Introduction to FedRAMP
FedRAMP 20x explained: New goals, challenges, and readiness steps

Introduction to FedRAMP
Looking to streamline the work for FedRAMP compliance?

The US government-sponsored Federal Risk and Authorization Management Program (FedRAMP) is the gold standard for securing cloud services used by federal agencies. While its stringent requirements strengthen cybersecurity, the same rigor has made FedRAMP authorization one of the most time-consuming and resource-heavy compliance obligations.
To address this, the FedRAMP PMO introduced FedRAMP 20x: the program’s most significant modernization effort to date. It’s designed to accelerate authorizations, standardize expectations across agencies, and reduce redundant work without compromising security.
In this guide, we’ll break down:
- Goals of FedRAMP 20x
- Differences between FedRAMP and FedRAMP 20x
- FedRAMP 20x compliance process
- Common challenges to expect
What is FedRAMP 20x?
Introduced in early 2025, the FedRAMP 20x is a pilot program focused on modernizing and addressing systemic bottlenecks in the traditional FedRAMP authorization process. FedRAMP 20x introduces a modernized, automation-ready authorization path that cuts manual work, speeds up reviews, and supports continuous security validation—making it easier for cloud providers to innovate and agencies to adopt secure cloud services faster.
The pilot program was originally launched with the Low impact level authorization in Phase One. As of late 2025, the FedRAMP 20x Phase Two is active and expanding to Moderate impact level authorizations and beyond.
Despite the “20x” label, FedRAMP 20x isn’t just about speed. It’s about shifting to a tech-forward and more predictable authorization path built on standardization and automation, making it a new process altogether. It also remains subject to revisions and iterations as federal agencies and CSPs test implementation and share feedback.
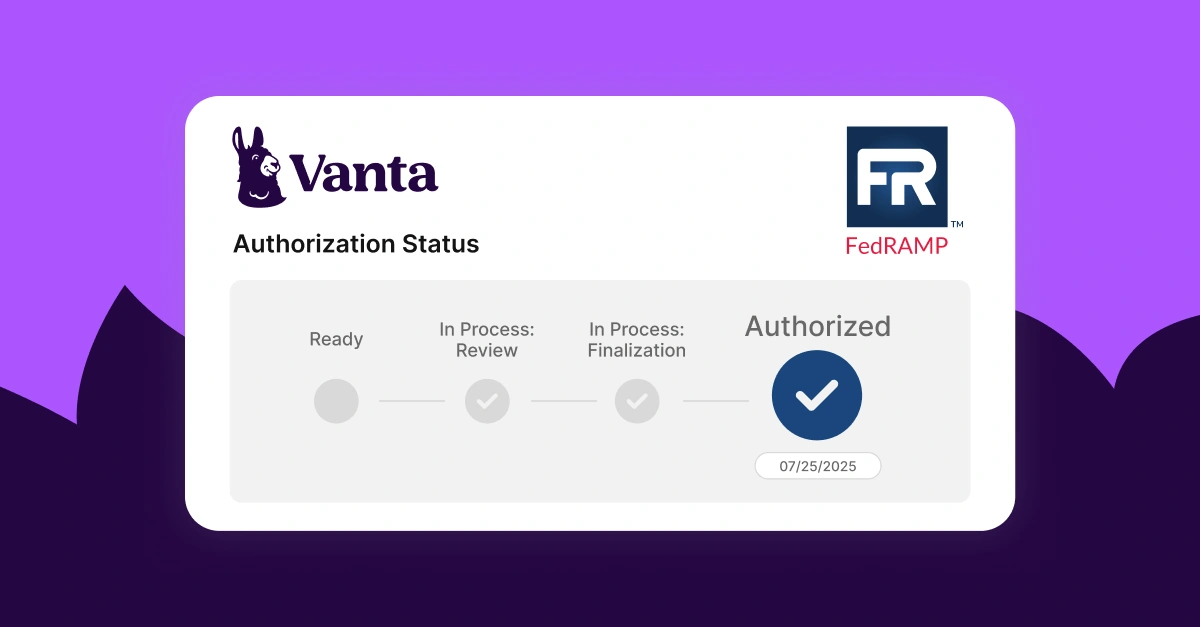
Bonus read: Explore the firsthand lessons learned from Vanta’s FedRAMP 20x pilot program.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
What are the goals of FedRAMP 20x?
FedRAMP 20x goals address the most notable pain points of the original compliance and authorization setup. There’s a focus on making federal cloud authorization more accessible, efficient, and cost-effective. This enables cloud service providers (CSPs) of all sizes to pursue authorization, which was previously mostly attainable only to large enterprises.
The overarching goal is also to leverage existing industry investments, maintain continuous security monitoring, and demonstrate security best practices—strengthening the federal trust ecosystem.
