POA&M—to reflect remediation actions, risk decisions, and system changes.
- Review and update: Continuously refine the program to enhance control effectiveness, adapt to system changes, and improve organizational resilience.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
Consequences of failing FedRAMP’s ConMon requirements
Each agency AO will define compliance management deficiency triggers—events that indicate a lapse in security controls or failure to meet the FedRAMP ConMon obligations. Common triggers include incomplete documentation, missed reporting window, or an outdated POA&M.
Once a deficiency is identified, the AO may initiate corrective actions via four tiers of escalation.
The escalation itself is an agency-led process. Typically, when a ConMon deficiency is identified, the AO evaluates the issue, taking into account the CSP’s past ConMon performance, and decides whether to:
- Monitor the deficiency
- Increase the current escalation level
- Put the escalation in motion immediately
The CSP is notified about the deficiency and the escalation level. Higher escalation levels require a formal remediation package, including root cause analysis and a corrective action plan.
6 core continuous monitoring responsibilities in FedRAMP
Engage with the following core ConMon activities for sustained FedRAMP authorization:
- Establishing a continuous monitoring team
- Vulnerability scanning and remediation
- Developing and managing a POA&M
- Implementing change control
- Executing incident response
- Reporting and documentation
1. Establishing a continuous monitoring team
Form a core GRC team that will be responsible for managing FedRAMP monitoring activities. These members will navigate communication and liaison with the 3PAO and AOs, so that you have clear and timely coordination. Their responsibilities will also include engagement with the FedRAMP PMO and CISA on incident response and reporting obligations.
Vanta offers tools to support your FedRAMP continuous monitoring program—helping reduce manual effort, lower reporting overhead, and make it easier to track and manage program actions over time.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
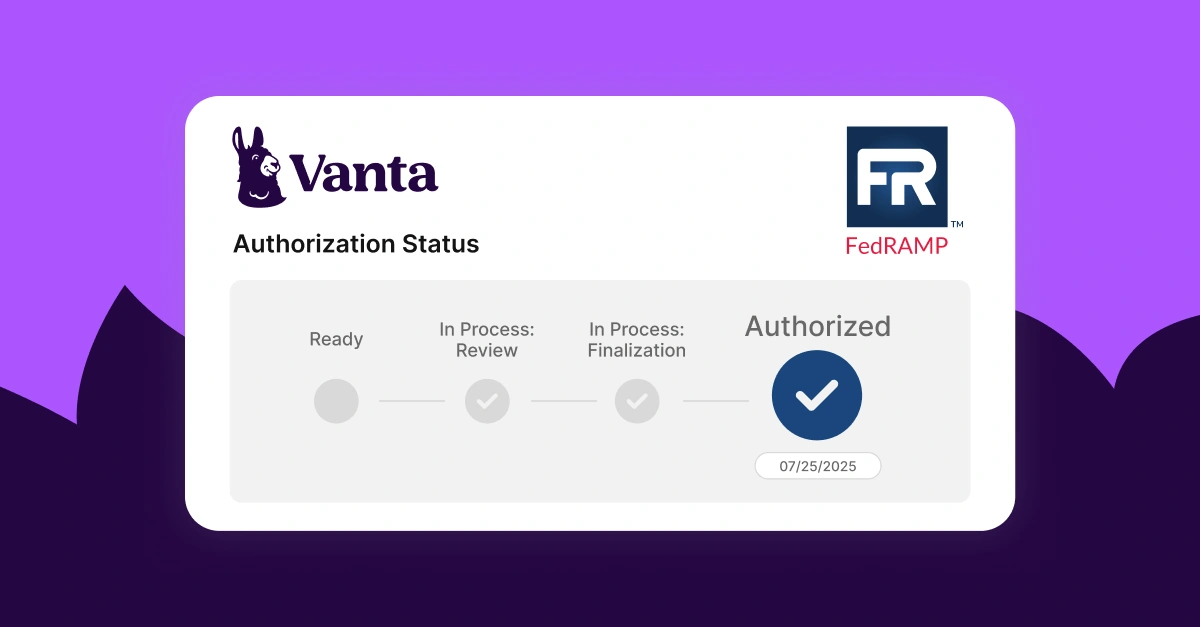
Streamline FedRAMP continuous monitoring with Vanta
Vanta is an agentic trust platform built for compliance, governance, and risk management—with capabilities designed to support FedRAMP readiness and select continuous monitoring activities. By centralizing trust management workflows in one unified platform, Vanta helps teams stay organized and prepared throughout the FedRAMP lifecycle.
Vanta can support your continuous monitoring preparation through automated tests and endpoint monitoring via 400+ integrations. Teams can also leverage Vanta to help streamline vulnerability scanning workflows and centralize POA&M tracking—making it easier to stay on top of reporting and prepare for annual reassessment. When remediation becomes available for a tracked vulnerability, Vanta can automatically reopen the item to keep your program current.
Other helpful features include:
- A centralized dashboard for managing everything FedRAMP
- Automated evidence collection
- Vendor/third-party risk management
- Instant alerts for new vulnerabilities or configuration gaps
- AI policy management feature
- Access to Vanta’s partner network to find vetted professionals for consultations and assessments
Schedule a custom demo to watch Vanta’s FedRAMP functionalities in action.
{{cta_simple39="/cta-blocks"}} | FedRAMP product page
FAQs
How often do we need to submit ConMon packages?
The frequency for submitting ConMon packages depends on what the AO and the CSP have agreed upon via the service level agreement (SLA). Typically, the packages are submitted monthly.
Can you automate ConMon reporting?
Yes, you can automate ConMon reporting with an automation platform like Vanta, which offers report generation and documentation collection features.
Who is responsible for maintaining the POA&M for continuous monitoring?
The CSP owns POA&M management under FedRAMP and is responsible for maintaining, updating, and submitting it to the agency AO as part of continuous monitoring.
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