In practice, the framework’s goals translate into four key focus areas:
- Automate FedRAMP compliance
- Reduce the documentation burden
- Improve cost effectiveness
- Enable rapid improvements at scale
1. Automate FedRAMP compliance
Under the traditional FedRAMP Rev. 5 model, both implementation and authorization processes were highly manual and fragmented. Organizations often struggled to maintain anything close to real-time visibility into their compliance posture because most validation occurred during point-in-time assessments—typically once a year during the annual audit.
On the implementation side, CSPs spent substantial time preparing evidence, reviewing controls manually, and updating documentation.
On the authorization side, the path to an ATO required lengthy review cycles, static security packages, and extensive manual validation by assessors and federal agencies.
FedRAMP 20x addresses these scattered processes through automated, continuous validation that provides federal agencies with near-instant visibility into the cloud service’s security posture. Compliance expectations are expressed as machine-readable, outcome-focused Key Security Indicators (KSIs), mapped to established control outcomes, such as NIST SP 800-53 Rev. 5.
This shift enables organizations to move away from manual, point-in-time reviews and leverage automation solutions to oversee, document, and demonstrate their security posture in real time.
2. Reduce the documentation burden
Traditional FedRAMP compliance required extensive documentation, much of which was manually reviewed since artifacts varied in structure and format. Naturally, this slowed down the authorization process and increased the likelihood of inconsistencies, such as duplicate or missed evidence—even version drift.
FedRAMP 20x fundamentally shifts the compliance paradigm from static documents to data-centric validation. By operationalizing machine readable standards, such as Open Security Controls Assessment Language (OSCAL), the framework transforms requirements into machine-readable logic that supports consistent, automated assessment.
Instead of relying on static, text-heavy control narratives, CSPs increasingly report via Key Security Indicators (KSIs). These are structured, outcome-based data points that prove a control is functioning in real-time. This allows 3PAOs to rely on automated validation for the majority of controls, reserving human review for complex architectural decisions and governance logic.
To further reduce preparation time and minimize duplicate documentation, organizations may reuse existing industry investments and evidence, such as framework mappings, policy libraries, and controls. The FedRAMP PMO also plans to release standardized, customizable templates that can support the remaining documentation.
3. Improve cost effectiveness
FedRAMP 20x has potential to improve cost efficiency by shifting bulky compliance processes to streamlined, automation-assisted validations. The program’s stated goal is to compress authorization timelines from months or years down to weeks, significantly lowering the barrier to entry for commercial software vendors.
Organizations must still engage Third-Party Assessment Organizations (3PAOs), but their role has fundamentally changed. Under FedRAMP 20x, 3PAOs shift from being manual document reviewers ("Did you take a screenshot of the setting?") to Automation Validators ("Is your code correctly enforcing the setting?").
In practice, this means 3PAO engagement will start collaborating with the CSP sooner and be more technical. They’ll focus more on validating automation pipelines, verifying the accuracy of machine readable evidence, and maintaining reliable continuous monitoring processes.
The combination of 3PAO engagement, automation, and the accelerated authorization process can reduce the investment needed to achieve and maintain compliance, potentially leading to a faster recovery of ROI.
Tip: Curious how the FedRAMP 20x shift can impact your processes? Watch this free Vanta 20x webinar to enrich your knowledge.
4. Enable rapid improvements at scale
FedRAMP 20x standardizes compliance artifacts using OSCAL Component Definitions, allowing organizations to digitally map and inherit controls from authorized infrastructure (like AWS or Azure). This eliminates the need to manually re-document physical security controls, significantly reducing redundant work.
Additionally, FedRAMP 20x introduces a tiered approach to change management. While routine, low-risk updates ("Adaptive Changes") can be streamlined via Significant Change Notifications, major architectural shifts ("Transformative Changes") still require 3PAO assessment and validation.
This hybrid model allows for rapid DevOps speed where it’s safe, while maintaining rigorous oversight for critical updates. By leveraging Persistent Validation (e.g., Key Security Indicators [KSIs]), organizations can prove that routine changes haven't degraded their security posture, reducing the frequency of "stop-and-wait" audit cycles.
Preparing for FedRAMP 20x compliance
The authorization process for FedRAMP 20x is largely similar to traditional FedRAMP, but with a greater emphasis on real-time security and continuous monitoring.
Here’s what the FedRAMP 20x-supported authorization process looks like:
- Confirm FedRAMP Impact Level (FIPS 199): You must categorize your system based on the potential impact to Confidentiality, Integrity, and Availability (the CIA Triad). Use the findings to determine if you must pursue FedRAMP Low, Moderate, or High.
- Note: High-impact systems aren’t eligible for the 20x path as of 2025.
- Define the Minimum Assessment Scope: Conduct internal audits to identify which systems, data, and services fall in your FedRAMP boundary
- Implement controls and map to KSIs: Configure your product to meet FedRAMP KSIs, and set up the system to automatically prove its security status.
- Create a machine-readable package: Use your compliance tools to convert your system’s security data into machine readable format.
- Validate with a 3PAO: Engage a Third-Party Assessment Organization (3PAO) to review your package. In FedRAMP 20x, the 3PAO validates your automation logic and KSIs to ensure they accurately report your security status in real-time.
- Submit for authorization: Submit your validated machine-readable package to the FedRAMP PMO. Because the data is structured, the PMO can validate your security outcomes significantly faster than traditional manual reviews.
- Obtain authorization and continuously monitor: Once authorized, sustain compliance through continuous monitoring and regular updates to documentation and controls.
Note: Due to the pilot nature of the program, FedRAMP 20x authorizations are currently issued for only 12 months.
{{cta_withimage44="/cta-blocks"}} | FedRAMP checklist
FedRAMP 20x vs FedRAMP
Because FedRAMP 20x is an automated variation of FedRAMP, the shift greatly transforms your workflows—giving rise to numerous differences. Notably, FedRAMP 20x articulates expectations as KSIs designed for automated, outcome-based control validation rather than relying solely on the traditional, elaborate control-by-control evidence.
Other key differences are presented in the table below:
Challenges of FedRAMP 20x compliance
Although FedRAMP 20x aims to streamline the authorization process, aligning with the still-evolving requirements comes with challenges. Those include:
- Lack of fully prescriptive guidance during the pilot: KSIs are outcome-based and don’t require specific documentation. Without prescriptive guidance, organizations must interpret how to meet them or how to map legacy controls to the new model.
- New compliance expectations: FedRAMP 20x moves away from periodic reviews and reporting to a continuous monitoring approach. Organizations may face process friction as they adapt existing review cadence, reporting procedures, and control maintenance.
- Tooling changes: FedRAMP 20x emphasizes the use of OSCAL and machine-readable evidence. Some teams could face a knowledge gap as they explore such technical and automation-heavy workflows. That said, embracing a continuous assurance approach can be a significant expertise boost for compliance teams.
Early collaboration with FedRAMP advisors and 3PAOs, as well as investing in data automation, can help navigate these challenges more efficiently. An effective solution is to leverage dedicated FedRAMP 20x software like Vanta to streamline the transition with native workflow automation, guidance, and access to industry experts.
Adapt to FedRAMP 20x compliance with Vanta
Vanta is an agentic trust platform that helps you achieve FedRAMP authorization in a more organized and guided way with built-in resources, automation, templates, and documentation management. The platform gives you a centralized system with agentic workflows, continuous monitoring, and unified visibility, which can help you align with FedRAMP, FedRAMP 20x, and 35+ other frameworks and standards faster.
If you’re pursuing FedRAMP 20x, Vanta can support you with:
- Real-time monitoring aligned to KSIs
- AI-guided policy reviews and workflow guidance
- Continuous monitoring for both FedRAMP 20x Low and Moderate
Vanta participated in the FedRAMP 20x pilot, and you can check the team’s firsthand findings in this FedRAMP® 20x Pilot webinar.
If you’re pursuing traditional FedRAMP certification, Vanta’s FedRAMP product enables you to approach authorization confidently with features like 1,200+ automated tests, 400+ integrations for evidence management, and pre-built policy templates. You can also tap into Vanta’s partner network to find compliance experts relevant to you.
Schedule a personalized demo to explore Vanta’s capabilities for FedRAMP compliance.
{{cta_simple39=”/cta-blocks”}} | FedRAMP product page
FAQs
Is FedRAMP 20x mandatory for federal agencies or CSPs?
FedRAMP 20x is not yet mandatory, but the clock is ticking. Currently, FedRAMP 20x is an optional alternative path (Pilot Phase). It's scheduled to become the mandatory standard for all new authorizations by early 2027, with a full sunset of the legacy Rev. 5 process targeted for late 2027.
What’s the 20x authorization timeline compared to standard FedRAMP?
FedRAMP 20x aims to substantially reduce the traditional 12–18+ month FedRAMP authorization timeline through automation, standardized data exchange, and continuous oversight. The stated goal of FedRAMP 20x is to achieve authorization in weeks.
How should I plan resources differently for 20x versus traditional FedRAMP?
Anticipate a larger shift towards automation and digital workflows with FedRAMP 20x. You’ll have to keep allocating resources for internal control implementation, continuous monitoring, and 3PAO assessments, but maintain some flexible capacity for the tooling shift and the iteration cycle with your 3PAO.
Explore more FedRAMP articles
Introduction to FedRAMP
FedRAMP levels
FedRAMP requirements
Get started with FedRAMP:
Start your FedRAMP journey with these related resources.

FedRAMP Authorization Checklist
Here’s the step-by-step process to achieve FedRAMP authorization for the first time.

The ultimate guide to FedRAMP: A requirements guide for authorization
Learn about FedRAMP authorization, from impact levels to compliance steps, to unlock opportunities with U.S. federal agencies.
Lessons learned from Vanta’s FedRAMP® 20x pilot program
A behind-the-scenes look at how Vanta navigated the FedRAMP 20x pilot.




